37-16
Catalyst 3750-X and 3560-X Switch Software Configuration Guide
OL-21521-01
Chapter 37 Configuring Network Security with ACLs
Configuring IPv4 ACLs
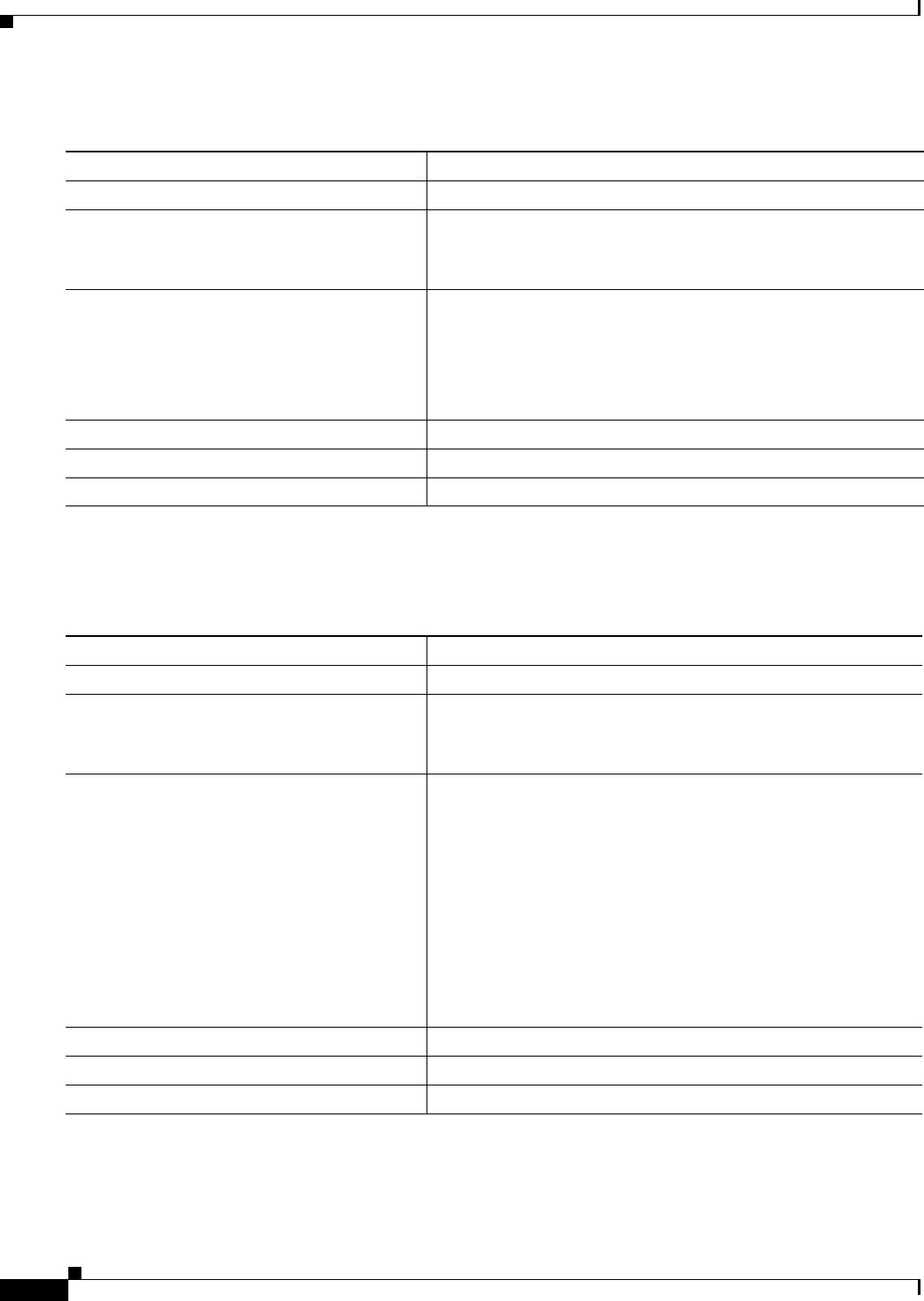
Beginning in privileged EXEC mode, follow these steps to create a standard ACL using names:
To remove a named standard ACL, use the no ip acces
s-list standard name global configuration
command.
Beginning in privileged EXEC mode, follow these steps to create an extended ACL using names:
To remove a named extended ACL, use the no ip acc
ess-list extended name global configuration
command.
Command Purpose
Step 1
configure terminal Enter global configuration mode.
Step 2
ip access-list standard name Define a standard IPv4 access list using a name, and enter
access-list configuration mode.
The name can be a number fr
om 1 to 99.
Step 3
deny {source [source-wildcard] | host source |
any} [log]
or
permit {so
urce [source-wildcard] | host source
| any} [log]
In access-list configura
tion mode, specify one or more conditions
denied or permitted to decide if the packet is forwarded or dropped.
• host source—A source and source wildcard of source 0.0.0.0.
• any—A source and source wildcard of 0.0.0.0
255.255.255.255.
Step 4
end Return to privileged EXEC mode.
Step 5
show access-lists [number | name] Show the access list configuration.
Step 6
copy running-config startup-config (Optional) Save your entries in the configuration file.
Command Purpose
Step 1
configure terminal Enter global configuration mode.
Step 2
ip access-list extended name Define an extended IPv4 access list using a name, and enter
access-list configuration mode.
The name can be a number from 100 to 199.
Step 3
{deny | permit} protocol {source
[source-wildcard] | host source | any}
{destination [destination-wildcard] | host
destination | any} [precedence precedence]
[tos tos] [established] [log] [time-range
time-range-name]
In access-list configuration mode, specify
the conditions allowed
or denied. Use the log keyword to get access list logging messages,
including violations.
See the “
Creating a Numbered Extended ACL” section on
page 37-11 for definitions of protocols and other keywords.
• host source—A source and source wildcard of source 0.0.0.0.
• host destination—A destination and destination wildcard of
destination 0.0.0.0.
• any—A source and source wildcard or destination and
destination wildcard of 0.0.0.0 255.255.255.255.
Step 4
end Return to privileged EXEC mode.
Step 5
show access-lists [number | name] Show the access list configuration.
Step 6
copy running-config startup-config (Optional) Save your entries in the configuration file.


















