Setup Pages
80
MVP Modero ViewPoint Touch Panels
Refer to the Using the Site Survey tool section on page 22 for more information on using this
feature.
EAP-TTLS Settings
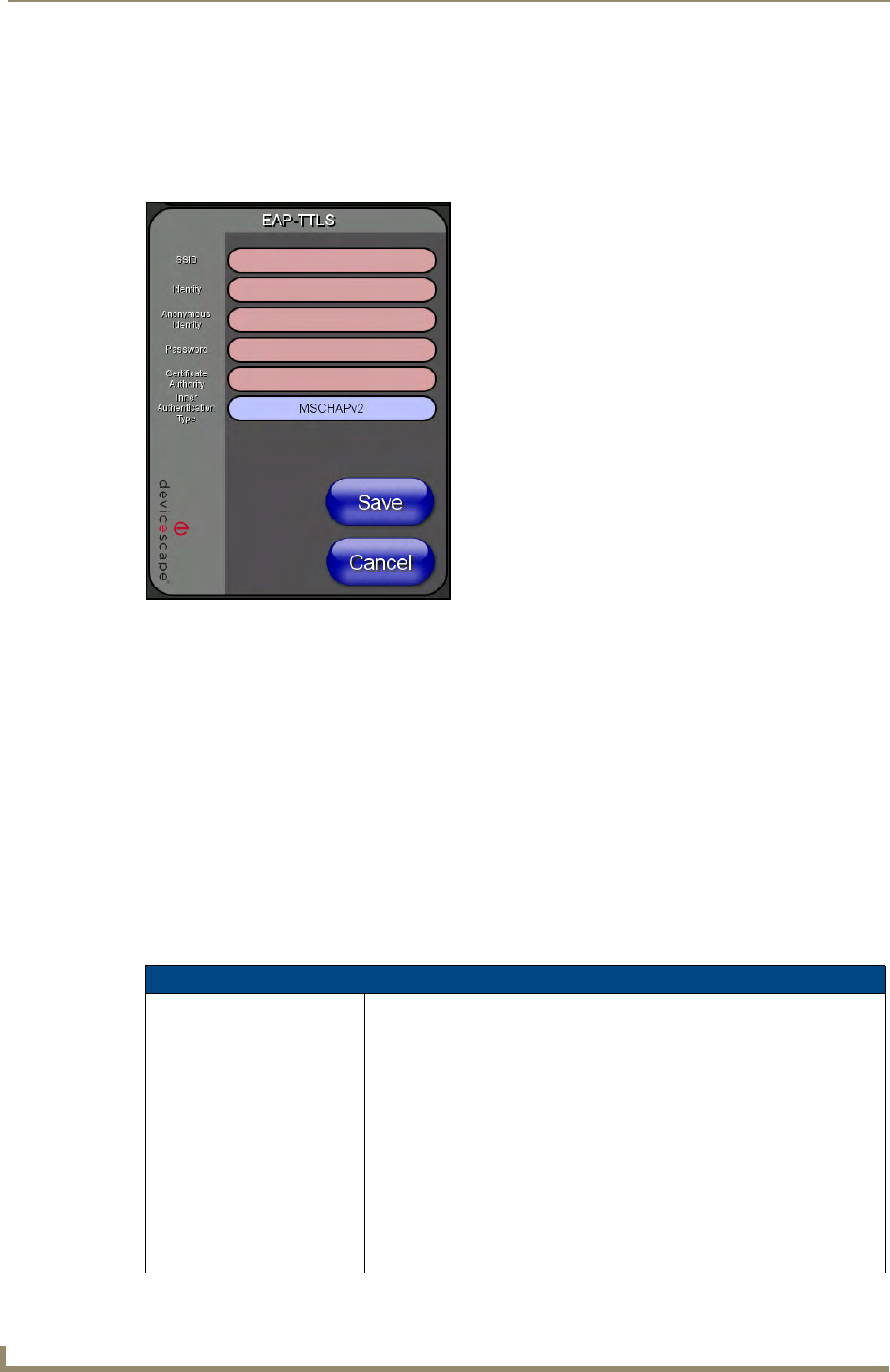
Press the EAP-TTLS button to opens the EAP-TTLS Settings page (FIG. 64).
TTLS (EAP Tunneled Transport Layer Security) is an authentication method that does not use a client
certificate to authenticate the panel. However. this method is more secure than PEAP because it does not
broadcast the identity of the user. Setup is similar to PEAP, but differs in the following areas:
An anonymous identity must be specified until the secure tunnel between the panel and the
Radius server is setup to transfer the real identity of the user.
There is no end-user ability to select from the different types of PEAP.
Additional Inner Authentication choices are available to the end-user.
EAP-TTLS security is designed for wireless environments where it is necessary to have the Radius
server directly validate the identity of the client (panel) before allowing it access to the network. This
validation is done by tunneling a connection through the WAP and directly between the panel and the
Radius server. Once the client is identified and then validated, the Radius server disconnects the tunnel
and allows the panel to access the network directly via the target WAP.
FIG. 64 Wireless Settings page - EAP-TTLS Settings
EAP-TTLS Settings
SSID (Service Set Identifier): Opens an on-screen keyboard to enter the SSID name used on the target
WAP.
The SSID is a unique name used by the WAP, and is assigned to all panels
on that network. An SSID is required by the WAP before the panel is permit-
ted to join the network.
• The SSID is case sensitive and must not exceed 32 characters.
• Make sure this setting is the same for all points in your wireless network.
• NXA-WAP200Gs use AMX as their default SSID.
• With EAP security, the SSID of the WAP must be entered. If it is left blank,
the panel will try to connect to the first access point detected that supports
EAP. However, a successful connection is not guaranteed because the
detected WAP may be connected to a RADIUS server, which may not
support this EAP type and/or have the proper user identities configured.


















