P-334U/P-335U User’s Guide
Chapter 13 IPSec VPN 155
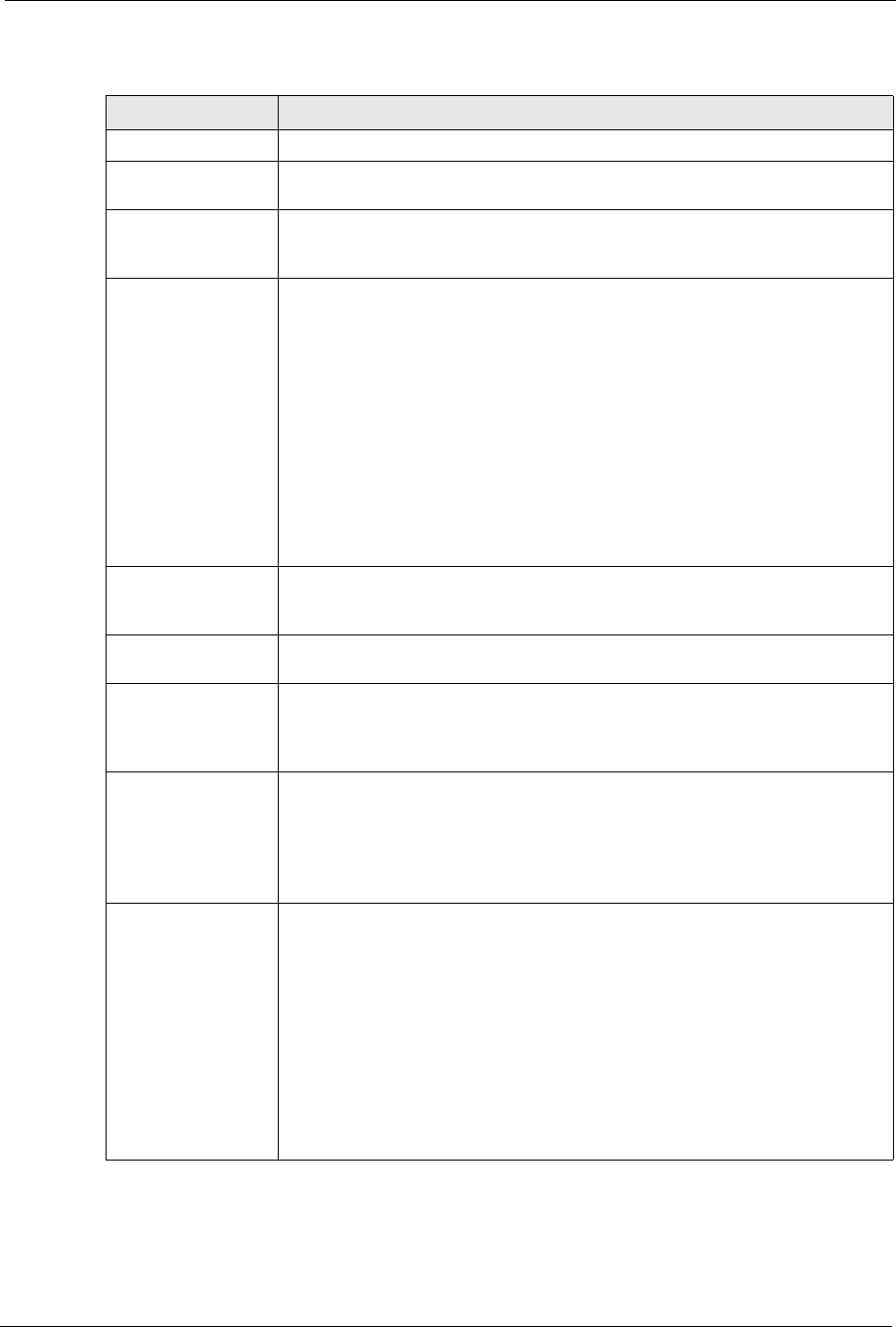
The following table describes the labels in this screen.
Table 53 Security > VPN > Rule Setup: IKE (Advanced)
LABEL DESCRIPTION
Property
Active Select this check box to activate this VPN policy. This option determines
whether a VPN rule is applied before a packet leaves the firewall.
Keep Alive Select this check box to have the ZyXEL Device automatically reinitiate the SA
after the SA lifetime times out, even if there is no traffic. The remote IPSec
router must also have keep alive enabled in order for this feature to work.
NAT Traversal Select this check box to enable NAT traversal. NAT traversal allows you to set
up a VPN connection when there are NAT routers between the two IPSec
routers.
Note: The remote IPSec router must also have NAT traversal
enabled. See
Section 13.1.2.5 on page 143 for more
information.
You can use NAT traversal with ESP protocol using Transport or Tunnel
mode, but not with AH protocol nor with manual key management. In order for
an IPSec router behind a NAT router to receive an initiating IPSec packet, set
the NAT router to forward UDP ports 500 and 4500 to the IPSec router behind
the NAT router.
IPSec Keying Mode Select IKE or Manual from the drop-down list box. IKE provides more
protection so it is generally recommended. Manual is a useful option for
troubleshooting if you have problems using IKE key management.
Protocol Number Enter 1 for ICMP, 6 for TCP, 17 for UDP, etc. 0 is the default and signifies any
protocol.
Enable Replay
Detection
As a VPN setup is processing intensive, the system is vulnerable to Denial of
Service (DoS) attacks The IPSec receiver can detect and reject old or duplicate
packets to protect against replay attacks. Select YES from the drop-down menu
to enable replay detection, or select NO to disable it.
DNS Server (for
IPSec VPN)
If there is a private DNS server that services the VPN, type its IP address here.
The ZyXEL Device assigns this additional DNS server to the ZyXEL Device's
DHCP clients that have IP addresses in this IPSec rule's range of local
addresses.
A DNS server allows clients on the VPN to find other computers and servers on
the VPN by their (private) domain names.
Local Policy Local IP addresses must be static and correspond to the remote IPSec router's
configured remote IP addresses.
Two active SAs can have the same configured local or remote IP address, but
not both. You can configure multiple SAs between the same local and remote IP
addresses, as long as only one is active at any time.
In order to have more than one active rule with the Secure Gateway Address
field set to 0.0.0.0, the ranges of the local IP addresses cannot overlap between
rules.
If you configure an active rule with 0.0.0.0 in the Secure Gateway Address
field and the LAN’s full IP address range as the local IP address, then you
cannot configure any other active rules with the Secure Gateway Address field
set to 0.0.0.0.


















