Vigor2800 Series User’s Guide
77
two IP addresses of 192.168.1.200 and 192.168.1.201 are
reserved for ISDN remote dial-in user.
3
3
.
.
7
7
.
.
3
3
I
I
P
P
S
S
e
e
c
c
G
G
e
e
n
n
e
e
r
r
a
a
l
l
S
S
e
e
t
t
u
u
p
p
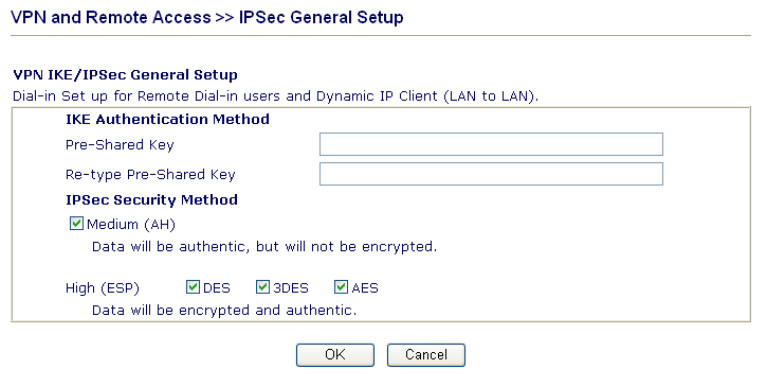
In IPSec General Setup, there are two major parts of configuration.
There are two phases of IPSec.
¾ Phase 1: negotiation of IKE parameters including encryption, hash, Diffie-Hellman
parameter values, and lifetime to protect the following IKE exchange, authentication of
both peers using either a Pre-Shared Key or Digital Signature (x.509). The peer that
starts the negotiation proposes all its policies to the remote peer and then remote peer
tries to find a highest-priority match with its policies. Eventually to set up a secure
tunnel for IKE Phase 2.
¾ Phase 2: negotiation IPSec security methods including Authentication Header (AH) or
Encapsulating Security Payload (ESP) for the following IKE exchange and mutual
examination of the secure tunnel establishment.
There are two encapsulation methods used in IPSec, Transport and Tunnel. The Transport
mode will add the AH/ESP payload and use original IP header to encapsulate the data
payload only. It can just apply to local packet, e.g., L2TP over IPSec. The Tunnel mode will
not only add the AH/ESP payload but also use a new IP header (Tunneled IP header) to
encapsulate the whole original IP packet.
Authentication Header (AH) provides data authentication and integrity for IP packets passed
between VPN peers. This is achieved by a keyed one-way hash function to the packet to
create a message digest. This digest will be put in the AH and transmitted along with packets.
On the receiving side, the peer will perform the same one-way hash on the packet and
compare the value with the one in the AH it receives.
Encapsulating Security Payload (ESP) is a security protocol that provides data
confidentiality and protection with optional authentication and replay detection service.
IKE Authentication Method This usually applies to those are remote dial-in user or node
(LAN-to-LAN) which uses dynamic IP address and
IPSec-related VPN connections such as L2TP over IPSec
and IPSec tunnel.
Pre-Shared Key -Currently only support Pre-Shared Key
authentication.
Pre-Shared Key- Specify a key for IKE authentication
Re-type Pre-Shared Key-Confirm the pre-shared key.


















