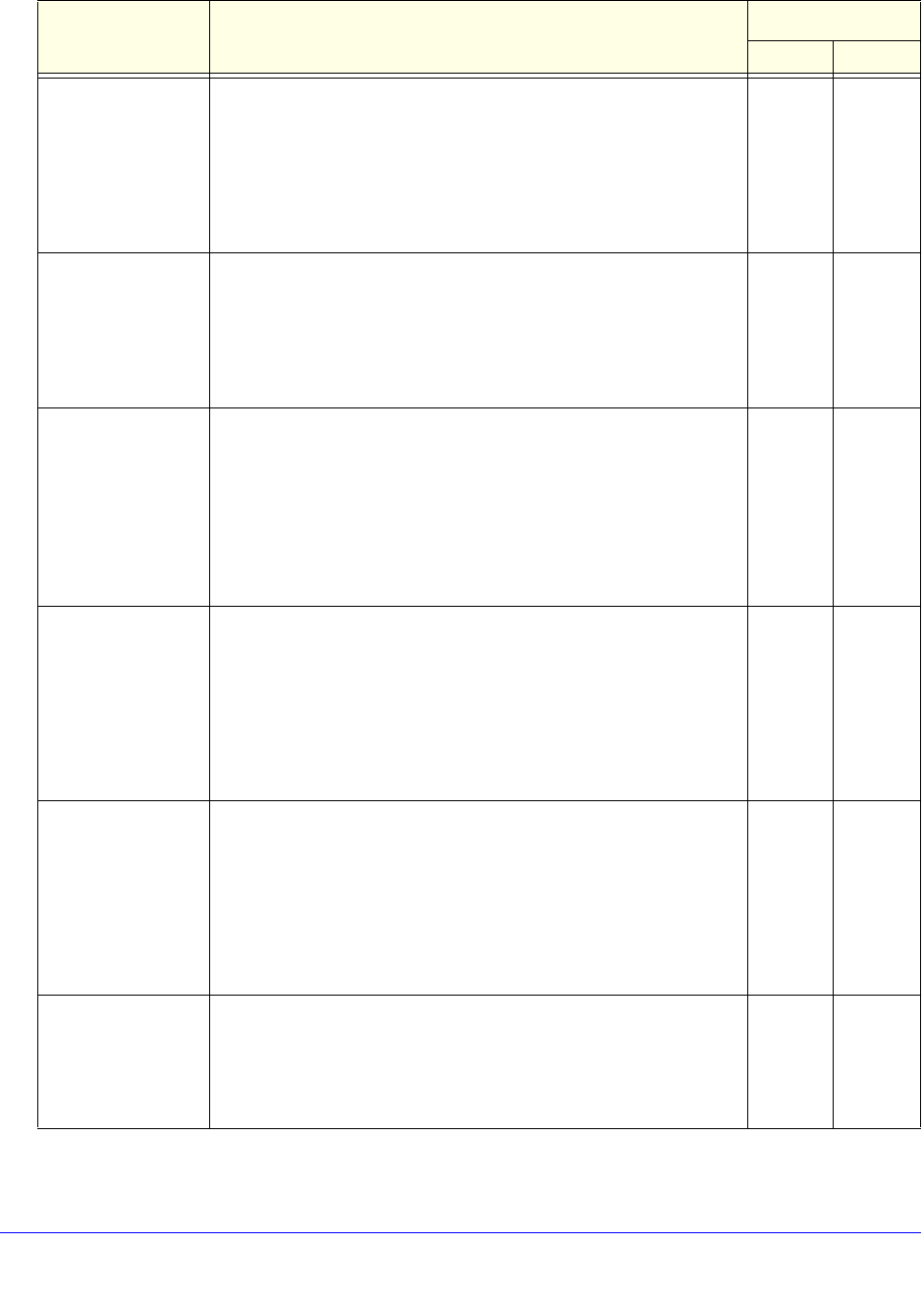
Management and Monitoring
90
ProSafe Premium 3 x 3 Dual-Band Wireless-N Access Point WNDAP620
Unauthenticated
association
• Attack. Multiple unauthenticated association requests (5 or
more) that use spoofed MAC addresses of legitimate clients are
sent to the wireless access point.
• R
esult. The client association table overflows, causing
authentication requests from legitimate clients to be denied.
• Solution. T
he oldest clients that are stuck in the authentication
phase are removed from the table.
5 Trap
Association table
o
verflow
• Attack. Multiple clients (5 or more) that use spoofed MAC
addresses of legitimate clients attempt to connect to the
wireless access point.
• R
esult. The client association table overflows, causing
association requests from legitimate clients to be denied.
• Solution. T
he oldest associations are removed from the table.
5 Trap
Authentication
fail
ure attack
• Attack. Multiple invalid authentication requests (5 or more) that
use the spoofed MAC address of a legitimate client are sent to
the wireless access point.
• R
esult. The client is disconnected from the wireless access
point.
• Solution. Th
e wireless access point determines if the legitimate
client is already connected before processing an authentication
request.
5 Trap
Deauthentication
bro
adcast attack
• Attack. Multiple deauthentication frames (5 or more) that use
the spoofed MAC address of the wireless access point are sent
to legitimate clients.
• R
esult. Clients are disconnected from the wireless access
point.
Note: The IDS detects this attack, but the IPS does not take action
a
gainst this attack.
5 Trap
Disassociation flood • At
tack. Multiple disassociation frames (5 or more) that use the
spoofed MAC address of the wireless access point are sent to a
legitimate client.
• R
esult. The client is disconnected from the wireless access
point.
Note: The IDS detects this attack, but the IPS does not take action
a
gainst this attack.
5 Trap
Malformed 802.11
p
ackets detected
• Detection. Multiple malformed packets (5 or more) are sent to
the wireless access point.
• R
esult. Clients behave unexpectedly or crash.
• Solution. The
wireless access point drops the malformed
packets.
5 Trap
Table 24. IDS/IPS policies and policy rules (continued)
Policy Description Policy Rule
Threshold Notification


















