ZyWALL 2 Series User’s Guide
VPN Screens 14-21
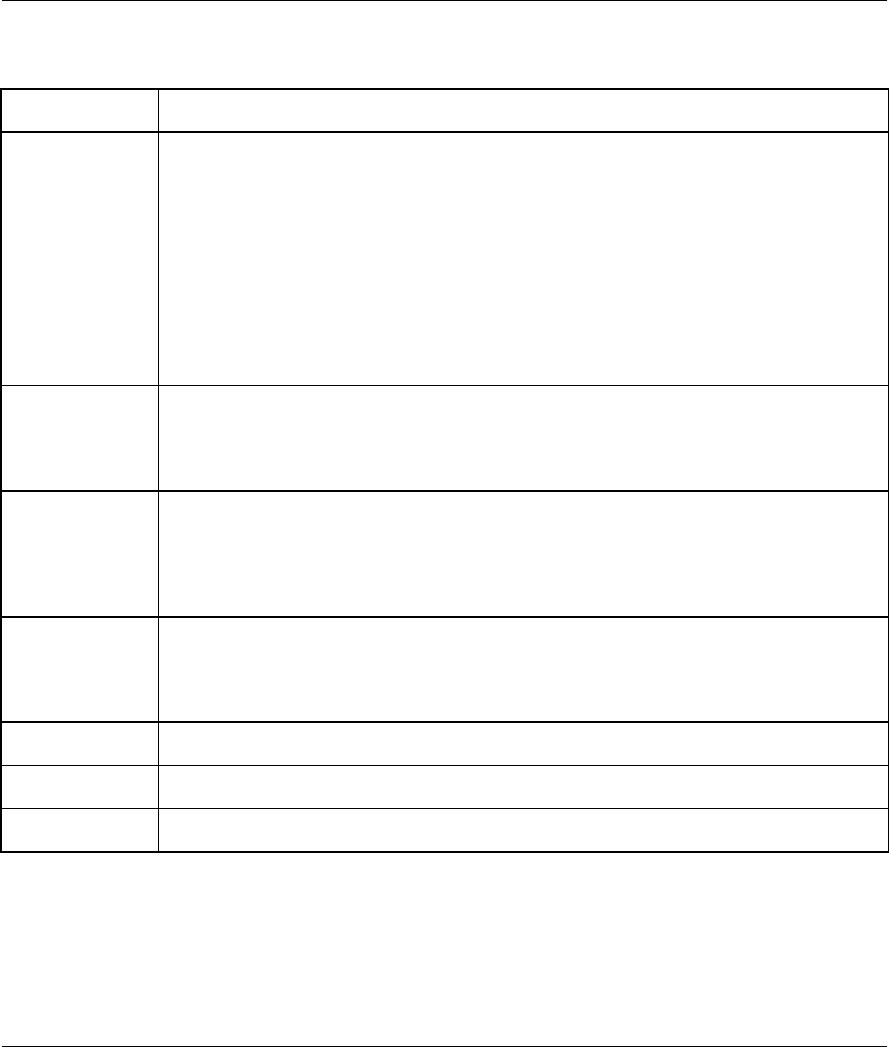
Table 14-7 Basic IKE VPN Rule Edit
LABEL DESCRIPTION
Encryption
Algorithm
Select DES, 3DES, AES or NULL from the drop-down list box.
When you use one of these encryption algorithms for data communications, both the
sending device and the receiving device must use the same secret key, which can be
used to encrypt and decrypt the message or to generate and verify a message
authentication code. The DES encryption algorithm uses a 56-bit key. Triple DES (3DES)
is a variation on DES that uses a 168-bit key. As a result, 3DES is more secure than DES.
It also requires more processing power, resulting in increased latency and decreased
throughput. This implementation of AES uses a 128-bit key. AES is faster than 3DES.
Select NULL to set up a tunnel without encryption. When you select NULL, you do not
enter an encryption key.
Authentication
Algorithm
Select SHA1 or MD5 from the drop-down list box. MD5 (Message Digest 5) and SHA1
(Secure Hash Algorithm) are hash algorithms used to authenticate packet data. The SHA1
algorithm is generally considered stronger than MD5, but is slower. Select MD5 for
minimal security and SHA-1 for maximum security.
AH
Select AH if you want to use AH (Authentication Header Protocol). The AH protocol (RFC
2402) was designed for integrity, authentication, sequence integrity (replay resistance),
and non-repudiation but not for confidentiality, for which the ESP was designed. If you
select AH here, you must select options from the Authentication Algorithm field
(described below).
Authentication
Algorithm
Select SHA1 or MD5 from the drop-down list box. MD5 (Message Digest 5) and SHA1
(Secure Hash Algorithm) are hash algorithms used to authenticate packet data. The SHA1
algorithm is generally considered stronger than MD5, but is slower. Select MD5 for
minimal security and SHA-1 for maximum security.
Advanced
Click Advanced to configure more detailed settings of your IKE key management.
Apply
Click Apply to save your customized settings and exit this screen.
Reset
Click Reset to begin configuring this screen afresh.
14.12 IKE Phases
There are two phases to every IKE (Internet Key Exchange) negotiation – phase 1 (Authentication) and phase
2 (Key Exchange). A phase 1 exchange establishes an IKE SA and the second one uses that SA to negotiate
SAs for IPSec.


















