ES-3124PWR Ethernet Switch
17-6 Access Control
Table 17-5 Access Control: Logins
LABEL DESCRIPTION
Apply Click Apply to save your changes back to the switch.
Cancel Click Cancel to begin configuring this screen afresh.
17.4 SSH Overview
Unlike Telnet or FTP, which transmit data in clear text, SSH (Secure Shell) is a secure communication protocol that
combines authentication and data encryption to provide secure encrypted communication between two hosts over
an unsecured network.
Figure 17-6 SSH Communication Example
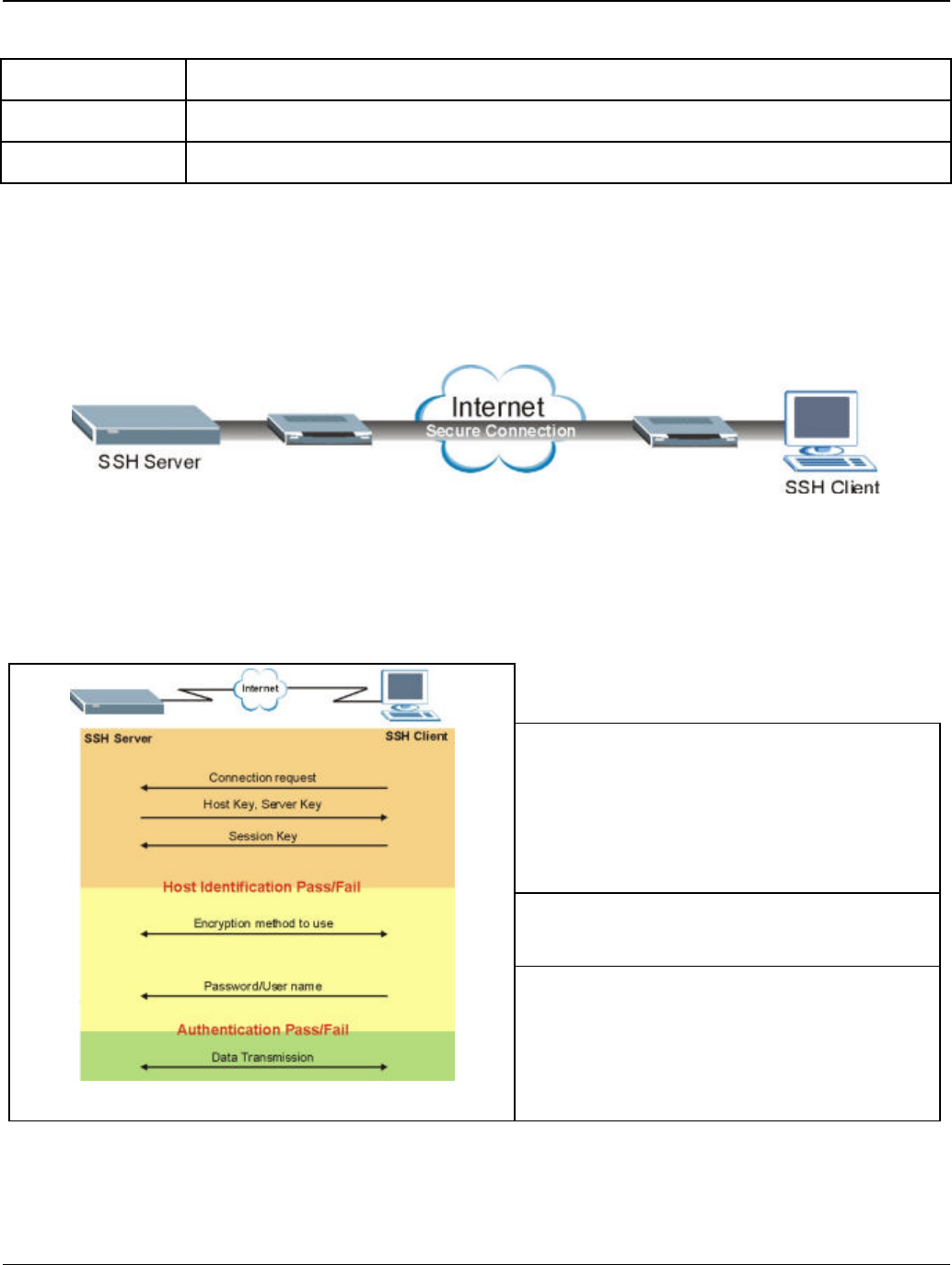
17.5 How SSH works
The following table summarizes how a secure connection is established between two remote hosts.
1. Host Identification
The SSH client sends a connection request to the SSH
server. The server identifies itself with a host key. The client
encrypts a randomly generated session key with the host key
and server key and sends the result back to the server.
The client automatically saves any new server public keys. In
subsequent connections, the server public key is checked
against the saved version on the client computer.
2. Encryption Method
Once the identification is verified, both the client and server
must agree on the type of encryption method to use.
Figure 17-7How SSH Works
3. Authentication and Data Transmission
After the identification is verified and data encryption
activated, a secure tunnel is established between the client
and the server. The client then sends its authentication
information (user name and password) to the server to log in
to the server.


















