164
E.2.4 Tunnel Mode ESP
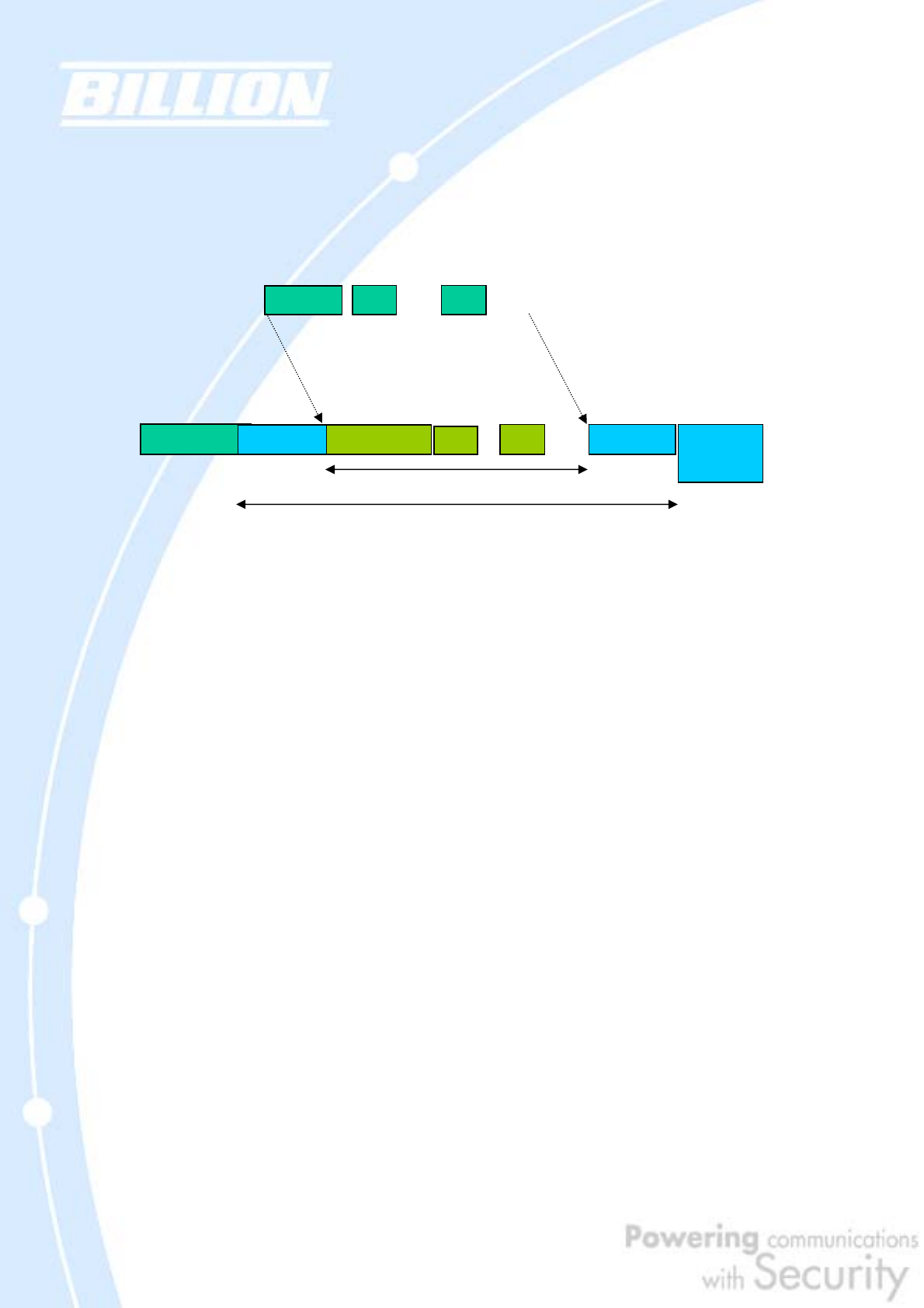
Here is an example of a packet with ESP applied:
E.2.5 Internet Key Exchange (IKE)
Before either AH or ESP can be used, it is necessary for the two communication
devices to exchange a secret key that the security protocols themselves will use. To
do this, IPSec uses Internet Key Exchange (IKE) as a primary support protocol. IKE
facilitates and automates the SA setup, and exchanges keys between parties
transferring data. Using keys ensures that only the sender and receiver of a
message can access it. These keys need to be re-created or refreshed frequently so
that the parties can communicate securely with each other. Refreshing keys on a
regular basis ensures data confidentiality.
There are two phases to this process. Phase I deals with the negotiation and
management of IKE and IPSec parameters. This phase can be carried out in either
one of two modes: Main Mode or Aggressive Mode. Main mode utilizes three
message pairs that negotiate IKE parameters, establish a shared secret and derive
session keys, and exchange and provide identities, retroactively authenticating the
information sent. This method is very secure, but when using the pre-shared key
method for authentication, it is possible to use IDs other than the packets’s IP
addresses. Aggressive mode reduces this process to three messages, but parameter
negotiation is limited, identity protection is lacking except when using public key
Original Packet
Packet with IPSec Encapsulation Security Payload
IP Heade
r
TCP
Data
N
ew IP Heade
r
ESP Heade
r
T
C
P
Data ESP Traile
r
ESP
Authentication
encrypted
Authenticated
Or
g
IP Heade
r


















