28-5
Cisco ME 3400 Ethernet Access Switch Software Configuration Guide
78-17058-01
Chapter 28 Configuring Network Security with ACLs
Understanding ACLs
As with port ACLs, the switch examines ACLs associated with features configured on a given interface.
However, router ACLs are supported in both directions. As packets enter the switch on an interface,
ACLs associated with all inbound features configured on that interface are examined. After packets are
routed and before they are forwarded to the next hop, all ACLs associated with outbound features
configured on the egress interface are examined.
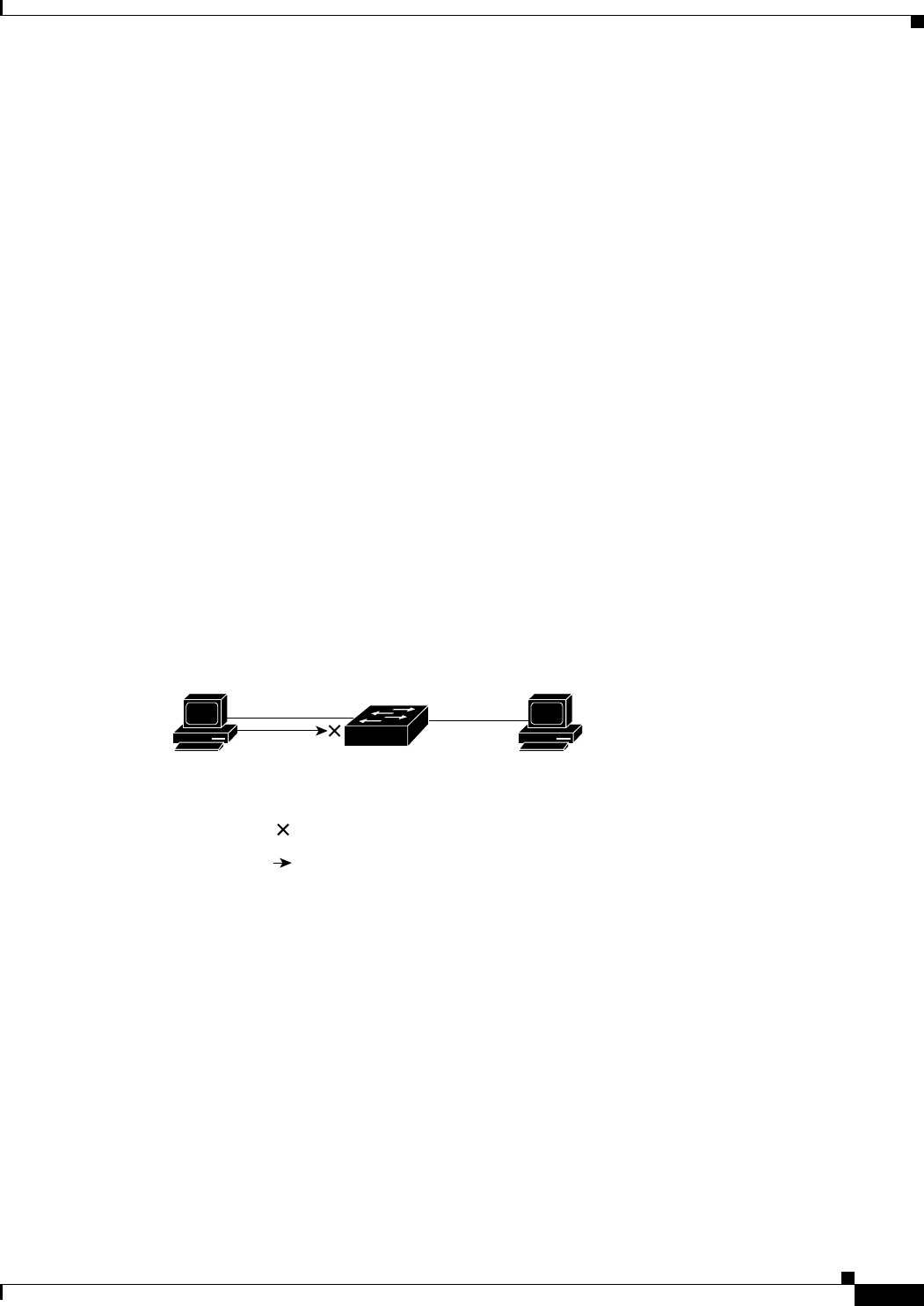
ACLs permit or deny packet forwarding based on how the packet matches the entries in the ACL, and
can be used to control access to a network or to part of a network. In Figure 28-1, ACLs applied at the
router input allow Host A to access the Human Resources network, but prevent Host B from accessing
the same network.
VLAN Maps
VLAN ACLs or VLAN maps can access-control all traffic. You can apply VLAN maps to all packets
that are routed into or out of a VLAN or are forwarded within a VLAN in the switch. VLAN maps are
used for security packet filtering and are not defined by direction (input or output).
You can configure VLAN maps to match Layer 3 addresses for IPv4 traffic.
All non-IP protocols are access-controlled through MAC addresses and Ethertype using MAC VLAN
maps. (IP traffic is not access controlled by MAC VLAN maps.) You can enforce VLAN maps only on
packets going through the switch; you cannot enforce VLAN maps on traffic between hosts on a hub or
on another switch connected to this switch.
With VLAN maps, forwarding of packets is permitted or denied, based on the action specified in the
map. Figure 28-2 shows how a VLAN map is applied to prevent a specific type of traffic from Host A in
VLAN 10 from being forwarded. You can apply only one VLAN map to a VLAN.
Figure 28-2 Using VLAN Maps to Control Traffic
Handling Fragmented and Unfragmented Traffic
IPv4 packets can be fragmented as they cross the network. When this happens, only the fragment
containing the beginning of the packet contains the Layer 4 information, such as TCP or UDP port
numbers, ICMP type and code, and so on. All other fragments are missing this information.
Host B
(VLAN 10)
Host A
(VLAN 10)
92919
= VLAN map denying specific type
of traffic from Host A
= Packet


















