43
Trigger: Defines the outgoing communication that determines whether the user has
legitimate access to the application.
Protocol: Select the protocol (TCP, UDP, or ICMP) that can be used to
access the application.
Port Range: Type the port range that can be used to access the application
in the text boxes.
Incoming: Defines which incoming communications users are permitted
to connect with.
Protocol: Select the protocol (TCP, UDP, or ICMP) that can be used by
the incoming communication.
Port: Type the port number that can be used for the incoming communication.
Add: Click to add the special application profile to the table at the bottom of the
screen.
Update: Click to update information for the special application if user have
selected a list item and have made changes.
Delete: Select a list item and click Delete to remove the item from the list.
New: Click “New” to erase all fields and enter new information.
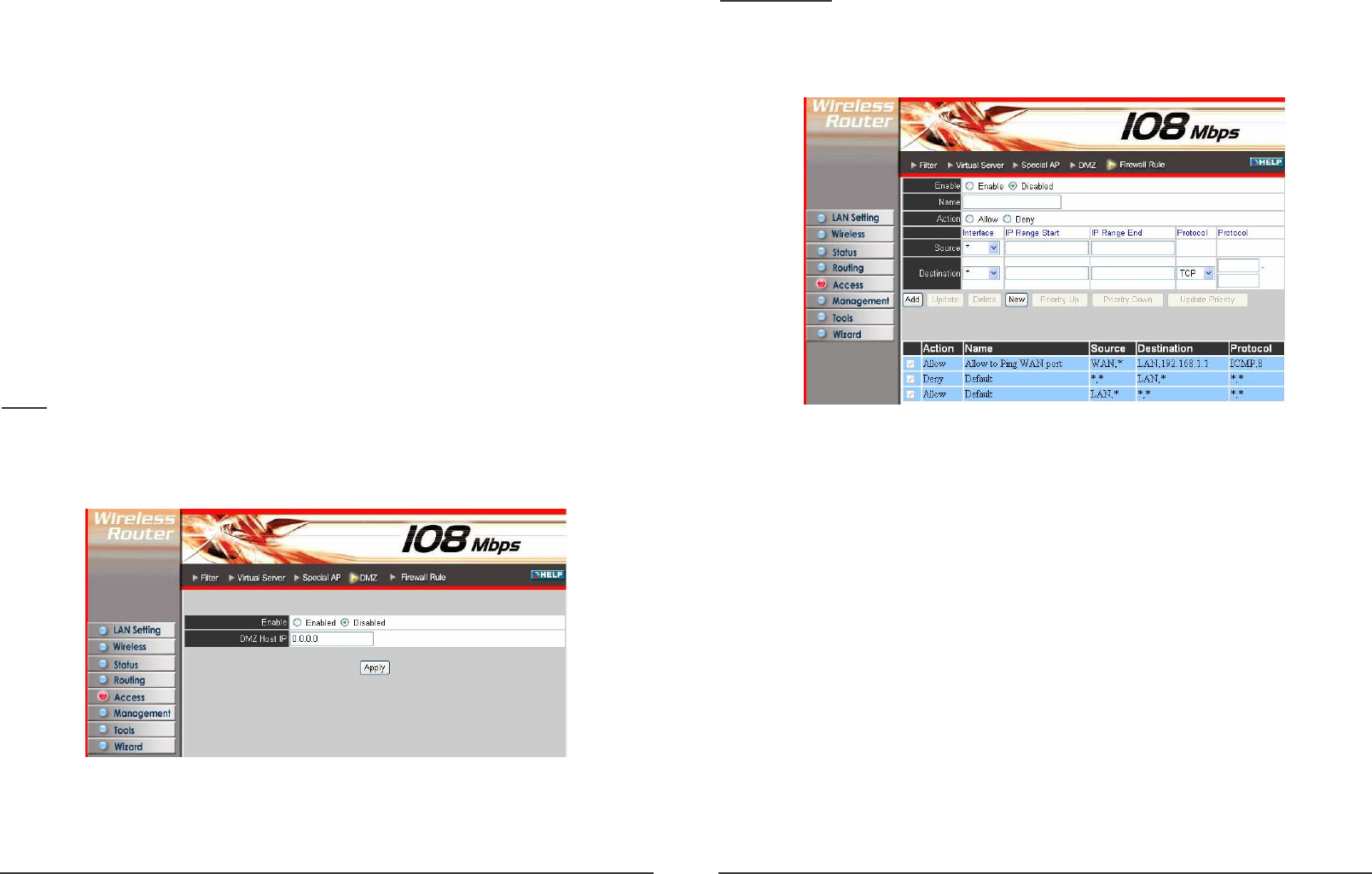
DMZ
This screen enables user to create a DMZ for those computers that cannot access
Internet applications properly through the router and associated security settings.
Note: Any clients added to the DMZ exposes the clients to security risks such as
viruses and unauthorized access.
Enable: Click to enable or disable the DMZ.
DMZ Host IP: Type a host IP address for the DMZ. The computer with this IP
address acts as a DMZ host with unlimited Internet access.
Apply: Click to save the settings.
44
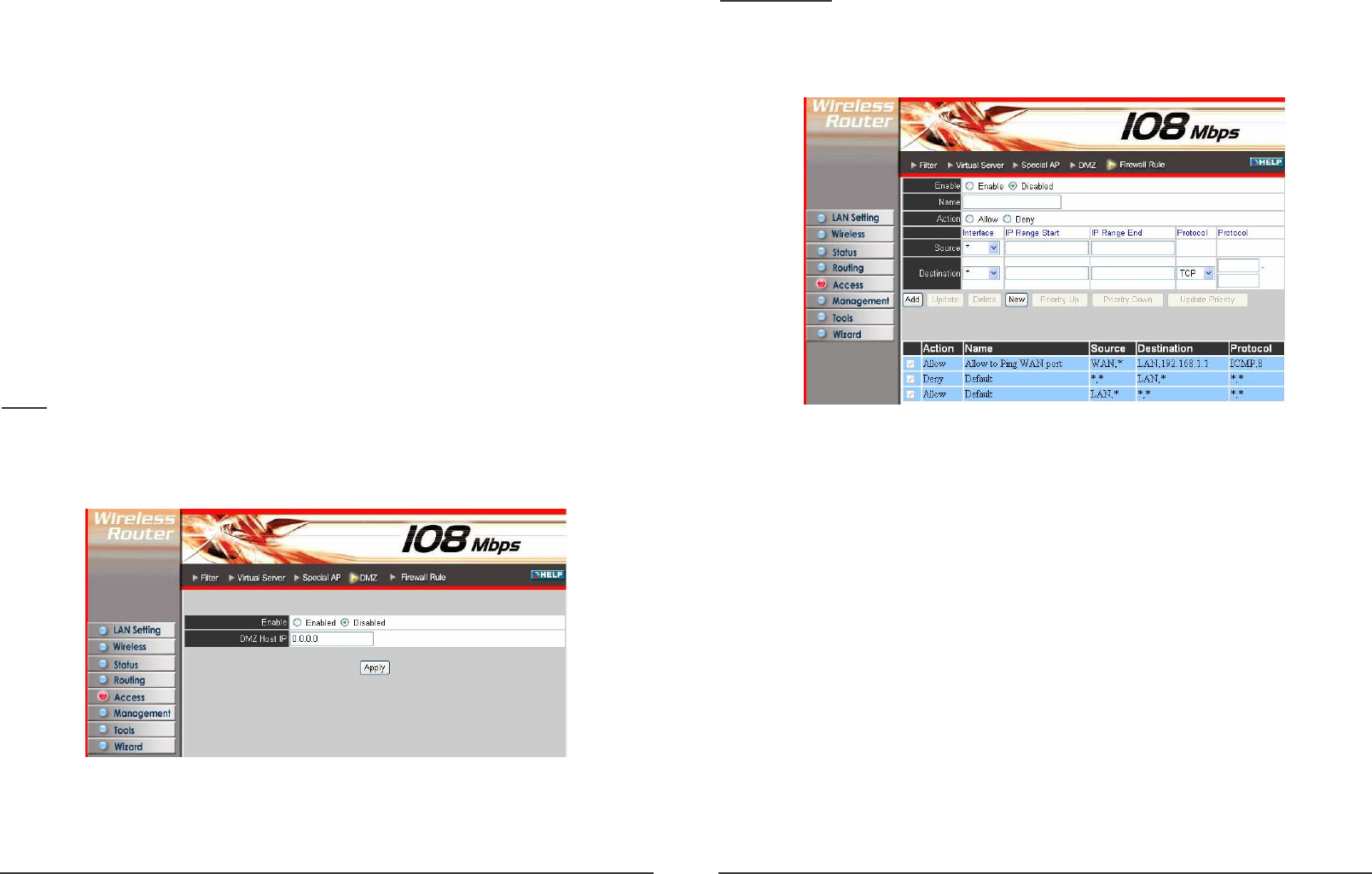
Firewall Rule
This screen enables user to set up the firewall. The router provides basic firewall
functions, by filtering all the packets that enter the router using a set of rules. The
rules are in an order sequence list--the lower the rule number, the higher the priority
the rule has.
Enable: Click to enable or disable the firewall rule profile.
Name: Type a descriptive name for the firewall rule profile.
Action: Select whether to allow or deny packets that conform to the rule.
Source: Defines the source of the incoming packet that the rule is applied to.
Interface: Select which interface (WAN or LAN) the rule is applied to.
IP Range Start: Type the start IP address that the rule is applied to.
IP Range End: Type the end IP address that the rule is applied to.
Destination: Defines the destination of the incoming packet that the rule is applied
to.
Interface: Select which interface (WAN or LAN) the rule is applied to.
IP Range Start: Type the start IP address that the rule is applied to.
IP Range End: Type the end IP address that the rule is applied to.
Protocol: Select the protocol (TCP, UDP, or ICMP) of the destination.
Port Range: Select the port range.
Add: Click to add the rule profile to the table at the bottom of the screen.
Update: Click to update information for the rule if user have selected a list item
and have made changes.