51
Enhanced Wireless Router
SECTIONSTable of Contents 1 2 3 4 5 7 8 9 106
USING THE WEB-BASED ADVANCED USER INTERFACE
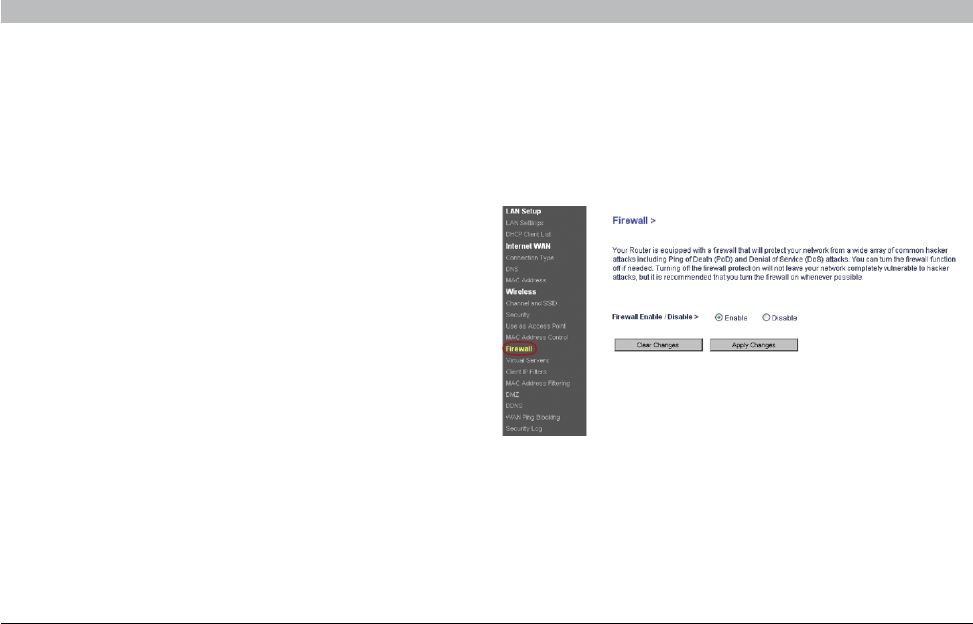
Configuring the Firewall
Your Router is equipped with a firewall that will protect your network
from a wide array of common hacker attacks including:
• IP Spoofing
• Land Attack Ping of Death (PoD)
• Denial of Service (DoS)
• IP with zero length
• Smurf Attack
• TCP Null Scan
• SYN flood
• UDP flooding
• Tear Drop Attack
• ICMP defect
• RIP defect
• Fragment flooding
The firewall also masks common ports that are frequently used to
attack networks� These ports appear to be “stealth” meaning that for
all intents and purposes, they do not exist to a would-be hacker� You
can turn the firewall function off if needed; however, it is recommended
that you leave the firewall enabled� Disabling the firewall protection will
not leave your network completely vulnerable to hacker attacks, but it is
recommended that you leave the firewall enabled�


















