1918
Using the Belkin Wireless Networking Utility
Using the Belkin Wireless Networking Utility
19
section
1
2
3
4
5
6
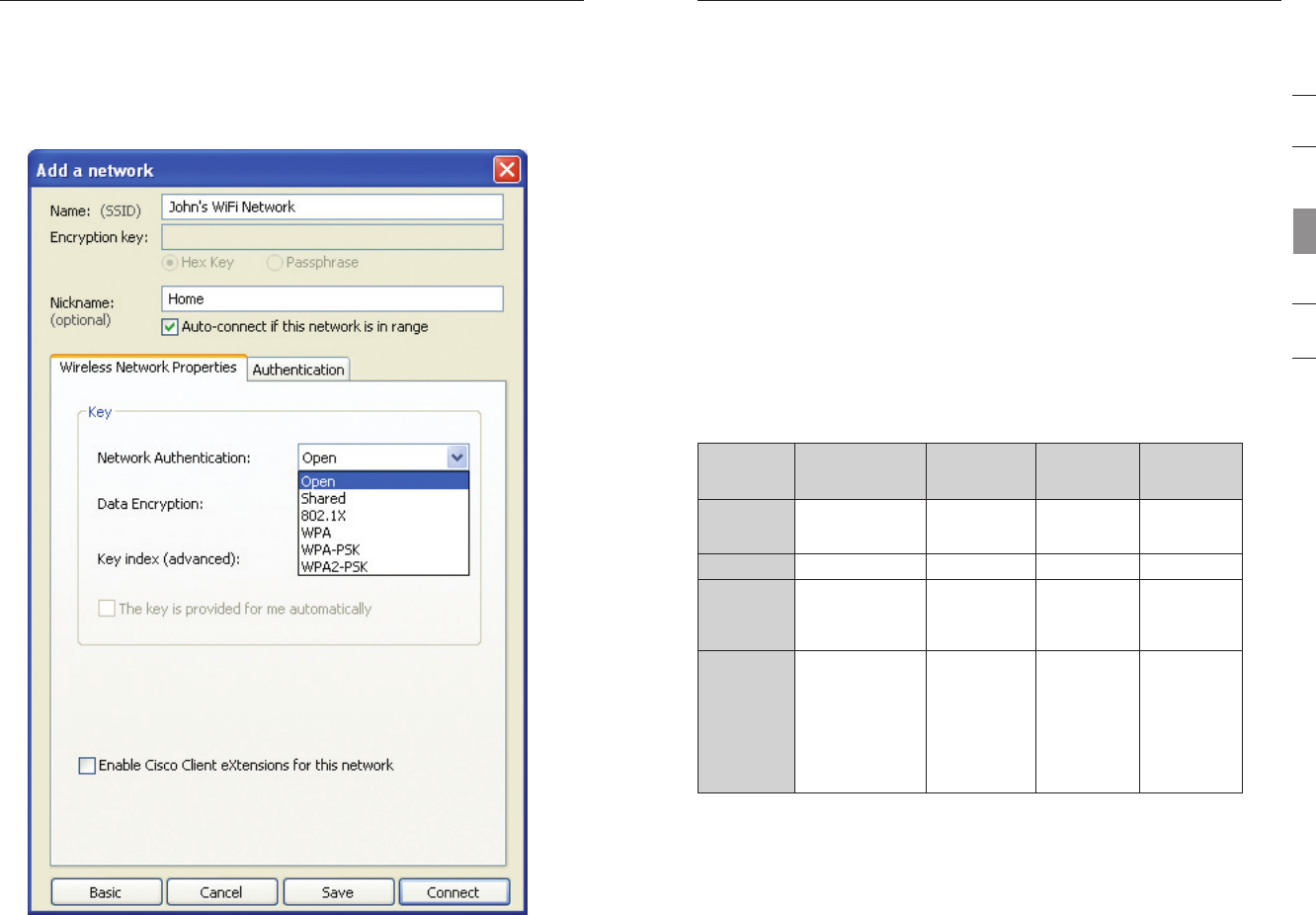
Note: When you select a network using encryption, you will first see
the simple security screen. Click the “Advanced” button to see other
security options (below).
Wired Equivalent Privacy (WEP) is a less secure, but more
widely adopted wireless security protocol. Depending on the security
level (64- or 128-bit), the user will be asked to input a 10- or 26-
character hex key. A hex key is a combination of letters, a–f, and
numbers, 0–9.
Wireless Protected Access (WPA) is the new standard in
the wireless security. However, not all wireless cards and adapters
support this technology. Please check your wireless adapter’s user
manual to check if it supports WPA. Instead of a hex key, WPA uses
only passphrases, which are much easier to remember.
The following section, intended for the home, home-office, and small-
office user, presents a few different ways to maximize the security of
your wireless network.
At the time of publication, four encryption methods are available:
Encryption Methods:
Name 64-bit Wired
Equivalent Privacy
128-bit
Encryption
Wi-Fi
Protected
Access-TKIP
Wi-Fi
Protected
Access 2
Acronym 64-bit WEP 128-bit WPA-TKIP/
AES (or just
WPA)
WPA2-AES (or
just WPA2)
Security Good Better Best Best
Features Static keys Static keys Dynamic key
encryption
and mutual
authentication
Dynamic key
encryption
and mutual
authentication
Encryption keys
based on RC4
algorithm (typically
40-bit keys)
More secure
than 64-bit
WEP using a
key length of
104 bits plus
24 additional
bits of system-
generated data
TKIP
(Temporal
Key Integrity
Protocol)
added so
that keys are
rotated and
encryption is
strengthened
AES
(Advanced
Encryption
Standard)
does not
cause any
throughput
loss
WEP
WEP is a common protocol that adds security to all Wi-Fi-compliant
wireless products. WEP gives wireless networks the equivalent level
of privacy protection as a comparable wired network.


















