DES-3010F/DES-3010FL/DES-3010G/DES-3016/DES-3018/DES-3026 Fast Ethernet Switch Manual
143
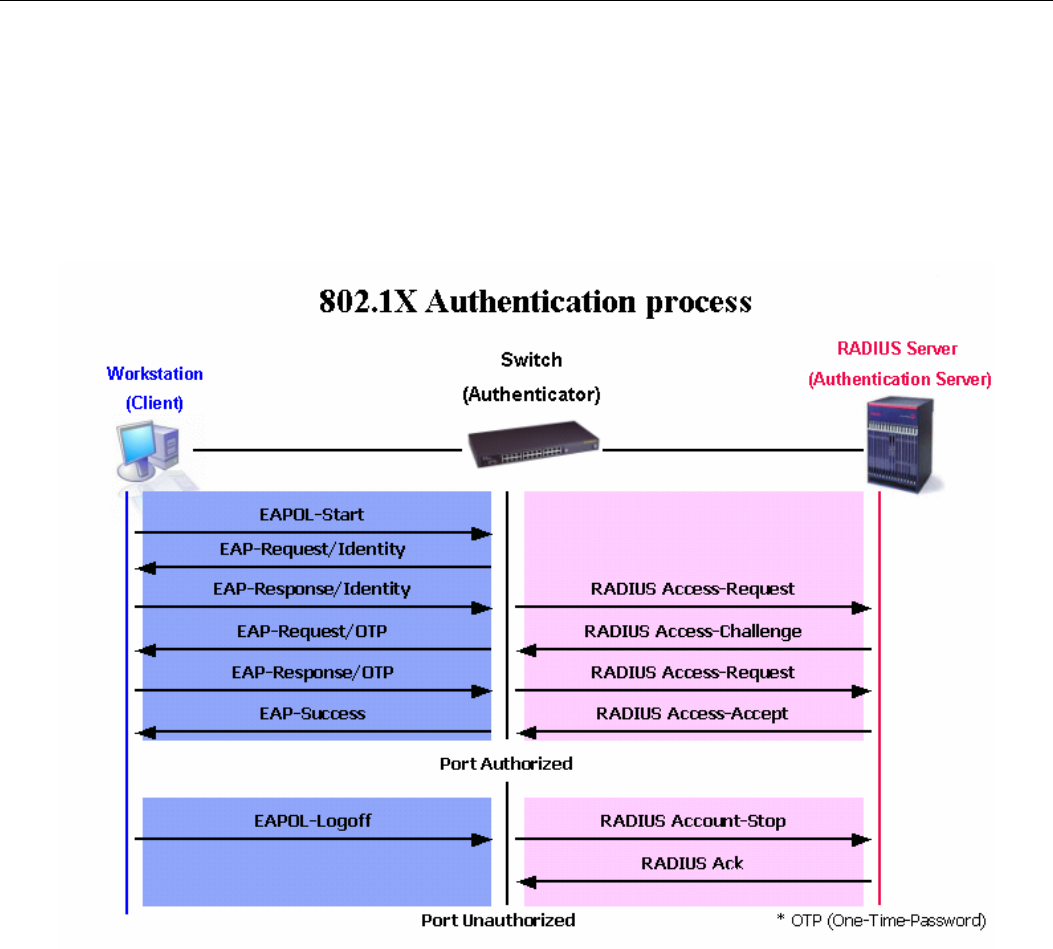
Authentication Process
Utilizing the three roles stated above, the 802.1X protocol provides a stable and secure way of authorizing
and authenticating users attempting to access the network. Only EAPOL traffic is allowed to pass through
the specified port before a successful authentication is made. This port is “locked” until the point when a
Client with the correct username and password (and MAC address if 802.1X is enabled by MAC address) is
granted access and therefore successfully “unlocks” the port. Once the port is unlocked, normal traffic is
allowed to pass through the port. The following figure displays a more detailed explanation of how the
authentication process is completed between the three roles stated above.
Figure 10- 9. The 802.1X Authentication Process
The D-Link implementation of 802.1X allows network administrators to choose between two types of
Access Control used on the Switch, which are:
1. Port-Based Access Control – This method requires only one user to be authenticated per port by a
remote RADIUS server to allow the remaining users on the same port access to the network.
2. MAC-Based Access Control – Using this method, the Switch will automatically learn up to eight
MAC addresses by port and set them in a list. Each MAC address must be authenticated by the
Switch using a remote RADIUS server before being allowed access to the Network.


















