VoIP/(802.11g) ADSL2+ (VPN) Firewall Router
Chapter 4: Configuration
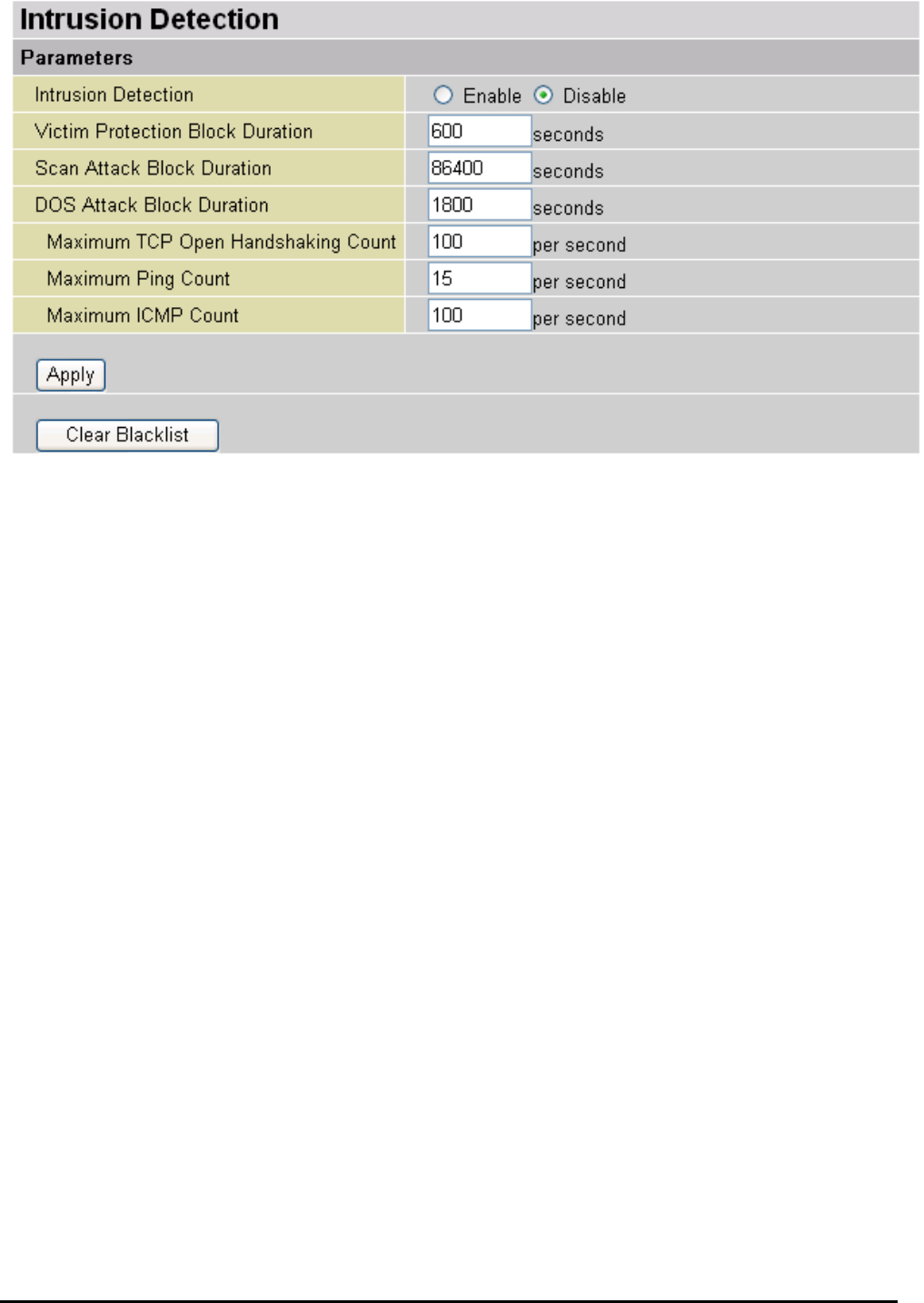
Intrusion Detection
The router’s Intrusion Detection System (IDS) is used to detect hacker attacks and intrusion attempts
from the Internet. If the IDS function of the firewall is enabled, inbound packets are filtered and blocked
depending on whether they are detected as possible hacker attacks, intrusion attempts or other
connections that the router determines to be suspicious.
Blacklist: If the router detects a possible attack, the source IP or destination IP address will be added to
the Blacklist. Any further attempts using this IP address will be blocked for the time period specified as the
Block Duration. The default setting for this function is false (disabled). Some attack types are denied
immediately without using the Blacklist function, such as Land attack and Echo/CharGen scan.
Intrusion Detection: If enabled, IDS will block Smurf attack attempts. Default is false.
Block Duration:
Victim Protection Block Duration: This is the duration for blocking Smurf attacks. Default
value is 600 seconds.
Scan Attack Block Duration: This is the duration for blocking hosts that attempt a possible
Scan attack. Scan attack types include X’mas scan, IMAP SYN/FIN scan and similar attempts.
Default value is 86400 seconds.
DoS Attack Block Duration: This is the duration for blocking hosts that attempt a possible
Denial of Service (DoS) attack. Possible DoS attacks this attempts to block include Ascend Kill and
WinNuke. Default value is 1800 seconds.
Max TCP Open Handshaking Count: This is a threshold value to decide whether a SYN Flood attempt
is occurring or not. Default value is 100 TCP SYN per seconds.
Max PING Count: This is a threshold value to decide whether an ICMP Echo Storm is occurring or not.
Default value is 15 ICMP Echo Requests (PING) per second.
Max ICMP Count: This is a threshold to decide whether an ICMP flood is occurring or not. Default value
is 100 ICMP packets per seconds except ICMP Echo Requests (PING).
For SYN Flood, ICMP Echo Storm and ICMP flood, IDS will just warn the user in the Event Log. It cannot
protect against such attacks.
68


















