Chapter 21 Remote Management
ZyWALL 2 Plus User’s Guide
363
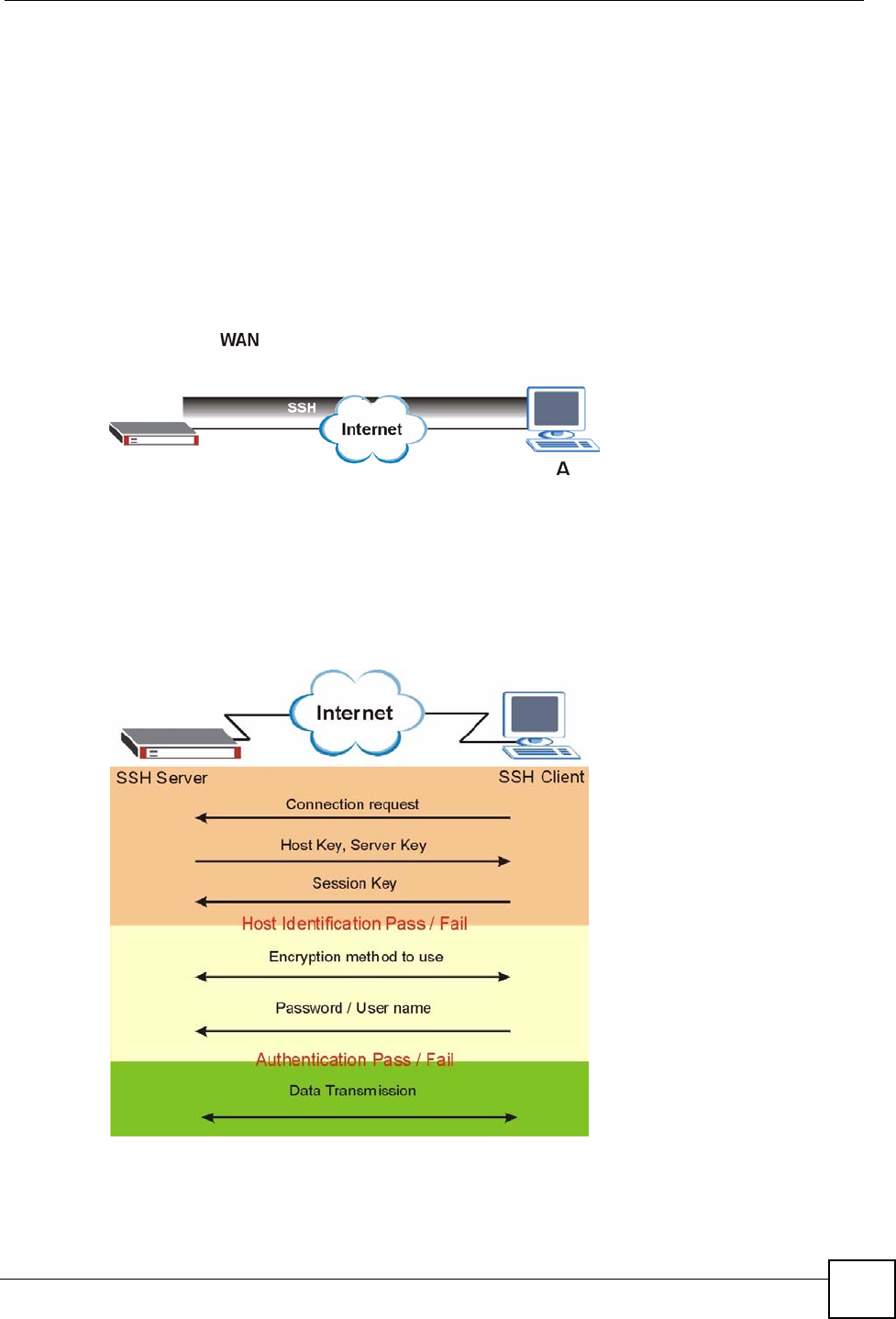
21.5 SSH
You can use SSH (Secure SHell) to securely access the ZyWALL’s SMT or command line
interface. Specify which interfaces allow SSH access and from which IP address the access
can come.
Unlike Telnet or FTP, which transmit data in plaintext (clear or unencrypted text), SSH is a
secure communication protocol that combines authentication and data encryption to provide
secure encrypted communication between two hosts over an unsecured network. In the
following figure, computer A on the Internet uses SSH to securely connect to the WAN port of
the ZyWALL for a management session.
Figure 236 SSH Communication Over the WAN Example
21.6 How SSH Works
The following table summarizes how a secure connection is established between two remote
hosts.
Figure 237 How SSH Works
1 Host Identification


















