Security: Secure Sensitive Data Management
SSD Rules
365 Cisco Small Business 300 Series Managed Switch Administration Guide
18
NOTE When doing a file transfer initiated by an XML or SNMP command, the
underlying protocol used is TFTP. Therefore, the SSD rule for insecure
channel will apply.
SSD Rules and User Authentication
SSD grants SSD permission only to authenticated and authorized users and
according to the SSD rules. A device depends on its user authentication process
to authenticate and authorize management access. To protect a device and its
data including sensitive data and SSD configurations from unauthorized access, it
is recommended that the user authentication process on a device is secured. To
secure the user authentication process, you can use the local authentication
database, as well as secure the communication through external authentication
servers, such as RADIUS and TACACS servers. The configuration of the secure
communication to the external authentication servers are sensitive data and are
protected under SSD.
NOTE The user credential in the local authenticated database is already protected by a
non SSD related mechanism
If a user from a channel issues an action that uses an alternate channel, the device
applies the read permission and default read mode from the SSD rule that match
the user credential and the alternate channel. For example, if a user logs in via a
secure channel and starts a TFTP upload session, the SSD read permission of the
user on the insecure channel (TFTP) is applied
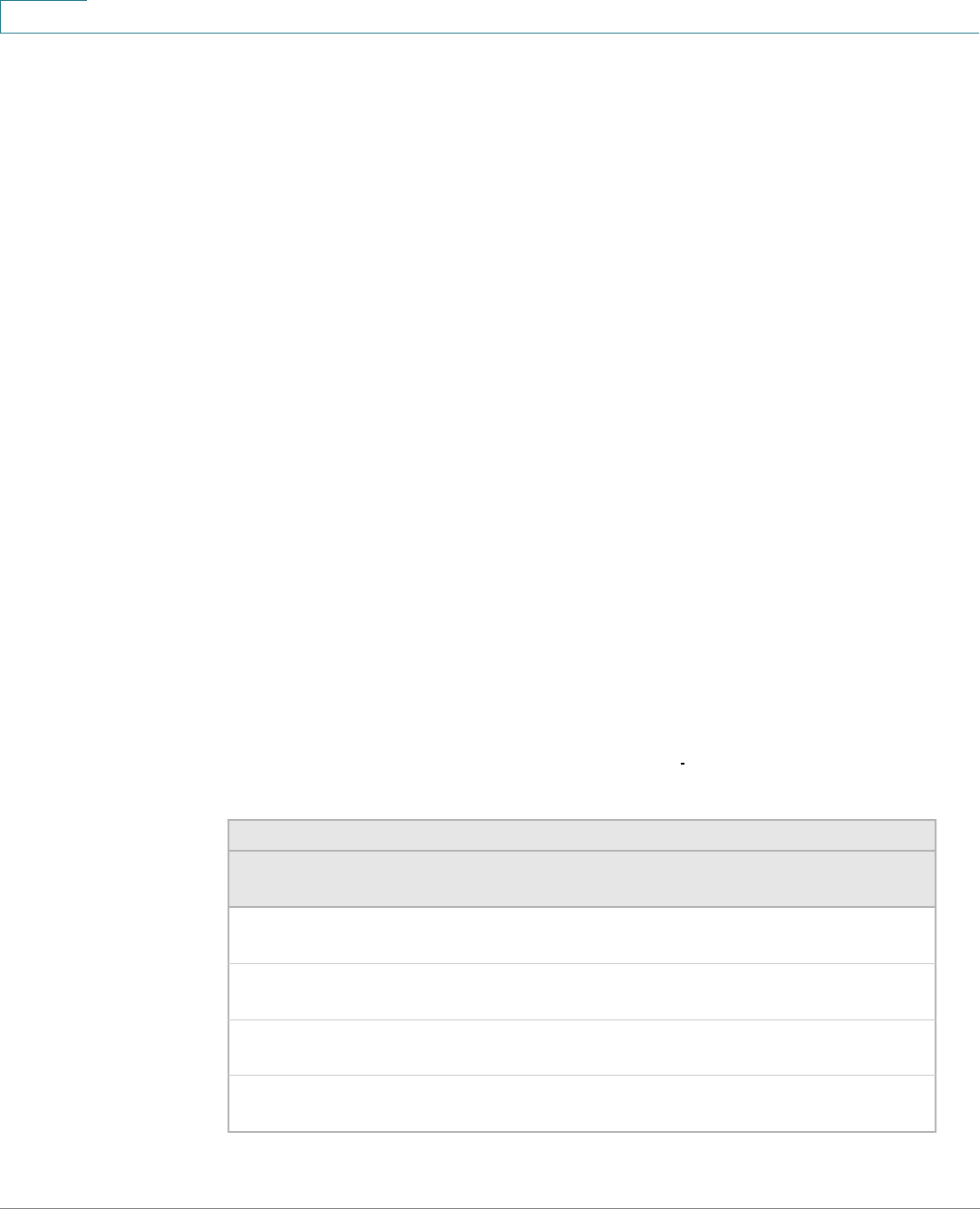
Default SSD Rules
The device has the following factory default rules:
Table 3 Default SSD Rules
Rule Key Rule Action
User Channel Read
Permission
Default Read Mode
Level
15
Secure XML
SNMP
Plaintext Only Plaintext
Level
15
Secure Both Encrypted
Level
15
Insecure Both Encrypted
All Insecure XML
SNMP
Exclude Exclude


















