xStack
®
DES-3200-10/18/28/28F Layer 2 Ethernet Managed Switch User Manual
Destination
address
Source
address
Ethernet
type
H/W type Protocol
type
H/W
address
length
Protocol
address
length
Operation Sender H/W
address
Sender
protocol
address
Target H/W
address
Target
protocol
address
Gratuitous ARP
Ethernet
(6-byte) (6-byte) (2-byte) (2-byte) (2-byte) (1-byte) (1-byte) (2-byte) (6-byte) (4-byte) (6-byte) (4-byte)
FF-FF-FF-FF-FF-FF 00-20-5C-01-11-11
806
ARP reply 00-20-5C-01-11-11 10.10.10.254 00-20-5C-01-11-11 10.10.10.254
Table-5
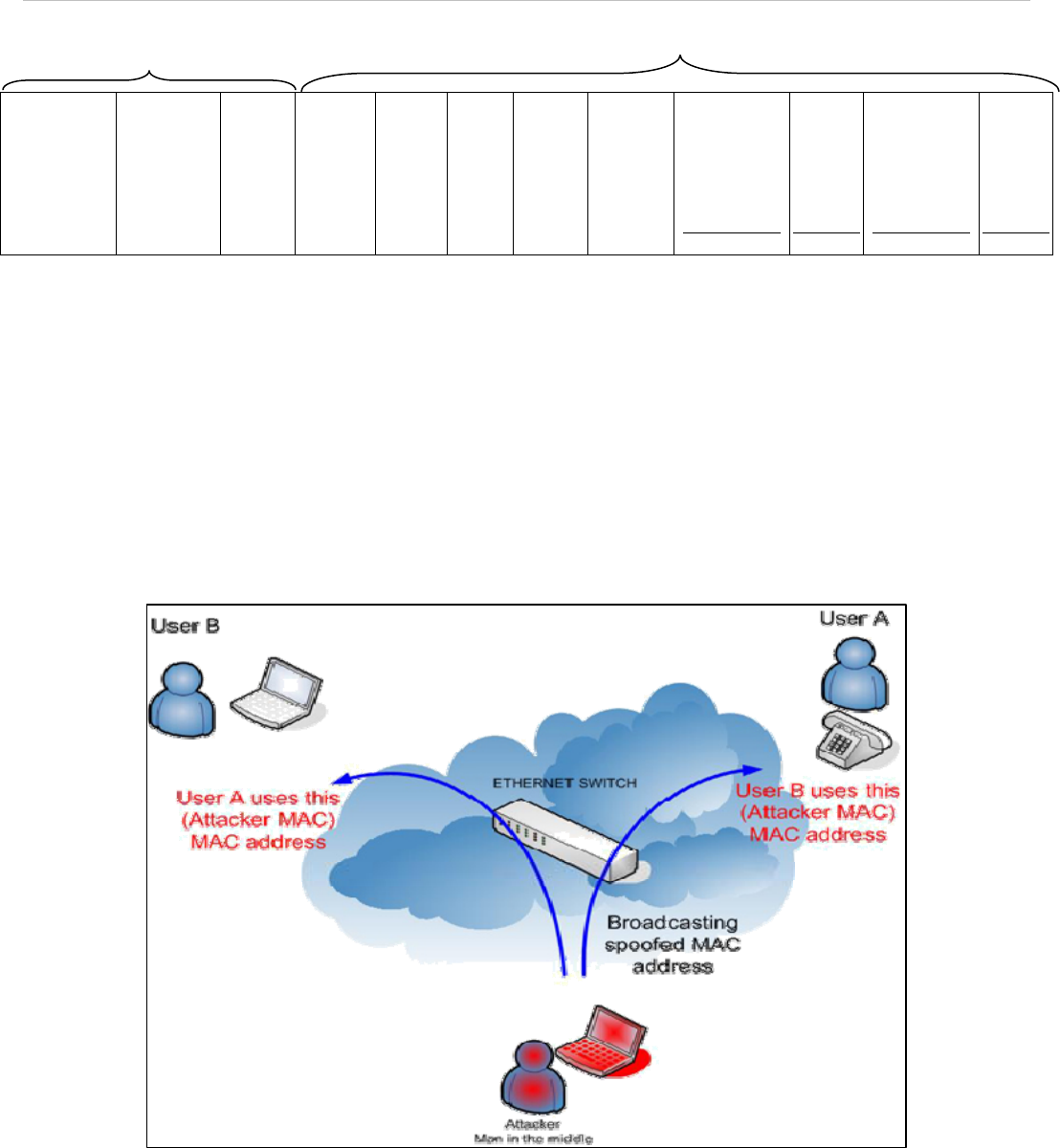
A common DoS attack today can be done by associating a nonexistent or specified MAC address to the IP address of
the network’s default gateway. The malicious attacker only needs to broadcast ONE Gratuitous ARP to the network
claiming it is the gateway so that the whole network operation will be turned down as all packets to the Internet will be
directed to the wrong node.
Likewise, the attacker can either choose to forward the traffic to the actual default gateway (passive sniffing) or modify
the data before forwarding it (man-in-the-middle attack). The hacker cheats the victim’s PC to think that it is a router
and cheats the router to think it is the victim. As can be seen in Figure-5 all traffic will be then sniffed by the hacker but
the users will not notice anything happening.
Figure-5
222


















