33
Chapter 6: Configuring the Wireless-G VPN Broadband Router
The Security Tab - VPN
Wireless-G VPN Broadband Router
Encryption. Using encryption also helps make your connection more secure. There are two different types of
encryption: DES or 3DES (3DES is recommended because it is more secure). You may choose either of these, but
it must be the same type of encryption that is being used by the VPN device at the other end of the tunnel. Or, you
may choose to disable this feature.
Authentication. Authentication acts as another level of security. There are two types of authentication: MD5 and
SHA (SHA is recommended because it is more secure). As with encryption, either of these may be selected,
provided that the VPN device at the other end of the tunnel is using the same type of authentication. Or, both ends
of the tunnel may choose to disable authentication.
Key Management
Key Exchange Method. Select Auto (IKE) or Manual for the Key Exchange Method. Both ends of a VPN tunnel
must use the same mode of key management. The two methods are described below. After you have selected the
method, the settings available on this screen may change, depending on the selection you have made.
Auto (IKE)
IKE is an Internet Key Exchange protocol used to negotiate key material for Security Association (SA). IKE uses
the Pre-shared Key to authenticate the remote IDE peer.
PFS. PFS (Perfect Forward Secrecy) ensures that the initial key exchange and IKE proposals are secure. To
use PFS, click the Enabled radio button.
Pre-shared Key. You can choose to use a Pre-shared Key or RSA Signature. To use the Pre-shared Key, click
its radio button. enter a series of numbers or letters in the Pre-shared Key field. Based on this word, which
MUST be entered at both ends of the tunnel, a key is generated to scramble (encrypt) the data being
transmitted over the tunnel, where it is unscrambled (decrypted). You may use any combination of up to 24
numbers or letters in this field. No special characters or spaces are allowed.
RSA Signature. You can choose to use a Pre-shared Key or RSA Signature. To use the RSA Signature, click its
radio button. Enter the RSA Signature in the field provided. (This is similar to a Pre-shared Key. Make sure it
matches the RSA Signature entered at the remote end of the tunnel.s
Key Lifetime. You may optionally select to have the key expire at the end of a time period of your choosing.
Enter the number of seconds you’d like the key to be useful, or leave it blank for the key to last indefinitely.
Manual
If you select Manual, you generate the key yourself, and no key negotiation is needed. Basically, manual key
management is used in small static environments or for troubleshooting purposes.
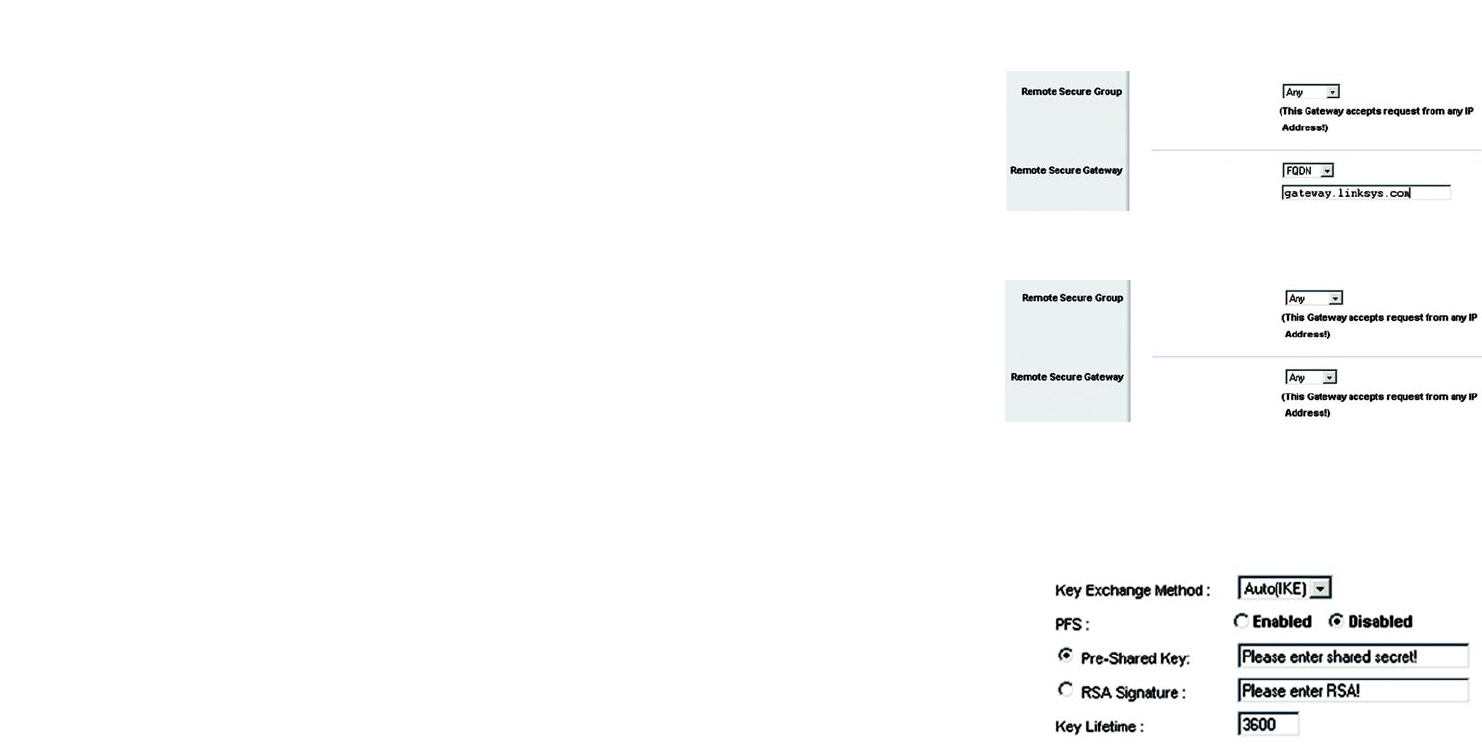
Figure 6-27: Remote Secure Group - Any
and Remote Secure Gateway - FQDN
Figure 6-28: Remote Security Group - Any
and Remote Secure Gateway - Any
Figure 6-29: Key Exchange Method - Auto(IKE)


















