ES-1552 User’s Guide
89
CHAPTER 15
Auto Denial of Service (DoS)
This chapter shows you how to configure automatic Denial of Service prevention on the
switch.
15.1 About Denial of Service Attacks
Denial of Service (DoS) attacks try to disable a device or network so users no longer have
access to network resources. The switch has features which automatically detect and thwart
currently known DoS attacks.
15.1.1 DoS Attacks Summary
The following table summarizes the types of attacks the switch can prevent.
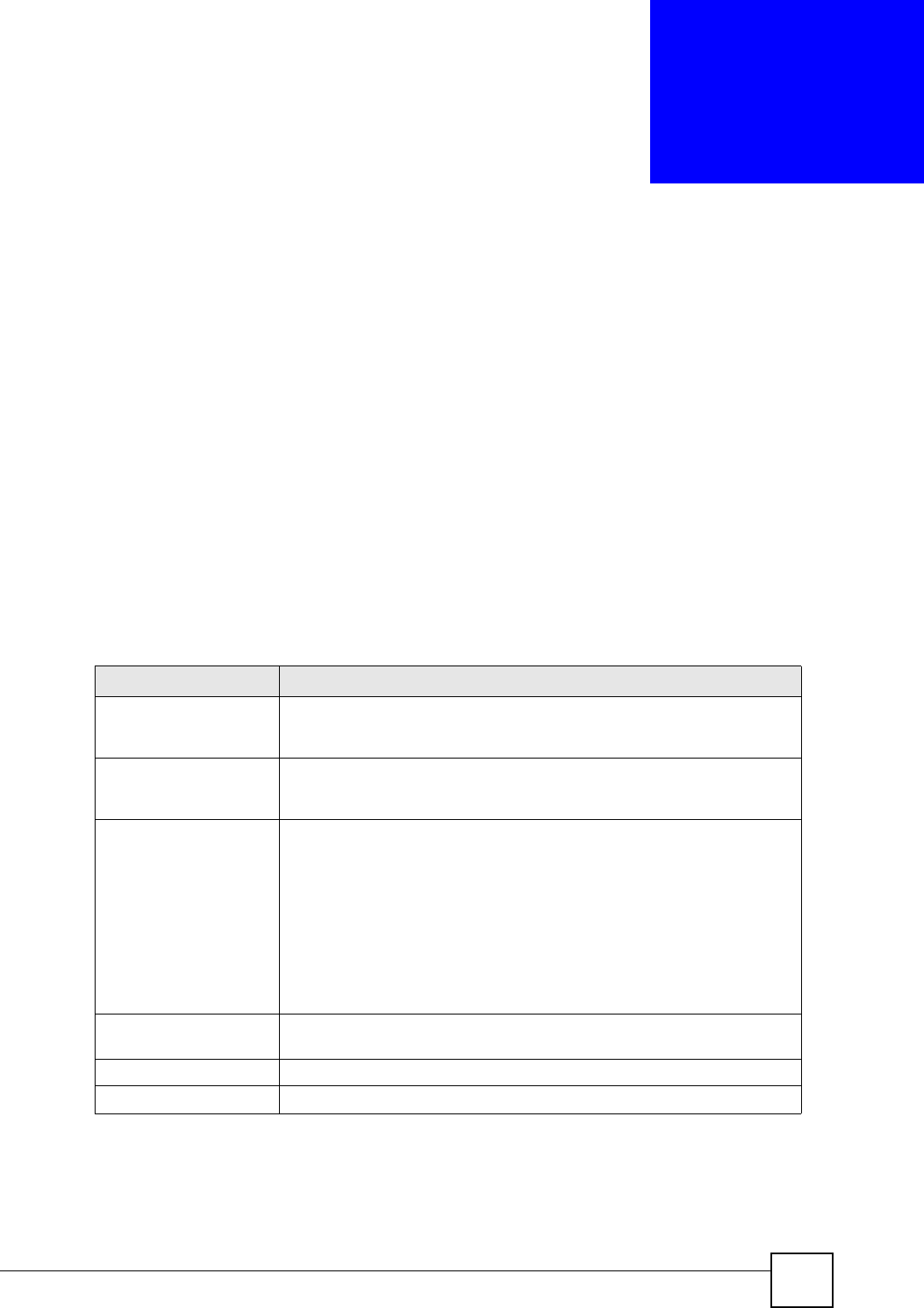
Table 29 DoS Attack Summary
ATTACK DESCRIPTION
Land Attacks These attacks result from sending a specially crafted packet to a machine
where the source host IP address is the same as the destination host IP
address. The system attempts to reply to itself, resulting in system lockup.
Blat Attacks These attacks result from sending a specially crafted packet to a machine
where the source host port is the same as the destination host port. The
system attempts to reply to itself, resulting in system lockup.
SYNFIN scans SYNchronization (SYN), ACKnowledgment (ACK) and FINish (FIN)
packets are used to initiate, acknowledge and conclude TCP/IP
communication sessions. The following scans exploit weaknesses in the
TCP/IP specification and try to illicit a response from a host to identify ports
for an attack:
Scan SYNFIN - SYN and FIN bits are set in the packet.
Xmascan - TCP sequence number is zero and the FIN, URG and PSH bits
are set.
NULL Scan - TCP sequence number is zero and all control bits are zeroes.
SYN with port < 1024 - SYN packets with source port less than 1024.
Smurf Attacks This attack uses Internet Control Message Protocol (ICMP) echo requests
packets (pings) to cause network congestion or outages.
Ping Flooding This attack floods the target network with ICMP packets.
SYN/SYN-ACK Flooding This attack floods the target network with SYN or SYN/ACK packets.


















