C
ONFIGURING
THE
S
WITCH
3-82
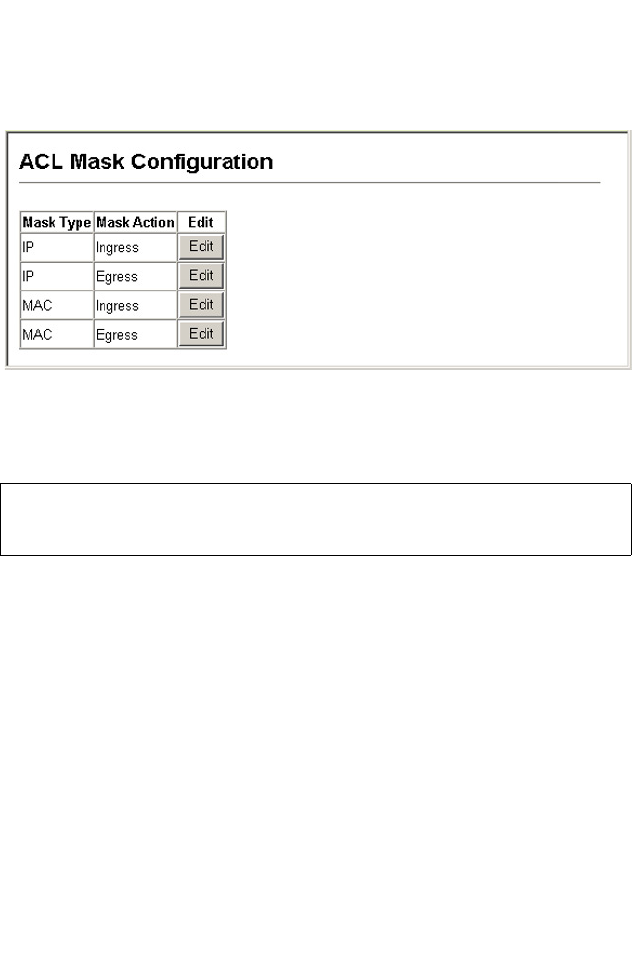
Web – Click Security, ACL, ACL Mask Configuration. Click Edit for one
of the basic mask types to open the configuration page.
CLI – This example creates an IP ingress mask, and then adds two rules.
Each rule is checked in order of precedence to look for a match in the
ACL entries. The first entry matching a mask is applied to the inbound
packet.
Configuring an IP ACL Mask
This mask defines the fields to check in the IP header.
Command Usage
• Masks that include an entry for a Layer 4 protocol source port or
destination port can only be applied to packets with a header length of
exactly five bytes.
Command Attributes
• Src/Dst IP – Specifies the source or destination IP address. Use
“Any” to match any address, “Host” to specify a host address (not a
subnet), or “IP” to specify a range of addresses. (Options: Any, Host,
IP; Default: Any)
• Src/Dst IP Bitmask – Source or destination address of rule must
Console(config)#access-list ip mask-precedence in3-121
Console(config-ip-mask-acl)#mask host any3-122
Console(config-ip-mask-acl)#mask 255.255.255.0 any
Console(config-ip-mask-acl)#


















