570 CHAPTER 26: ROGUE DETECTION AND COUNTERMEASURES
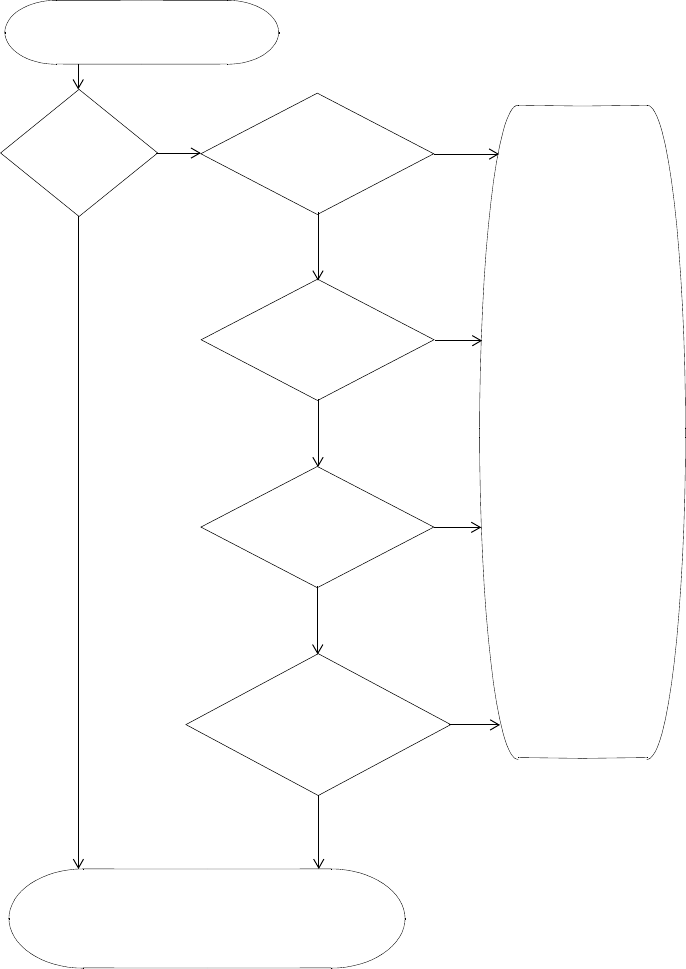
Figure 34 Rogue Detection Algorithm
MAP radio detects wireless packet.
No
Yes
Yes
Source MAC in
SSID in Permitted
Ignore List?
Device is not a threat.
SSID List?
Yes
OUI in Permitted
Vendor List?
No
Source MAC in
Attack List?
No
Generate an alarm.
Classify device as a rogue.
No
Yes
Issue countermeasures
(if enabled).
No
Rogue classification
Yes
algorithm deems the
device to be a rogue?


















