- 31 -
Chapter 4 802.1X Authentication Setup
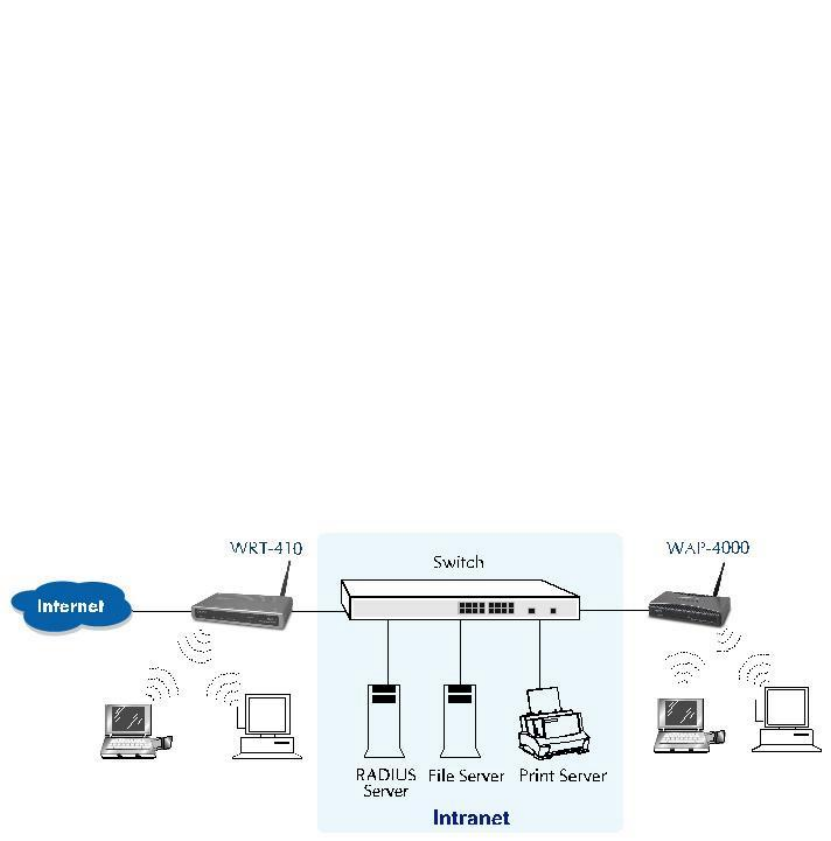
4.1 802.1X Infrastructure
An 802.1X Infrastructure is composed of three major components: Authenticator, Authentication server,
and Supplicant.
Authentication server: An entity that provides an authentication service to an authenticator. This
service determines, from the credentials provided by the supplicant, whether the supplicant is authorized
to access the services provided by the authenticator.
Authenticator: An entity at one end of a point-to-point LAN segment that facilitates authentication of the
entity attached to the other end of that link.
Supplicant: An entity at one end of a point-to-point LAN segment that is being authenticated by an
authenticator attached to the other end of that link.
In the following sections, we will guide you to build an 802.1X Infrastructure step by step. The instructions
are divided into three parts:
RADIUS Server Setup: Microsoft Windows 2000 server.
Authenticator Setup: WRT-410.
Wireless Client Setup: Microsoft Windows XP.
The above graph shows the network topology of the solution we are going to introduce. As illustrated, a
group of wireless clients is trying to build a wireless network with WRT-410 in order to have access to
both Internet and Intranet. With 802.1X authentication, each of these wireless clients would have to be
authenticated by RADIUS server. If the client is authorized, WRT-410 would be notified to open up a
communication port to be used for the client. There are 2 Extensive Authentication Protocol (EAP)
methods supported: (1) MD5 and (2) TLS.
MD5 authentication is simply a validation of existing user account and password that is stored in a
database of RADIUS server. Therefore, wireless clients will be prompted for account/password validation
to build the link. TLS authentication is a more complicated authentication, which is using certificate that is
issued by RADIUS server for authentication. TLS authentication is a more secure authentication, since
not only RADIUS server authenticates the wireless client, but also the client can validate RADIUS server
by the certificate that it issues. The TLS authentication request from wireless clients and reply by Radius
Server and WRT-410 can be briefed as follows:
1. The client sends an EAP start message to WRT-410.
2. WRT-410 replies with an EAP Request ID message.
3. The client sends its Network Access Identifier (NAI) – its user name – to WRT-410 in an EAP
Respond message.
4. WRT-410 forwards the NAI to the RADIUS server with a RADIUS Access Request message.
5. The RADIUS server responds to the client with its digital certificate.


















