EDS-518A Series User’s Manual Featured Functions
3-47
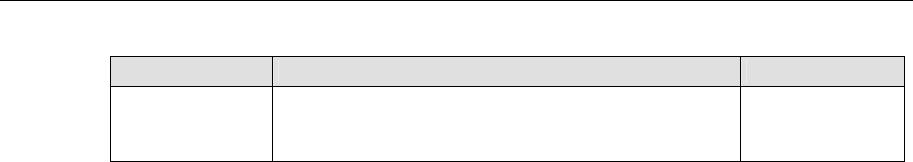
Ingress
Setting Description Factory Default
Ingress rate Select the ingress rate for all packets from the following
options: not limited, 3%, 5%, 10%, 15%, 25%, 35%,
50%, 65%, 85%
N/A
Using Port Access Control
EDS-518A provides two kinds of Port-Based Access Controls. One is Static Port Lock and the
other is IEEE 802.1X.
Static Port Lock
EDS-518A can also be configured to protect static MAC addresses for a specific port. With the
Port Lock function, these locked ports will not learn any additional addresses, but only allow
traffic from preset static MAC addresses, helping to block crackers and careless usage.
IEEE 802.1X
The IEEE 802.1X standard defines a protocol for client/server-based access control and
authentication. The protocol restricts unauthorized clients from connecting to a LAN through ports
that are open to the Internet, and which otherwise would be readily accessible. The purpose of the
authentication server is to check each client that requests access to the port. The client is only
allowed access to the port if the client’s permission is authenticated.
The IEEE 802.1X Concept
Three components are used to create an authentication mechanism based on 802.1X standards:
Client/Supplicant, Authentication Server, and Authenticator.
Supplicant: The end station that requests access to the LAN and switch services and responds to
the requests from the switch.
Authentication server: The server that performs the actual authentication of the supplicant.
Authenticator: Edge switch or wireless access point that acts as a proxy between the supplicant
and the authentication server, requesting identity information from the supplicant, verifying the
information with the authentication server, and relaying a response to the supplicant.
EDS-518A acts as an authenticator in the 802.1X environment. A supplicant and an authenticator
exchange EAPOL (Extensible Authentication Protocol over LAN) frames with each other. We can
either use an external RADIUS server as the authentication server, or implement the authentication
server in EDS-518A by using a Local User Database as the authentication look-up table. When we
use an external RADIUS server as the authentication server, the authenticator and the
authentication server exchange EAP frames between each other.
Authentication can be initiated either by the supplicant or the authenticator. When the supplicant
initiates the authentication process, it sends an “EAPOL-Start” frame to the authenticator. When
the authenticator initiates the authentication process or when it receives an “EAPOL Start” frame,
it sends an “EAP Request/Identity” frame to ask for the username of the supplicant. The following
actions are described below:


















