User Authentication.
3-25
CLI – Assign a user name to access-level 15 (i.e., administrator), then specify the
password.
Configuring Local/Remote Logon Authentication
Use the Authentication Settings menu to restrict management access based on
specified user names and passwords. You can manually configure access rights on
the switch, or you can use a remote access authentication server based on RADIUS
or TACACS+ protocols.
Remote Authentication Dial-in
User Service (RADIUS) and
Terminal Access Controller Access
Control System Plus (TACACS+)
are logon authentication protocols
that use software running on a
central server to control access to
RADIUS-aware or TACACS
-aware devices on the network. An
authentication server contains a
database of multiple user name/
password pairs with associated
privilege levels for each user that requires management access to the switch.
RADIUS uses UDP while TACACS+ uses TCP. UDP only offers best effort delivery,
while TCP offers a connection-oriented transport. Also, note that RADIUS encrypts
only the password in the access-request packet from the client to the server, while
TACACS+ encrypts the entire body of the packet.
Command Usage
• By default, management access is always checked against the authentication
database stored on the local switch. If a remote authentication server is used,
you must specify the authentication sequence and the corresponding
parameters for the remote authentication protocol. Local and remote logon
authentication control management access via the console port, web browser,
or Telnet.
• RADIUS and TACACS+ logon authentication assign a specific privilege level for
each user name/password pair. The user name, password, and privilege level
must be configured on the authentication server.
• You can specify up to three authentication methods for any user to indicate the
authentication sequence. For example, if you select (1) RADIUS, (2) TACACS
and (3) Local, the user name and password on the RADIUS server is verified
first. If the RADIUS server is not available, then authentication is attempted
using the TACACS+ server, and finally the local user name and password is
checked.
Console(config)#username bob access-level 15 4-24
Console(config)#username bob password 0 smith
Console(config)#
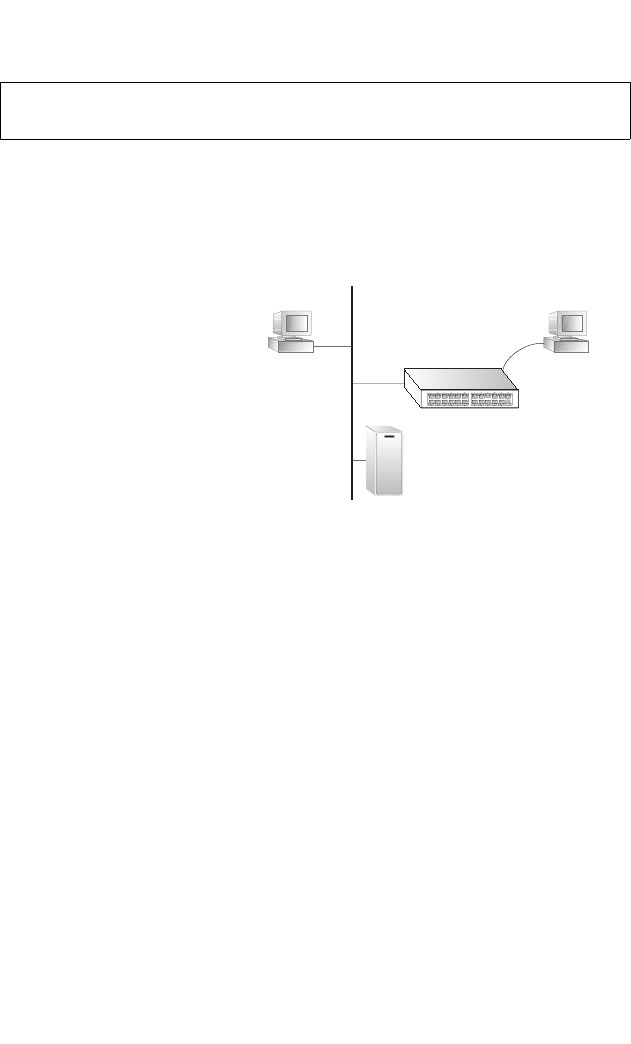
Web
Telnet
RADIUS/
TACACS+
server
console
1. Client attempts management access.
2. Switch contacts authentication server.
3.Authentication server challenges client.
4. Client responds with proper password or key.
5.Authentication server approves access.
6. Switch grants management access.


















