54 Mbps Wireless Router WGR614v8 User Manual
2-4 Safeguarding Your Network
v1.1, May 2008
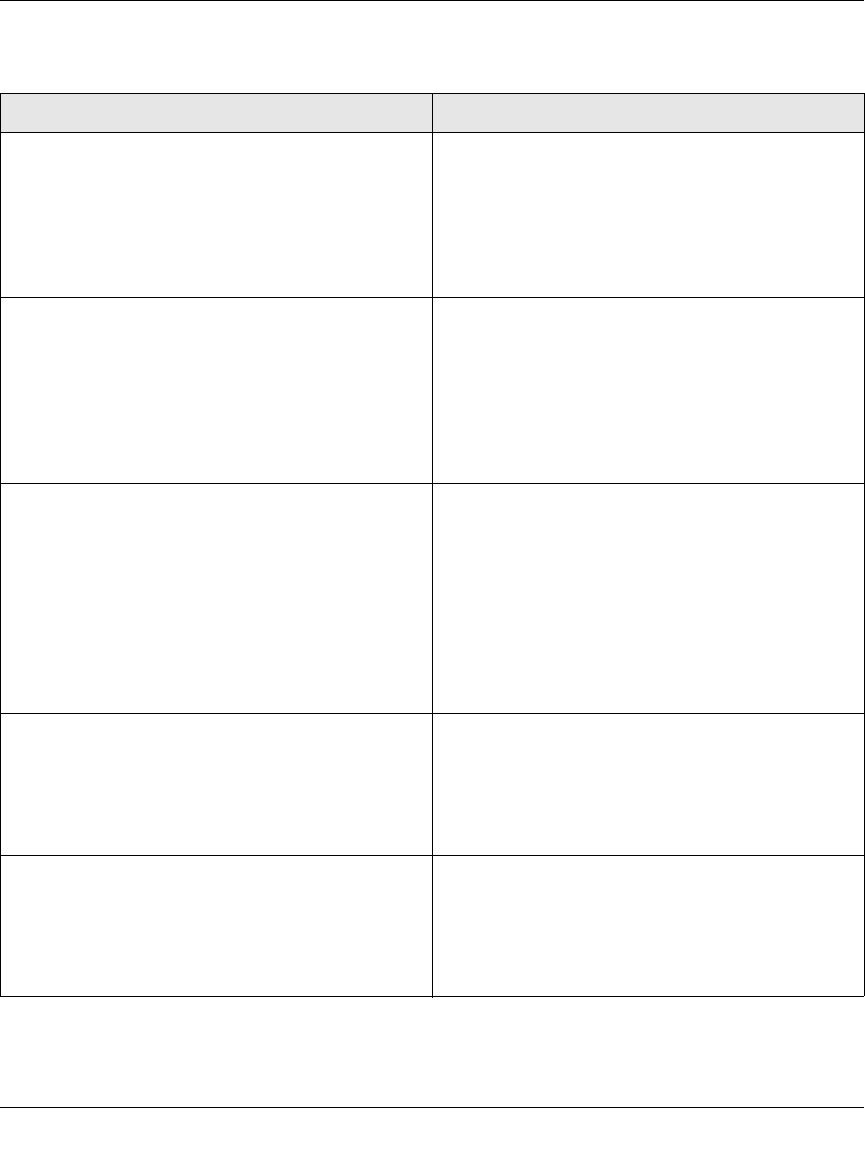
Table 2-2. Other Features That Enhance Security
Security Type Description
Disable the wireless router radio. If you disable the wireless router radio, wireless
devices cannot communicate with the router at all.
You might disable this when you are away or when
other users of your network all use wired
connections.
For more information, see “Viewing Advanced
Wireless Settings” on page 2-10.
Turn off the broadcast of the wireless network
name SSID.
If you disable the broadcast of the SSID, only
devices that know the correct SSID can connect.
This nullifies the wireless network discovery feature
of some products such as Windows XP, but your data
is still fully exposed to an intruder using available
wireless eavesdropping tools.
For more information, see “Viewing Advanced
Wireless Settings” on page 2-10.
Restrict access based on MAC address. You can restrict access to only trusted computers so
that unknown computers cannot wirelessly connect
to the Wireless-G Router. MAC address filtering
adds an obstacle against unwanted access to your
network by the general public, but the data broadcast
over the wireless link is fully exposed. This data
includes your trusted MAC addresses, which can be
read and impersonated by a hacker.
For more information, see “Restricting Wireless
Access by MAC Address” on page 2-17.
Modify your firewall’s rules. By default, the firewall allows any outbound traffic
and prohibits any inbound traffic except for
responses to your outbound traffic. However, you
can modify the firewall’s rules.
For more information, see “Understanding Your
Firewall” on page 2-21.
Use the Push 'N' Connect feature (Wi-Fi
Protected Setup).
Wi-Fi Protected Setup provides easy setup by
means of a push button. Older wireless adapters and
devices might not support this. Check whether
devices are WPS enabled.
For more information, see “Using Push 'N' Connect
(Wi-Fi Protected Setup)” on page 2-12.


















