xStack
®
DES-3200-10/18/28/28F Layer 2 Ethernet Managed Switch User Manual
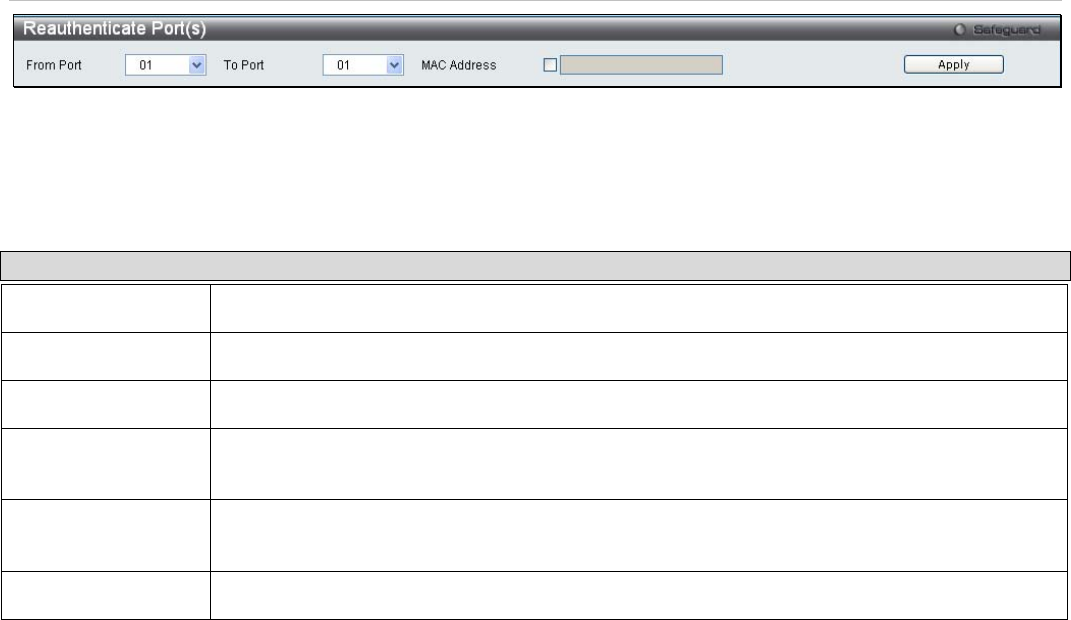
Figure 5 - 27. Reauthenticate Port(s) window for MAC-based 802.1X
To reauthenticate ports, first use the From Port and To Port drop-down menus to choose the range of ports. Then the
user must specify the MAC address to be reauthenticated by entering it into the MAC Address field and ticking the
corresponding check box. To begin the reauthentication, click Apply.
This window displays the following information:
Parameter Description
From Port
The beginning port in a range of ports to be reauthenticated.
To Port
The ending port in a range of ports to be reauthenticated.
MAC Address
Displays the physical address of the Switch where the port resides.
Auth PAE State
The Authenticator State will display one of the following: Initialize, Disconnected, Connecting,
Authenticating, Authenticated, Aborting, Held, ForceAuth, ForceUnauth, and N/A.
Backend_State
The Backend State will display one of the following: Request, Response, Success, Fail,
Timeout, Idle, Initialize, and N/A.
Port Status
The status of the controlled port can be Authorized, Unauthorized, or N/A.
SSL Settings
Secure Sockets Layer or SSL is a security feature that will provide a secure communication path between a host and
client through the use of authentication, digital signatures and encryption. These security functions are implemented
through the use of a ciphersuite, which is a security string that determines the exact cryptographic parameters,
specific encryption algorithms and key sizes to be used for an authentication session and consists of three levels:
1. Key Exchange: The first part of the cyphersuite string specifies the public key algorithm to be used. This
switch utilizes the Rivest Shamir Adleman (RSA) public key algorithm and the Digital Signature Algorithm
(DSA), specified here as the DHE DSS Diffie-Hellman (DHE) public key algorithm. This is the first
authentication process between client and host as they “exchange keys” in looking for a match and therefore
authentication to be accepted to negotiate encryptions on the following level.
2. Encryption: The second part of the ciphersuite that includes the encryption used for encrypting the messages
sent between client and host. The Switch supports two types of cryptology algorithms:
• Stream Ciphers – There are two types of stream ciphers on the Switch, RC4 with 40-bit keys and RC4
with 128-bit keys. These keys are used to encrypt messages and need to be consistent between
client and host for optimal use.
• CBC Block Ciphers – CBC refers to Cipher Block Chaining, which means that a portion of the
previously encrypted block of encrypted text is used in the encryption of the current block. The Switch
supports the 3DES EDE encryption code defined by the Data Encryption Standard (DES) to create
the encrypted text.
3. Hash Algorithm: This part of the ciphersuite allows the user to choose a message digest function which will
determine a Message Authentication Code. This Message Authentication Code will be encrypted with a sent
message to provide integrity and prevent against replay attacks. The Switch supports two hash algorithms,
MD5 (Message Digest 5) and SHA (Secure Hash Algorithm).
These three parameters are uniquely assembled in four choices on the Switch to create a three-layered encryption
code for secure communication between the server and the host. The user may implement any one or combination of
the ciphersuites available, yet different ciphersuites will affect the security level and the performance of the secured
connection. The information included in the ciphersuites is not included with the Switch and requires downloading from
a third source in a file form called a certificate. This function of the Switch cannot be executed without the presence
and implementation of the certificate file and can be downloaded to the Switch by utilizing a TFTP server. The Switch
133


















