C
ONFIGURING
THE
S
WITCH
3-60
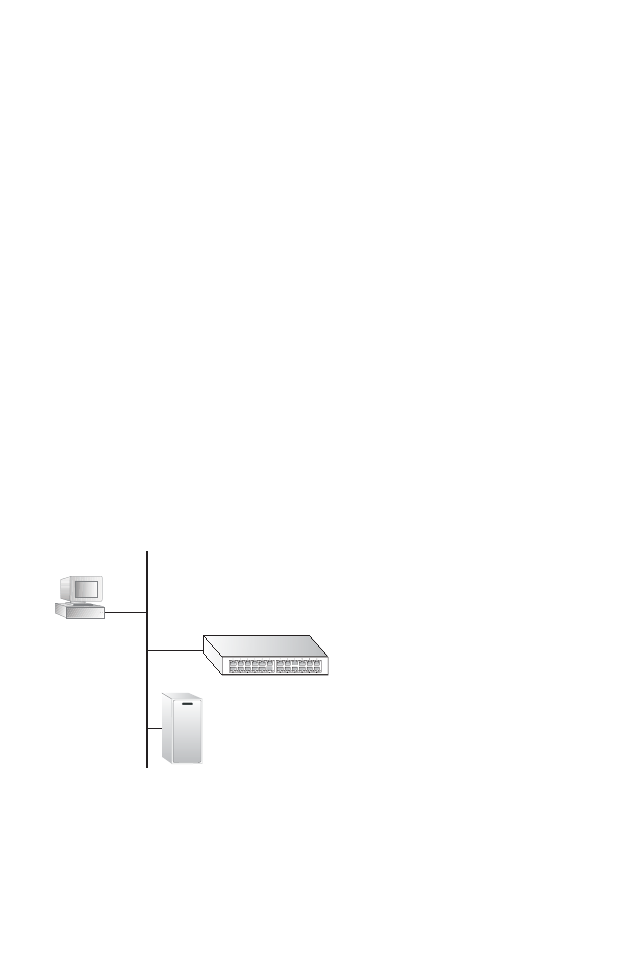
This switch uses the Extensible Authentication Protocol over LANs
(EAPOL) to exchange authentication protocol messages with the client,
and a remote RADIUS authentication server to verify user identity and
access rights. When a client (i.e., Supplicant) connects to a switch port, the
switch (i.e., Authenticator) responds with an EAPOL identity request. The
client provides its identity (such as a user name) in an EAPOL response to
the switch, which it forwards to the RADIUS server. The RADIUS server
verifies the client identity and sends an access challenge back to the client.
The EAP packet from the RADIUS server contains not only the challenge,
but the authentication method to be used. The client can reject the
authentication method and request another, depending on the
configuration of the client software and the RADIUS server. The current
version of the firmware supports only the MD5 authentication method.
The client responds to the appropriate method with its credentials, such as
a password or certificate. The RADIUS server verifies the client
credentials and responds with an accept or reject packet. If authentication
is successful, the switch allows the client to access the network. Otherwise,
network access is denied and the port remains blocked.
The operation of 802.1x on the switch requires the following:
• The switch must have an IP address assigned.
• RADIUS authentication must be enabled on the switch and the IP
address of the RADIUS server specified.
• Each switch port that will be used must be set to dot1x “Auto” mode.
802.1x
client
RADIUS
server
1. Client attempts to access a switch port.
2. Switch sends client an identity request.
3. Client sends back identity information.
4. Switch forwards this to authentication server.
5.Authentication server challenges client.
6. Client responds with proper credentials.
7.Authentication server approves access.
8. Switch grants client access to this port.


















