Setup Pages
81
MVP Modero ViewPoint Touch Panels
Refer to the EAP Authentication section on page 155 for further details on these security
options.
Refer to the Using the Site Survey tool section on page 22 for more information on using this
feature.
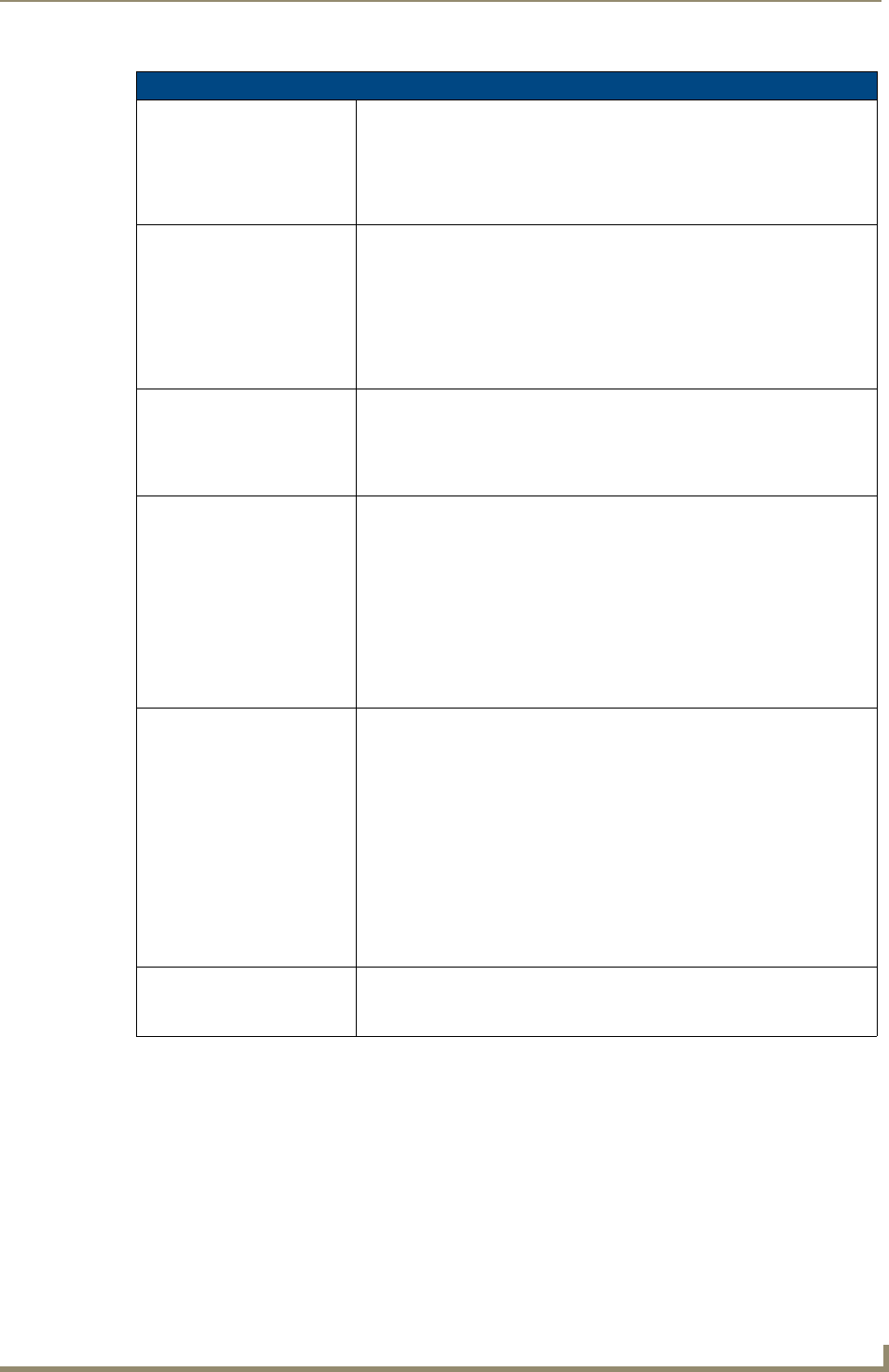
EAP-TTLS Settings (Cont.)
Identity: Opens an on-screen keyboard. Enter an EAP Identity string (used by the
panel to identify itself to an Authentication (RADIUS) Server).
Note: This information is similar to a username used to login to a secured
server or workstation. This works in tandem with the Password string which is
similar to the password entered to gain access to a secured workstation. Typ-
ically, this is in the form of a username such as: jdoe@amx.com.
Anonymous Identity: Opens an on-screen keyboard. Enter an IT provided alpha-numeric string
which (similar to the username) used as the identity, but that does not repre-
sent a real user.
This information is used as a fictitious name which might be seen by sniffer
programs during the initial connection and setup process between the panel
and the Radius server. In this way the real identity (username) is protected.
Typically, this is in the form of a fictitious username such as: anony-
mous@amx.com
Password: Opens an on-screen keyboard. Enter the network password string specified
for the user entered within the Identity field (used by the panel to identify itself
to an Authentication (RADIUS) Server)
Note: This information is similar to the password entered to gain access to a
secured workstation.
Certificate Authority: When pressed, the panel displays an on-screen Certificate Authority (CA)
File Location keyboard which allows you to enter the name of the certificate
authority file which is used to validate the server certificate.
This field is optional.
If a server certificate is used, it should first be downloaded into the panel and
the Certificate Authority field should then be set to the name of that certificate
file. No file path should be used for this setting as all certificates are stored in
a specific directory that the user cannot control or change.
• Use the on-screen keyboard’s Clear button to completely erase any
previously stored network path information.
Inner Authentication Type: When pressed, this field cycles through the choices of available Inner
Authentication mechanism supported by the Devicescape Secure Wireless
Client:
• MSCHAPv2 (default because its the most common)
• MSCHAP
•PAP
• CHAP
• EAP-MSCHAPv2
• EAP-GTC
• EAP-OTP
• EAP-MD5-Challenge
Save/Cancel: • Save - store the new security information, apply changes, and return to the
previous page.
• Cancel - discard changes and return to the previous page.


















