CONSTELLATION ES SERIAL ATA PRODUCT MANUAL, REV. F 26
4.0 ABOUT FIPS
The Federal Information Processing Standard (FIPS) Publication 140-2 is a U.S. Government Computer Security Standard used to
accredit cryptographic modules. It is titled 'Security Requirements for Cryptographic Modules (FIPS PUB 140-2)' and is issued by the
National Institute of Standards and Technology (NIST).
Purpose
This standard specifies the security requirements that will be satisfied by a cryptographic module utilized within a security system
protecting sensitive but unclassified information. The standard provides four increasing, qualitative levels of security: Level 1, Level 2,
Level 3 and Level 4. These levels are intended to cover the wide range of potential applications and environments in which cryptographic
modules may be employed.
Seagate Enterprise SEDs
The SEDs referenced in this Product Manual have been validated by CMVP and have been thoroughly tested by a NVLAP accredited lab
to satisfy FIPS 140-2 Level 2 requirements. In order to operate in FIPS Approved Mode of Operation, these SEDs require security
initialization. For more information, refer to 'Security Rules' section in the 'Security Policy' document uploaded on the NIST website. To
reference the product certification visit -
http://csrc.nist.gov/groups/STM/cmvp/documents/140-1/1401vend.htm and search for "Seagate".
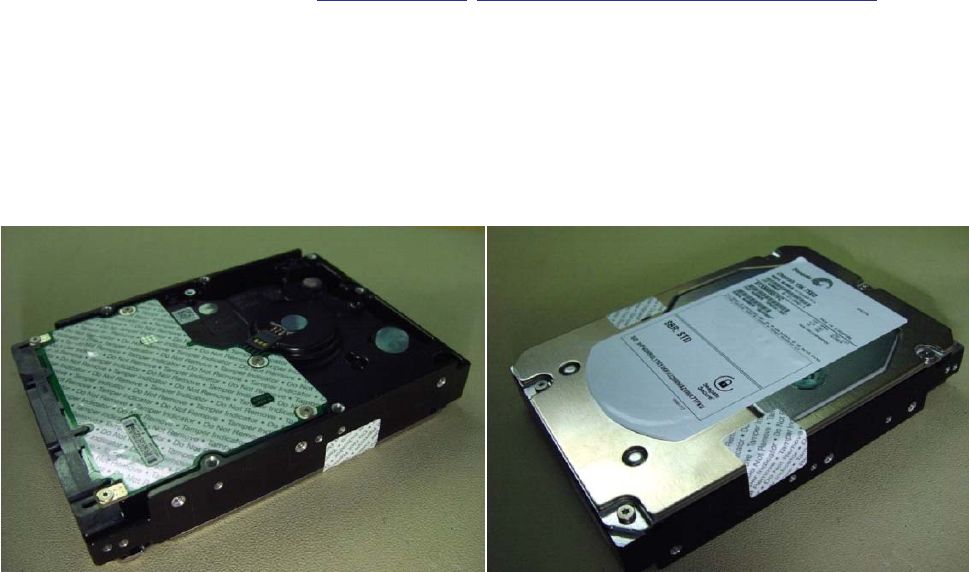
Level 2 security
Security Level 2 enhances the physical security mechanisms of a Security Level 1 cryptographic module by adding the requirement for
tamper-evidence, which includes the use of tamper-evident coatings or seals on removable covers of the module. Tamper-evident coatings
or seals are placed on a cryptographic module so that the coating or seal must be broken to attain physical access to the critical security
parameters (CSP) within the module. Tamper-evident seals are placed on covers to protect against unauthorized physical access. In
addition Security Level 2 requires, at a minimum, role-based authentication in which a cryptographic module authenticates the
authorization of an operator to assume a specific role and perform a corresponding set of services.
Figure 7. Example of FIPS tamper evidence labels.
Note. Does not represent actual drive.


















