88
Enhancements in Release F.04.08
Configuring Secure Shell (SSH)
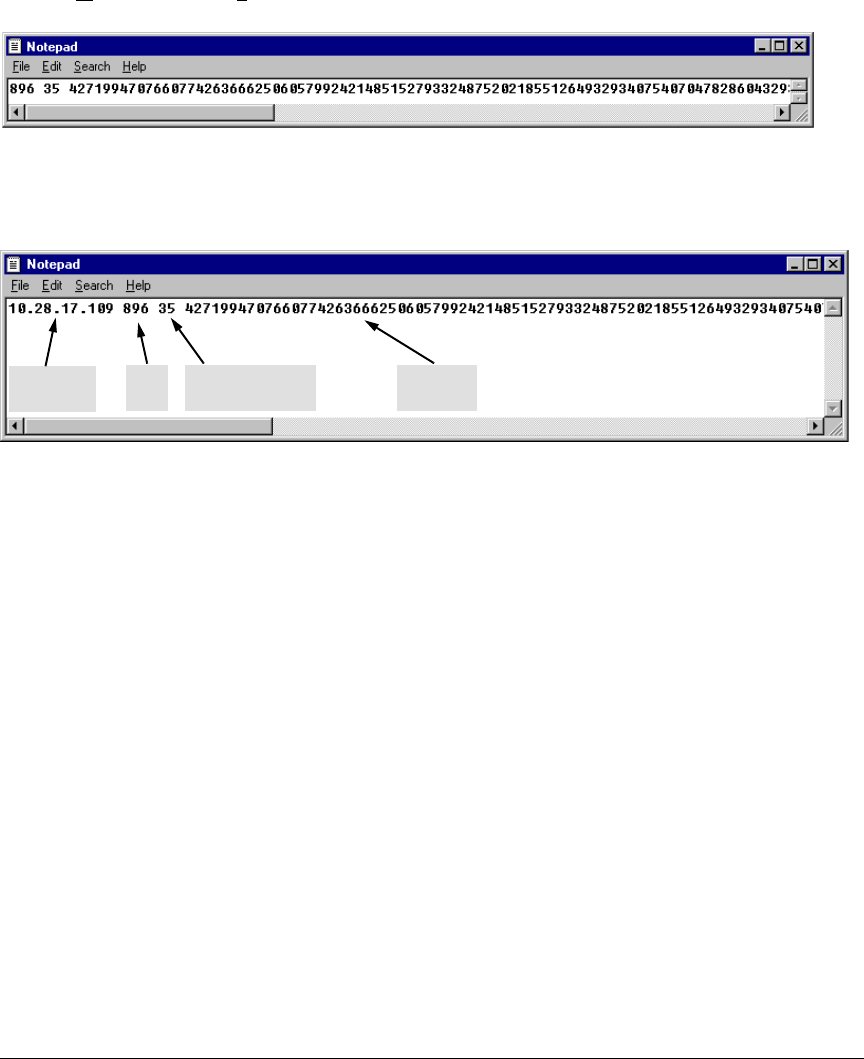
3. Ensure that there are no line breaks in the text string. (A public key must be an unbroken ASCII
string. Line breaks are not allowed.) For example, if you are using Windows® Notepad, ensure
that W
ord Wrap (in the Edit menu) is disabled, and that the key text appears on a single line.
Figure 33. Example of a Correctly Formatted Public Key (Unbroken ASCII String)
4. Add any data required by your SSH client application. For example Before saving the key to an
SSH client’s "known hosts" file you may have to insert the switch’s IP address:
Figure 34. Example of a Switch Public Key Edited To Include the Switch’s IP Address
For more on this topic, refer to the documentation provided with your SSH client application.
Displaying the Public Key. The switch provides three options for displaying its public key. This is
helpful if you need to visually verify that the public key the switch is using for authenticating itself
to a client matches the copy of this key in the client’s "known hosts" file:
■ Non-encoded ASCII numeric string: Requires a client ability to display the keys in the
"known hosts" file in the ASCII format. This method is tedious and error-prone due to the
large ASCII number set. (See figure 33 on page 88.)
■ Phonetic hash: Outputs the key as a relatively short series of alphabetic character groups.
Requires a client ability to convert the key to this format.
■ Hexadecimal hash: Outputs the key as a relatively short series of hexadecimal numbers.
Requires a parallel client ability.
For example, on the switch, you would generate the phonetic and hexadecimal versions of the
switch’s public key in figure 33 as follows:
Key
Size
Encoded
Public Exponent
Encoded
Modulus
Inserted IP
Address


















