FDDI Applications
3-6 Connection Policy Window
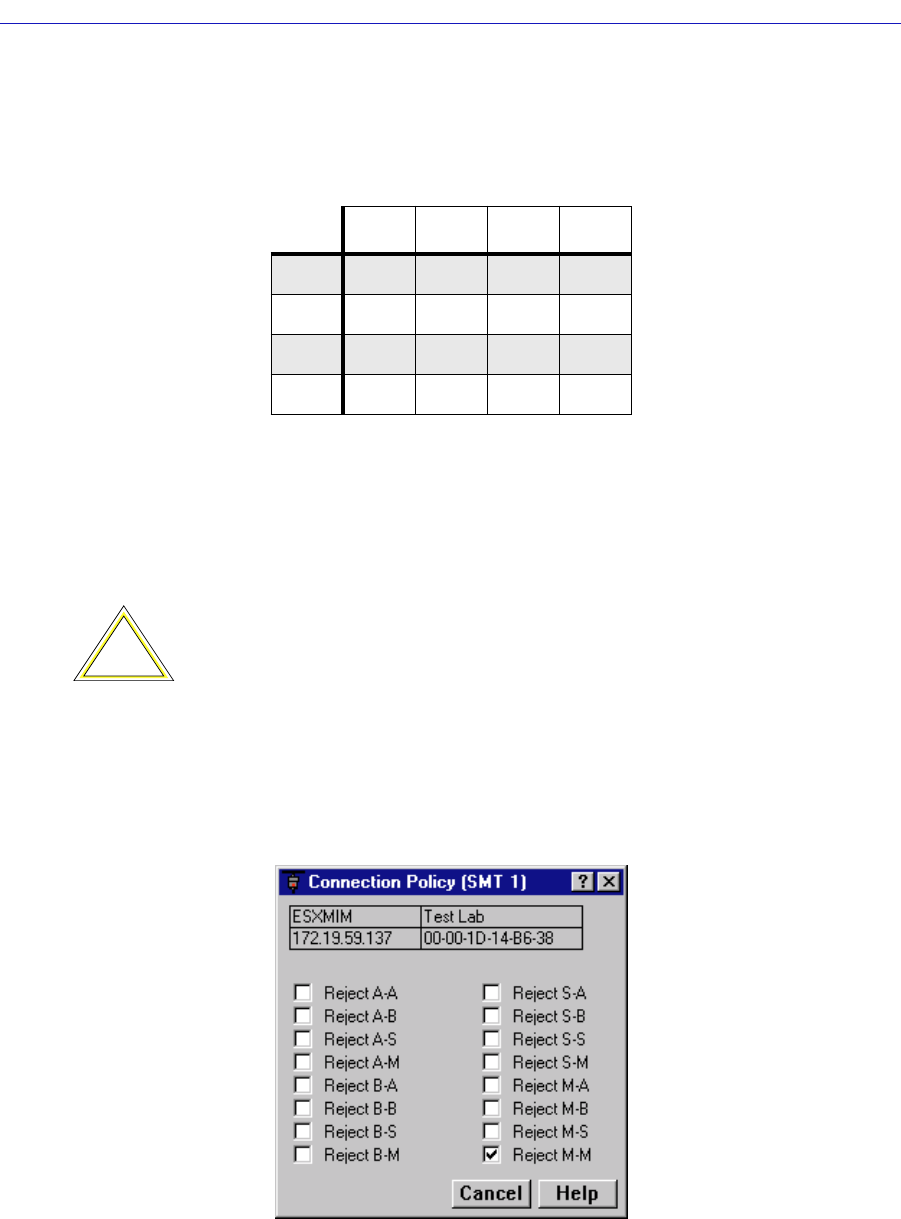
The following table summarizes the FDDI connection rules:
V – valid connection
X – illegal connection
U – undesirable (but legal) connection
P – valid, but when both A and B are connected to M ports (a dual-homing
configuration), only the B connection is used.
The Connection Policy window, Figure 3-3, lists potential connection types in a
ÒReject X-YÓ format, where X represents a port on the FDDI BRIM, and Y
represents the attaching node. A check in the checkbox next to a Connection
Policy indicates that it is an illegal connection.
Figure 3-3. The Connection Policy Window
Table 3-1. FDDI Connection Rules
ABSM
A V, U V V, U V, P
B V V, U V, U V, P
S V, U V, U V V
MVVVX
!
CAUTION
Though technically legal under FDDI connection rules, undesirable connections will
cause a twisted or wrapped ring.


















