19-5
Cisco ASA Series Firewall ASDM Configuration Guide
Chapter 19 Configuring Cisco Mobility Advantage
Information about the Cisco Mobility Advantage Proxy Feature
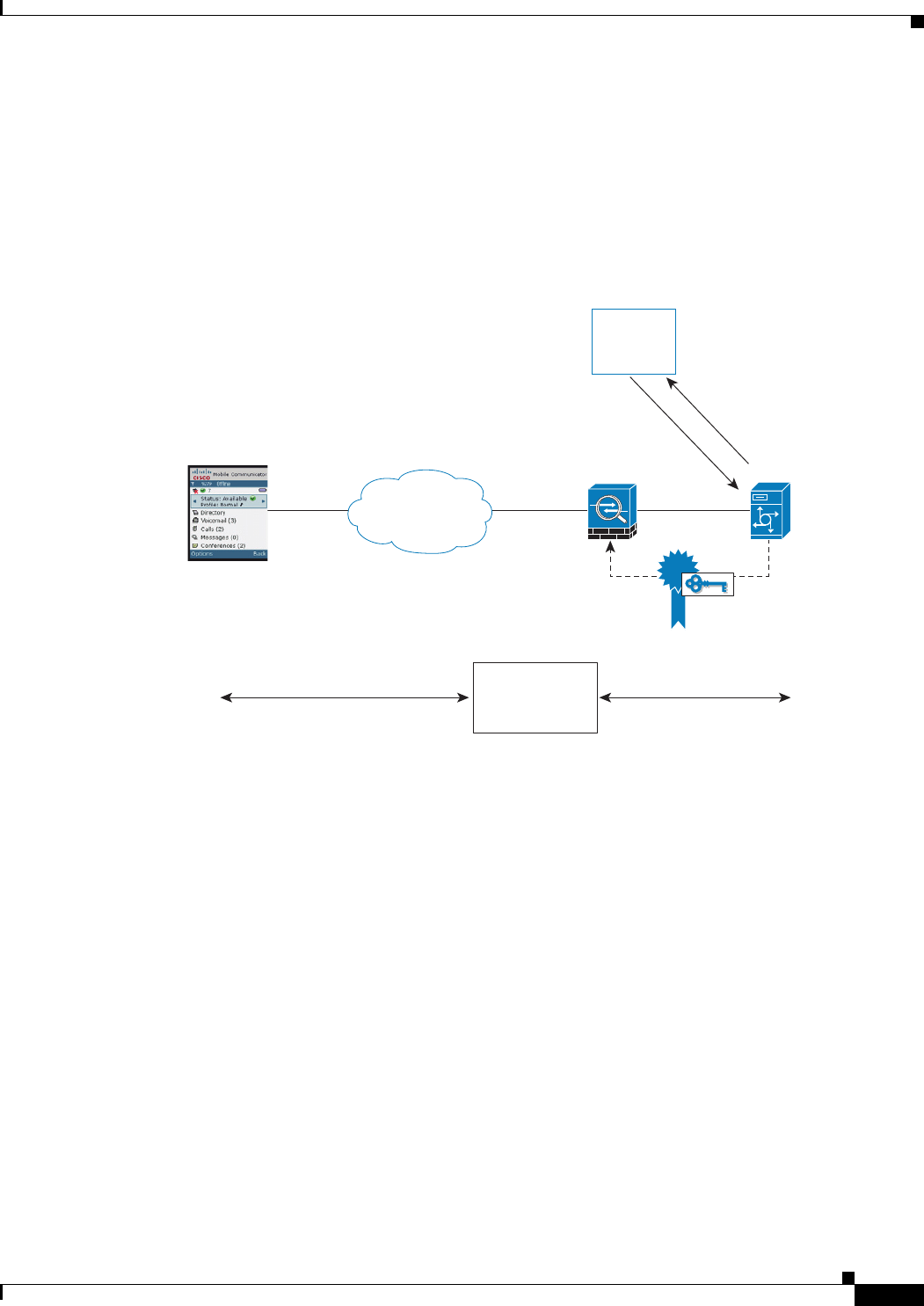
Figure 19-4 shows how you can import the Cisco UMA server certificate onto the ASA. When the Cisco
UMA server has already enrolled with a third-party CA, you can import the certificate with the private
key onto the ASA. Then, the ASA has the full credentials of the Cisco UMA server. When a Cisco UMA
client connects to the Cisco UMA server, the ASA intercepts the handshake and uses the Cisco UMA
server certificate to perform the handshake with the client. The ASA also performs a handshake with the
server.
Figure 19-4 How the Security Appliance Represents Cisco UMA – Private Key Sharing
Figure 19-5 shows another way to establish the trust relationship. Figure 19-5 shows a green field
deployment, because each component of the deployment has been newly installed. The ASA enrolls with
the third-party CA by using the Cisco UMA server FQDN as if the ASA is the Cisco UMA server. When
the Cisco UMA client connects to the ASA, the ASA presents the certificate that has the Cisco UMA
server FQDN. The Cisco UMA client believes it is communicating to with the Cisco UMA server.
271643
Internet
Inspected and
Modified
(if needed)
Certificate
Authority
Certificate
Certificate with
Private Key
ASA
Enroll with FQDN
of Cisco UMA
Key 1
Key 2
TLS (Self-signed,
or from local CA)
TLS (Cisco UMA Certificate)
3rd Party CA
Cisco UMA
Cisco UMC Client


















