CHAPTER 5: AUTHENTICATION DEPLOYMENT ACTIVATE AUTHENTICATION ON THE NETWORK
8E6 TECHNOLOGIES, R3000 ENTERPRISE FILTER AUTHENTICATION USER GUIDE 195
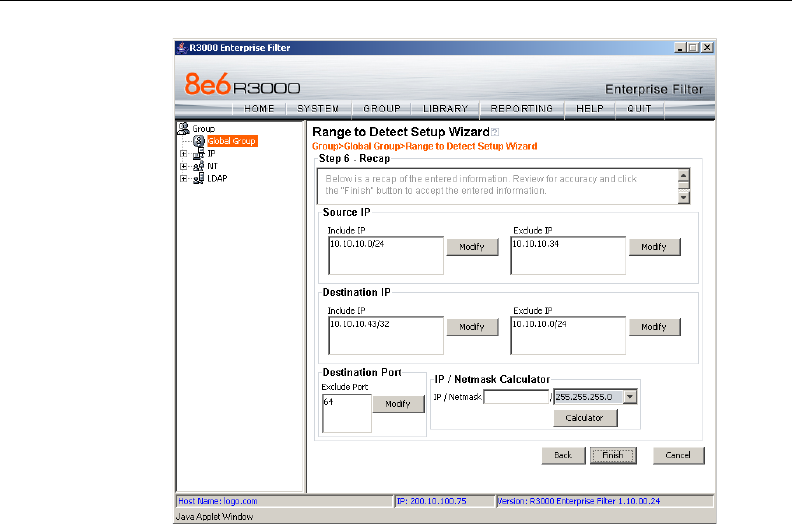
Fig. 5-30 Range to Detect Setup Wizard, Step 6
11. After review the contents in all list boxes, click Finish to
accept all your entries.
As a result of these entries, the IP address(es) specified to
be excluded will not be logged or filtered on the network.
Bypass Step 1B and go on to Step 2 to complete this
process.


















