7-21
Using Passwords, Port Security, and Authorized IP Managers To Protect Against Unauthorized Access
Configuring and Monitoring Port Security
Using Passwords, Port
Security, and Authorized IP
How the Intrusion Log Operates
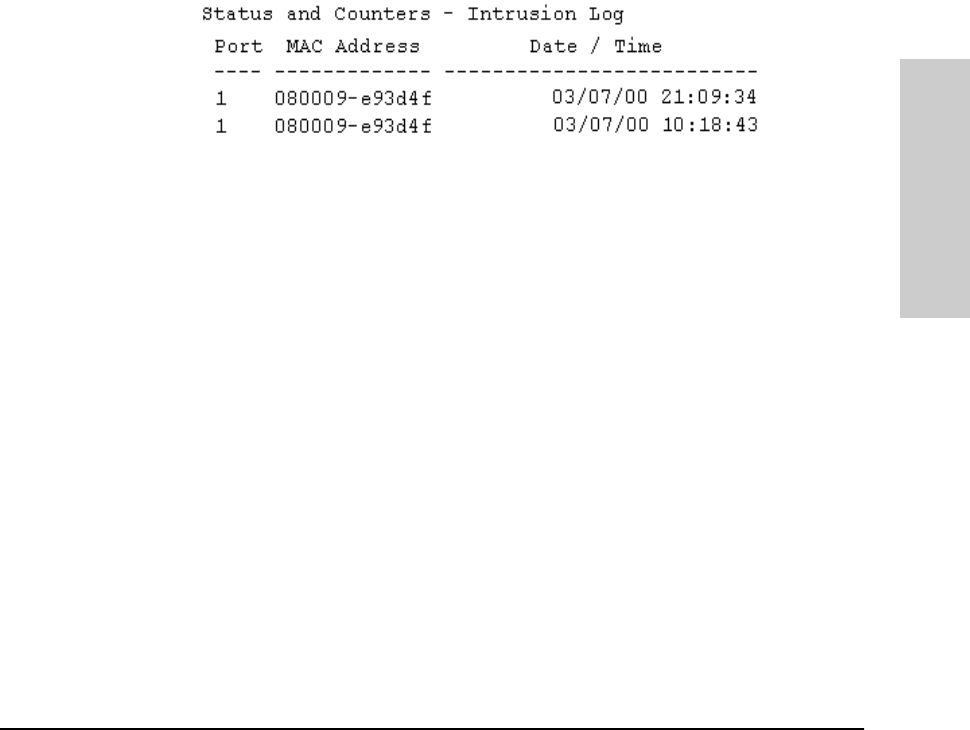
When the switch detects an intrusion attempt on a port, it enters a record of
this event in the Intrusion Log. No further intrusion attempts on that port will
appear in the Log until you acknowledge the earlier intrusion event by reset-
ting the alert flag.
The Intrusion Log lists the 20 most recently detected security violation
attempts, regardless of whether the alert flags for these attempts have been
reset. This gives you a history of past intrusion attempts. Thus, for example,
if there is an intrusion alert for port 1 and the Intrusion Log shows two or more
entries for port 1, only the most recent entry has not been acknowledged (by
resetting the alert flag). The other entries give you a history of past intrusions
detected on port 1.
Figure 7-6. Example of Multiple Intrusion Log Entries for the Same Port
The log shows the most recent intrusion at the top of the listing. You cannot
delete Intrusion Log entries (unless you reset the switch to its factory-default
configuration). Instead, if the log is filled when the switch detects a new
intrusion, the oldest entry is dropped off the listing and the newest entry
appears at the top of the listing.
Keeping the Intrusion Log Current by Resetting Alert Flags
When a violation occurs on a port, an alert flag is set for that port and the
violation is entered in the Intrusion Log. The switch can detect and handle
subsequent intrusions on that port, but will not log another intrusion on the
port until you reset the alert flag for either all ports or for the individual port.


















