42
Appendix D: virus throttle security
Virus throttle is based on the detection of anomalous behavior of network traffic that differs from a normal
activity. Under normal activity, a server will make fairly few outgoing connections to new clients or servers, but
instead, is more likely to connect regularly to the same set of end nodes. This is in contrast to the fundamental
behavior of a rapidly spreading worm, which will attempt many outgoing connections to new computers. For
example, while computers normally make approximately one connection per second, the SQL Slammer virus
tries to infect more than 800 systems per second.
Virus throttle works by intercepting IP-routed connection requests—connections crossing VLAN boundaries—in
which the source subnet and destination subnet are different. The virus throttle tracks the number of recently
made connections. If a new, intercepted request is to a destination to which a connection was recently made,
the request is processed as normal. If the request is to a destination that has not had a recent connection,
the request is processed only if the number of recent connections is below a pre-set threshold. The threshold
specifies how many connections are to be allowed over a set amount of time, thereby enforcing a connection-
rate limit. If the threshold is exceeded, because requests are coming in at an unusually high rate, it is taken
as evidence of a virus. This causes the throttle to stop processing requests and to instead notify the system
administrator.
This applies to most common Layer 4 through 7 session and application protocols, including TCP connections,
UDP packets, SMTP, IMAP, Web Proxy, HTTP, SSL, and DNS—virtually any protocol where the normal traffic
does not look like a virus spreading. For virus throttle to work, IP routing and multiple VLANs with member
ports must first be configured.
Note that some protocols, such as NetBIOS and WINS, and some applications such as network management
scanners, notification services, and P2P file sharing, are not appropriate for virus throttle. These protocols and
applications initiate a broad burst of network traffic that could be misinterpreted by the virus-throttle technology
as a threat.
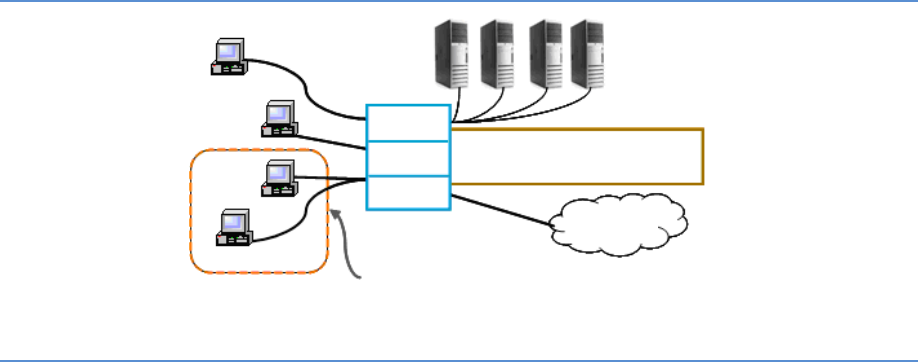
5400zl, 3500yl, or 6200yl with
IP Routing configured
Devices on VLAN 3 infected with worm-like
malicious code
VLAN 1
Intranet
Networked
servers
VLAN 2
VLAN 3
Figure D-1: Virus throttle example topology
On the ProCurve 6600 Switch Series, virus throttle is implemented through connection-rate filtering. When
connection-rate filtering is enabled on a port, the inbound routed traffic is monitored for a high rate of
connection requests from any given host on the port. If a host appears to exhibit the worm-like behavior
of attempting to establish a large number of outbound IP connections in a short period of time, the switch
responds, depending on how connection-rate filtering is configured.


















