ZyXEL AG-200 User’s Guide
WLAN Networking 2-7
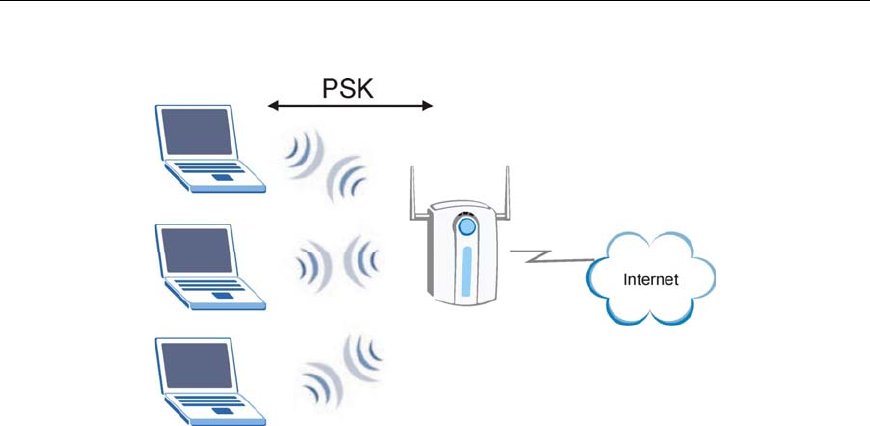
Step 4. The AP and wireless clients use the TKIP encryption process to encrypt data exchanged
between them.
Figure 2-6
WPA-PSK Authentication
2.2.5 WPA with RADIUS Application Example
You need the IP address of the RADIUS server, its port number (default is 1812), and the RADIUS shared
secret. A WPA application example with an external RADIUS server looks as follows. “A” is the RADIUS
server. “DS” is the distribution system.
Step 1. The AP passes the wireless client’s authentication request to the RADIUS server.
Step 2. The RADIUS server then checks the user's identification against its database and grants or
denies network access accordingly.
Step 3. The RADIUS server distributes a Pairwise Master Key (PMK) key to the AP that then sets up a
key hierarchy and management system, using the pair-wise key to dynamically generate unique
data encryption keys to encrypt every data packet that is wirelessly communicated between the
AP and the wireless clients.


















