Chapter 3
Advanced Configuration
20
Wireless-N ADSL2+ Gateway
Authentication Authentication acts as another level of
security. There are two types of authentication: MD5 and
SHA (SHA is recommended because it is more secure). As
with encryption, either of these may be selected, provided
that the VPN device at the other end of the tunnel is using
the same type of authentication. Or, both ends of the
tunnel may choose to Disable authentication.
Key Management
In order for any encryption to occur, the two ends of the
tunnel must agree on the type of encryption and the way
the data will be decrypted. This is done by sharing a “key”
to the encryption code. Under Key Management, you may
choose automatic or manual key management.
Auto (IKE) Key Management
Encryption The Encryption method determines the
length of the key used to encrypt/decrypt ESP packets.
Notice that both sides must use the same method.
Authentication The Authentication method authen-
ticates the Encapsulating Security Payload (ESP) packets.
Select MD5 or SHA. Notice that both sides (VPN endpoints)
must use the same method.
MD5 - A one-way hashing algorithm that
produces a 128-bit digest
SHA - A one-way hashing algorithm that produces
a 160-bit digest
Perfect Forward Secrecy (PFS) If PFS is enabled, IKE
Phase 2 negotiation will generate new key material for
IP traffic encryption and authentication. Note that both
sides must have PFS enabled.
Pre-Shared Key IKE uses the Pre-Shared Key to
authenticate the remote IKE peer. Both character and
hexadecimal values are acceptable in this field, e.g., “My_
@123” or “0x4d795f40313233”. Note that both sides must
use the same Pre-Shared Key.
Key Lifetime This field specifies the lifetime of the
IKE generated key. If the time expires, a new key will be
renegotiated automatically. The Key Lifetime may range
from 300 to 100,000,000 seconds. The default lifetime is
3600 seconds.
Manual Key Management
Encryption Algorithm The Encryption method
determines the length of the key used to encrypt/decrypt
ESP packets. Notice that both sides must use the same
method.
Encryption Key This field specifies a key used to encrypt
and decrypt IP traffic. Both character and hexadecimal
values are acceptable in this field. Note that both sides
must use the same Encryption Key.
Authentication Algorithm The Authentication method
authenticates the Encapsulating Security Payload (ESP)
•
•
packets. Select MD5 or SHA. Notice that both sides (VPN
endpoints) must use the same method.
MD5 A one-way hashing algorithm that produces a 128-
bit digest
SHA A one-way hashing algorithm that produces a 160-
bit digest
Authentication Key This field specifies a key used to
authenticate IP traffic. Both character and hexadecimal
values are acceptable in this field. Note that both sides
must use the same Authentication Key.
Inbound SPI/Outbound SPI The Security Parameter
Index (SPI) is carried in the ESP header. This enables the
receiver to select the SA, under which a packet should
be processed. The SPI is a 32-bit value. Both decimal and
hexadecimal values are acceptable. e.g., “987654321” or
“0x3ade68b1”. Each tunnel must have a unique Inbound
SPI and Outbound SPI. No two tunnels share the same
SPI. Note that the Inbound SPI must match the remote
gateway’s Outbound SPI, and vice versa.
The Status field at the bottom of the screen will show
when a tunnel is active.
To connect a VPN tunnel, click the Connect button. Click
the Disconnect button to break a connection for the
current VPN tunnel. The View Log button, when logging is
enabled on the Log screen of the Administration tab, will
show you VPN activity on a separate screen. The VPN Log
screen displays successful connections, transmissions and
receptions, and the types of encryption used. For more
advanced VPN options, click the Advanced Settings
button to open the Advanced Settings screen.
Click Save Settings to apply your changes, or click Cancel
Changes to cancel your changes.
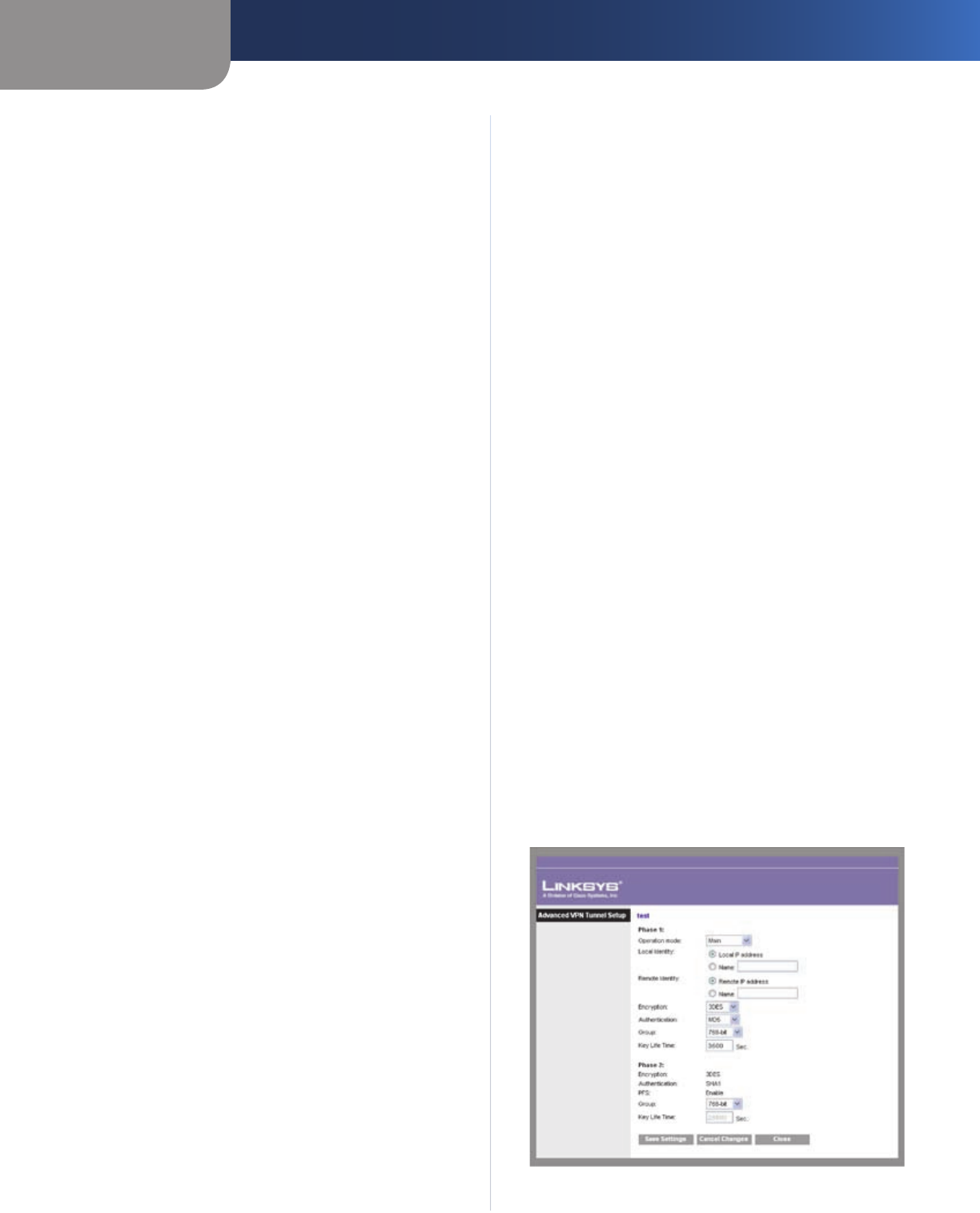
Advanced VPN Tunnel Setup
Advanced VPN Tunnel Setup


















