Management and Monitoring
89
ProSafe Premium 3 x 3 Dual-Band Wireless-N Access Point WNDAP620
Configure Wireless Intrusion Detection and Prevention
• Configure Wireless Intrusion Detection and Prevention Policy Settings
• Configure Wireless Intrusion Detection and Prevention Mail Settings
• Monitor Traps, Counters, and Ad Hoc Networks
Configure Wireless Intrusion Detection and Prevention Policy
Settings
The wireless access point provides a wireless intrusion detection system (WIDS) and
wireless intrusion prevention system (WIPS) to detect and mitigate wireless attacks. These
intrusion systems are referred to as IDS/IPS.
If enabled, the IDS recognizes multiple types of wireless attacks, and the IPS automatically
n
eutralizes many attacks. Attacks are covered by preconfigured policy rules. When an attack
occurs, the wireless access point can notify a network administrator though an email.
The following table lists all IDS/IPS policies with
their policy rules. Most of these policies
provide protection against denial of service (DoS) attacks. You can enable or disable IDS/IPS
policies, but both the policies and the policy rules are not configurable.
All thresholds are measured over a short period. For the IDS/IPS to send a notification according
to th
e policy rule, you first need to configure the email settings (see Configure Wireless Intrusion
Detection and Prevention Mail Settings on p
age 95).
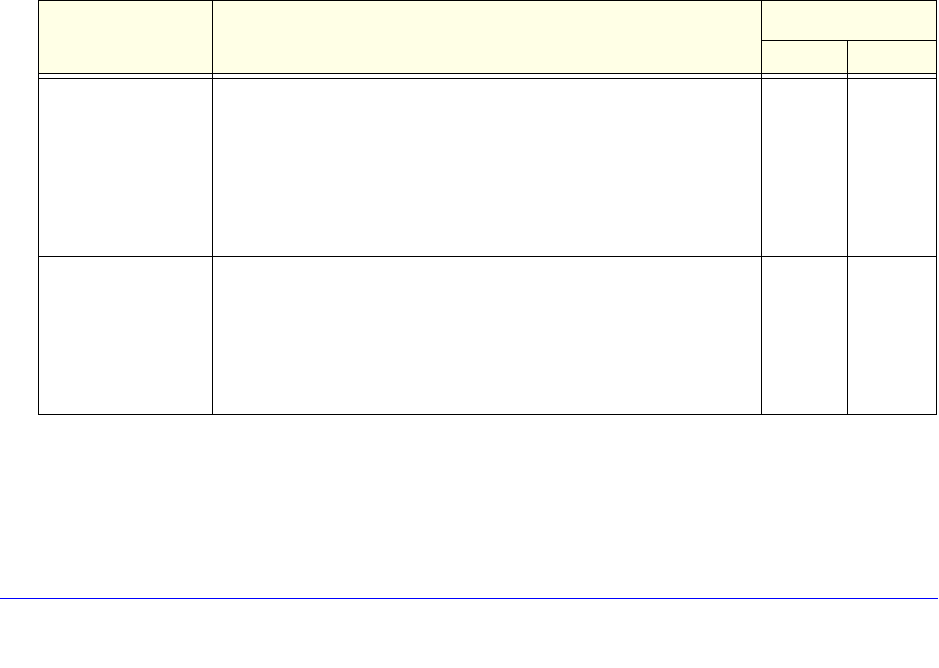
Table 24. IDS/IPS policies and policy rules
Policy Description Policy Rule
Threshold Notification
Authentication flood • Attack. Multiple authentication requests (5 or more) that use
spoofed MAC addresses of legitimate clients are sent to the
wireless access point.
• Res
ult. The client association table overflows, causing
authentication requests from legitimate clients to be denied.
• Solution.
The oldest clients that are stuck in the authentication
phase are removed from the table.
5 Trap
Association flood • Attack. Multiple association requests (5 or more) that use
spoofed MAC addresses of legitimate clients are sent to the
wireless access point.
• Res
ult. The client association table overflows, causing
association requests from legitimate clients to be denied.
• Solution. T
he oldest associations are removed from the table.
5 Trap


















