xStack
®
DES-3200-10/18/28/28F Layer 2 Ethernet Managed Switch User Manual
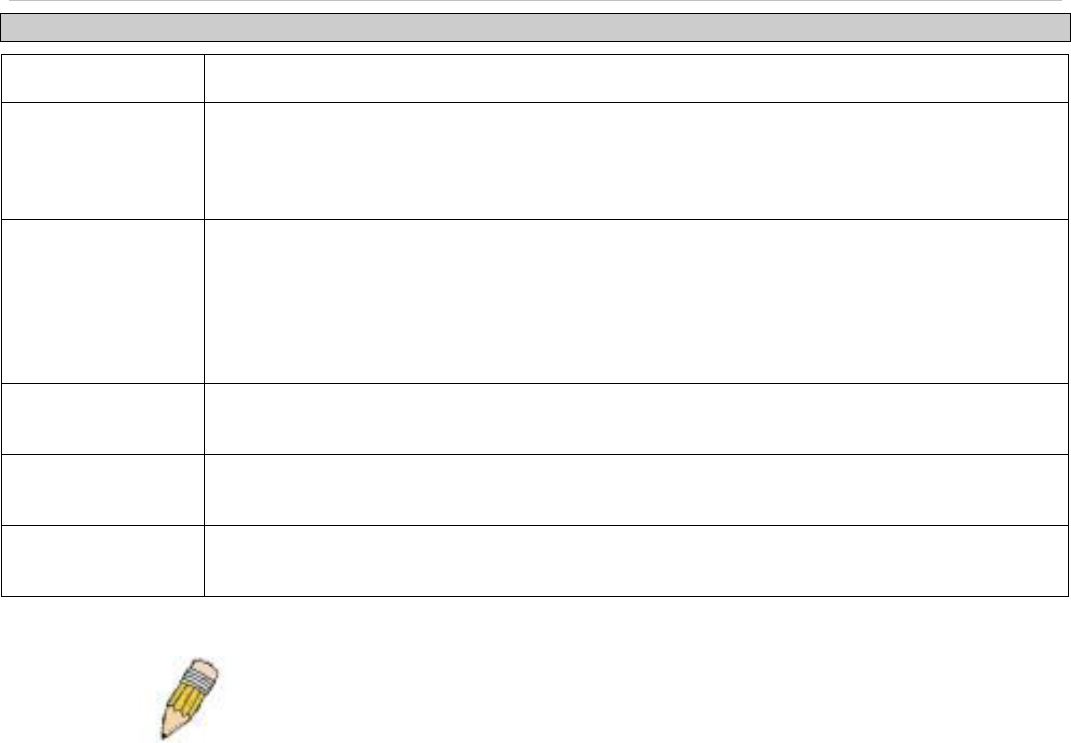
Parameter Description
IP Address
The IP address of the remote server host the user wishes to add.
Port (1-65535)
Enter a number between 1 and 65535 to define the virtual port number of the authentication
protocol on a server host. The default port number is 49 for TACACS/XTACACS/TACACS+
servers and 1813 for RADIUS servers but the user may set a unique port number for higher
security.
Protocol
The protocol used by the server host. The user may choose one of the following:
TACACS - Enter this parameter if the server host utilizes the TACACS protocol.
XTACACS - Enter this parameter if the server host utilizes the XTACACS protocol.
TACACS+ - Enter this parameter if the server host utilizes the TACACS+ protocol.
RADIUS - Enter this parameter if the server host utilizes the RADIUS protocol.
Timeout (1-255)
Enter the time in seconds the Switch will wait for the server host to reply to an authentication
request. The default value is 5 seconds.
Key
Authentication key to be shared with a configured TACACS+ or RADIUS servers only. Specify
an alphanumeric string up to 254 characters.
Retransmit (1-255)
Enter the value in the retransmit field to change how many times the device will resend an
authentication request when the server does not respond.
Click Apply to add the server host. Entries will be displayed in the table on the lower half of this window.
NOTE: More than one authentication protocol can be run on the same
physical server host but, remember that TACACS/XTACACS/TACACS+
are separate entities and are not compatible with each other
Login Method Lists
This window is used to configure a user-defined or default Login Method List of authentication techniques for users
logging on to the Switch. The sequence of techniques implemented in this command will affect the authentication
result. For example, if a user enters a sequence of techniques, for example TACACS – XTACACS - local, the Switch
will send an authentication request to the first TACACS host in the server group. If no response comes from the server
host, the Switch will send an authentication request to the second TACACS host in the server group and so on, until
the list is exhausted. At that point, the Switch will restart the same sequence with the following protocol listed,
XTACACS. If no authentication takes place using the XTACACS list, the local account database set in the Switch is
used to authenticate the user. When the local method is used, the privilege level will be dependant on the local
account privilege configured on the Switch.
When the user logins to the device successfully through TACACS/XTACACS/TACACS+server or none method, the
“user” privilege level is assigned only. If the user wants to get admin privilege level, the user must use the Enable
Admin window to promote his privilege level. (See the Enable Admin part of this section for more detailed information.)
But when the user logins to the device successfully through RADIUS server or local method, three kinds of privilege
levels can be assigned to the user and the user can not use the Enable Admin window to promote to admin privilege
level.
To view the following window, click Security > Access Authentication Control > Login Method Lists:
143


















