19-8
Cisco ME 3400 Ethernet Access Switch Software Configuration Guide
78-17058-01
Chapter 19 Configuring Dynamic ARP Inspection
Configuring Dynamic ARP Inspection
To disable dynamic ARP inspection, use the no ip arp inspection vlan vlan-range global configuration
command. To return the interfaces to an untrusted state, use the no ip arp inspection trust interface
configuration command.
This example shows how to configure dynamic ARP inspection on Switch A in VLAN 1. You would
perform a similar procedure on Switch B:
Switch(config)# ip arp inspection vlan 1
Switch(config)# interface gigabitethernet0/1
Switch(config-if)# ip arp inspection trust
Configuring ARP ACLs for Non-DHCP Environments
This procedure shows how to configure dynamic ARP inspection when Switch B shown in Figure 19-2
on page 19-3 does not support dynamic ARP inspection or DHCP snooping.
If you configure port 1 on Switch A as trusted, a security hole is created because both Switch A and
Host 1 could be attacked by either Switch B or Host 2. To prevent this possibility, you must configure
port 1 on Switch A as untrusted. To permit ARP packets from Host 2, you must set up an ARP ACL and
apply it to VLAN 1. If the IP address of Host 2 is not static (it is impossible to apply the ACL
configuration on Switch A) you must separate Switch A from Switch B at Layer 3 and use a router to
route packets between them.
Beginning in privileged EXEC mode, follow these steps to configure an ARP ACL on Switch A. This
procedure is required in non-DHCP environments.
Step 7
end Return to privileged EXEC mode.
Step 8
show ip arp inspection interfaces
show ip arp inspection vlan vlan-range
Verify the dynamic ARP inspection configuration.
Step 9
show ip dhcp snooping binding Verify the DHCP bindings.
Step 10
show ip arp inspection statistics vlan
vlan-range
Check the dynamic ARP inspection statistics.
Step 11
copy running-config startup-config (Optional) Save your entries in the configuration file.
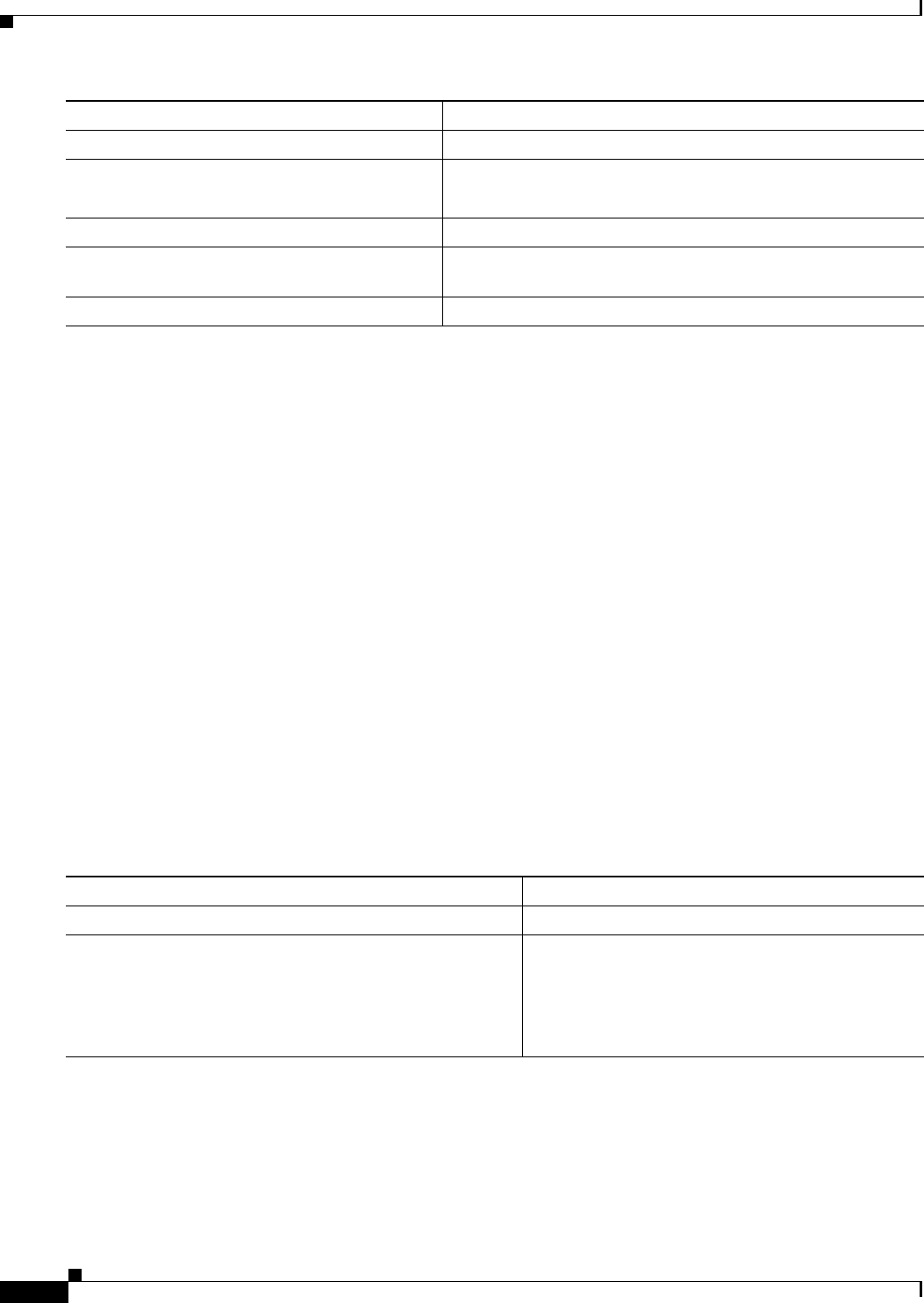
Command Purpose
Command Purpose
Step 1
configure terminal Enter global configuration mode.
Step 2
arp access-list acl-name Define an ARP ACL, and enter ARP access-list
configuration mode. By default, no ARP access lists
are defined.
Note At the end of the ARP access list, there is an
implicit deny ip any mac any command.


















