C
ONFIGURING
THE
S
WITCH
3-6
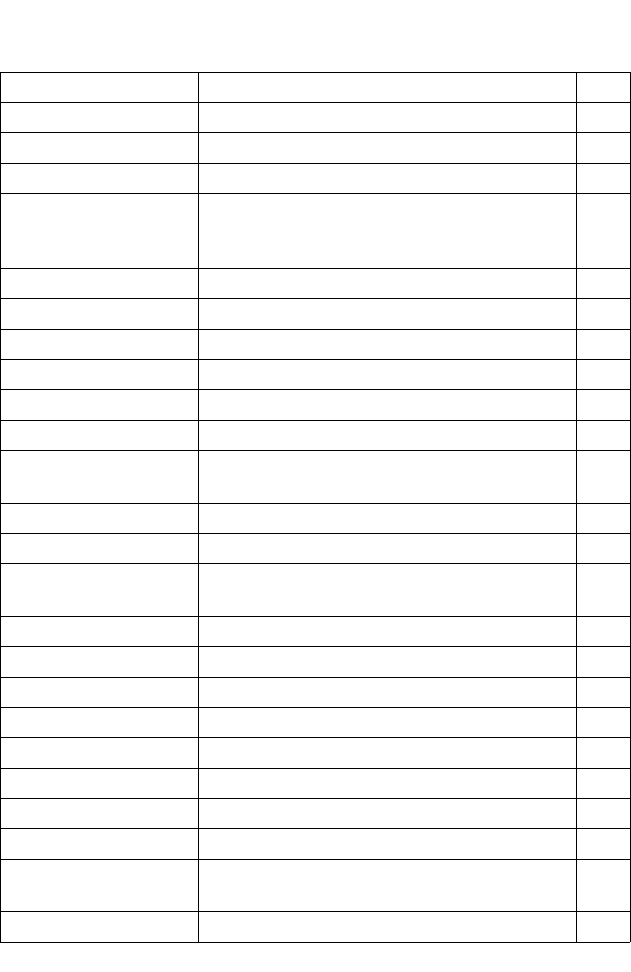
SSH
3-50
Settings
Configures Secure Shell server settings 3-55
Host-Key Settings
Generates the host key pair (public and private) 3-53
Port Security
Configures per port security, including status,
response for security breach, and maximum allowed
MAC addresses
3-56
802.1x
Port authentication 3-60
Information
Displays global configuration settings 3-61
Configuration
Configures protocol parameters 3-64
Port Configuration
Sets the authentication mode for individual ports 3-65
Statistics
Displays protocol statistics for the selected port 3-67
ACL
3-72
Configuration
Configures packet filtering based on IP or MAC
addresses
3-72
Mask Configuration
Controls the order in which ACL rules are checked 3-81
Port Binding
Binds a port to the specified ACL 3-87
IP Filter
Configures IP addresses that are allowed
management access
3-69
Port 3-89
Port Information
Displays port connection status 3-89
Trunk Information
Displays trunk connection status 3-89
Port Configuration
Configures port connection settings 3-93
Trunk Configuration
Configures trunk connection settings 3-93
Trunk Membership
Specifies ports to group into static trunks 3-97
LACP
3-96
Configuration
Allows ports to dynamically join trunks 3-99
Aggregation Port
Configures parameters for link aggregation group
members
3-101
Port Counters
Displays statistics for LACP protocol messages 3-104
Menu Description Page