7-22
Cisco ASA Series Firewall CLI Configuration Guide
Chapter 7 Configuring AAA Rules for Network Access
Configuring Accounting for Network Access
To configure accounting, perform the following steps:
Examples
The following example authenticates, authorizes, and accounts for inside Telnet traffic. Telnet traffic to
servers other than 209.165.201.5 can be authenticated alone, but traffic to 209.165.201.5 requires
authorization and accounting.
ciscoasa(config)# aaa-server AuthOutbound protocol tacacs+
ciscoasa(config-aaa-server-group)# exit
ciscoasa(config)# aaa-server AuthOutbound (inside) host 10.1.1.1
ciscoasa(config-aaa-server-host)# key TACPlusUauthKey
ciscoasa(config-aaa-server-host)# exit
ciscoasa(config)# access-list TELNET_AUTH extended permit tcp any any
eq telnet
ciscoasa(config)# access-list SERVER_AUTH extended permit tcp any host 209.165.201.5 eq
telnet
ciscoasa(config)# aaa authentication match TELNET_AUTH inside AuthOutbound
ciscoasa(config)# aaa authorization match SERVER_AUTH inside AuthOutbound
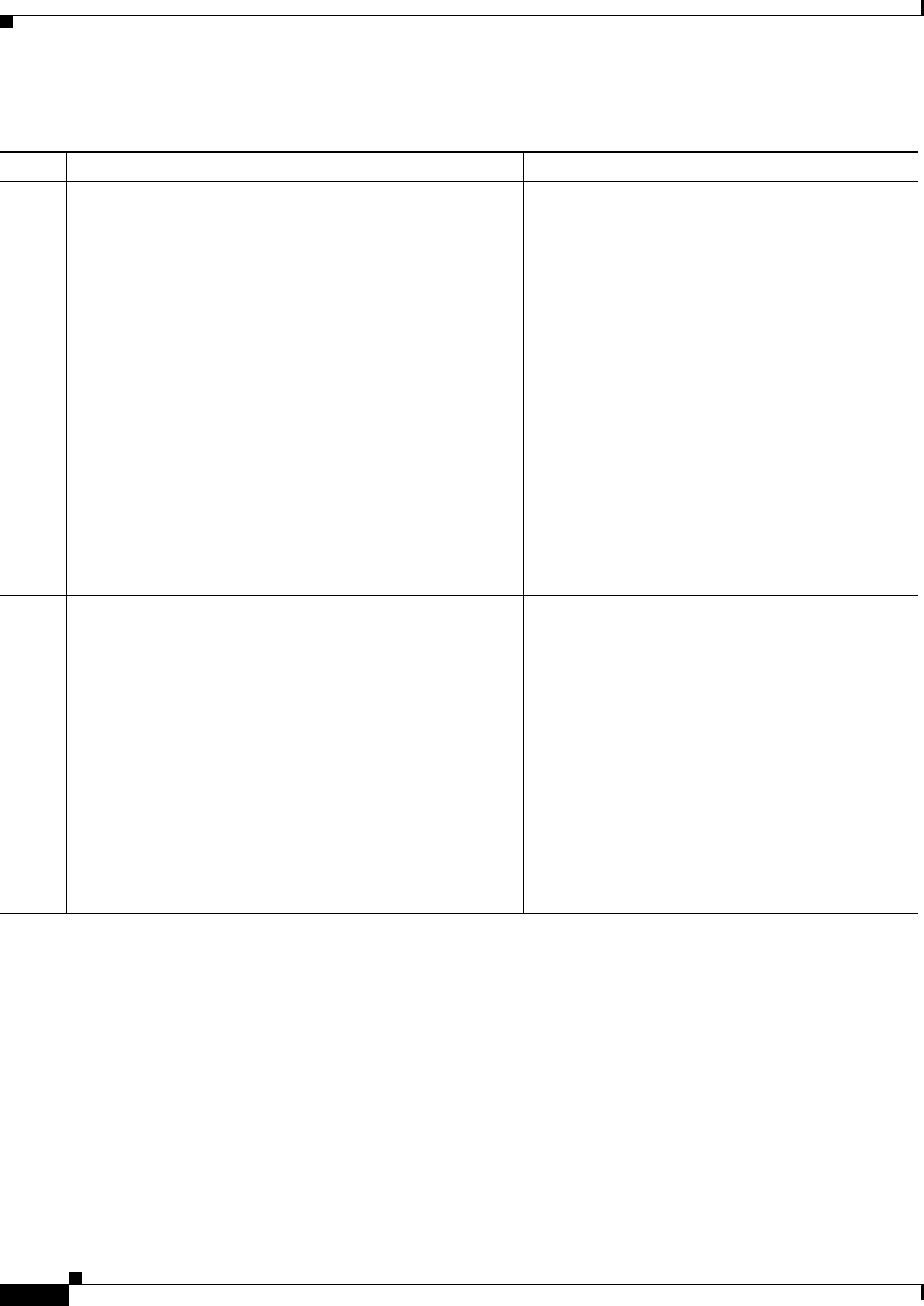
Command Purpose
Step 1
access-list
Example:
ciscoasa(config)# access-list TELNET_AUTH extended
permit tcp any any eq telnet
If you want the ASA to provide accounting data per
user, you must enable authentication. For more
information, see the “Configuring Network Access
Authentication” section on page 7-7. If you want the
ASA to provide accounting data per IP address,
enabling authentication is not necessary.
Creates an ACL that identifies the source addresses
and destination addresses of traffic for which you
want accounting data. For instructions, see the
general operations configuration guide.
The permit ACEs mark matching traffic for
accounting, while deny entries exclude matching
traffic from accounting.
Note If you have configured authentication and
want accounting data for all the traffic being
authenticated, you can use the same ACL
that you created for use with the aaa
authentication match command.
Step 2
aaa accounting match acl_name interface_name
server_group
Example:
ciscoasa(config)# aaa accounting match SERVER_AUTH
inside AuthOutbound
Enables accounting.
The acl_name argument is the ACL name set in the
access-list command.
The interface_name argument is the interface name
set in the nameif command.
The server_group argument is the server group
name set in the aaa-server command.
Note Alternatively, you can use the aaa
accounting include command (which
identifies traffic within the command), but
you cannot use both methods in the same
configuration. See the command reference
for more information.


















