Firewall Protection
186
ProSafe Wireless-N 8-Port Gigabit VPN Firewall FVS318N
Note these restrictions on port triggering:
• Only one computer can use a port-triggering application at any time.
• Af
ter a computer has finished using a port-triggering application, there is a short time-out
period before the application can be used by another computer. This time-out period is
required so the wireless VPN firewall can determine that the application has terminated.
Note: For additional ways of allowing inbound traffic, see Inbound Rules
(Port Forwarding) on page 130.
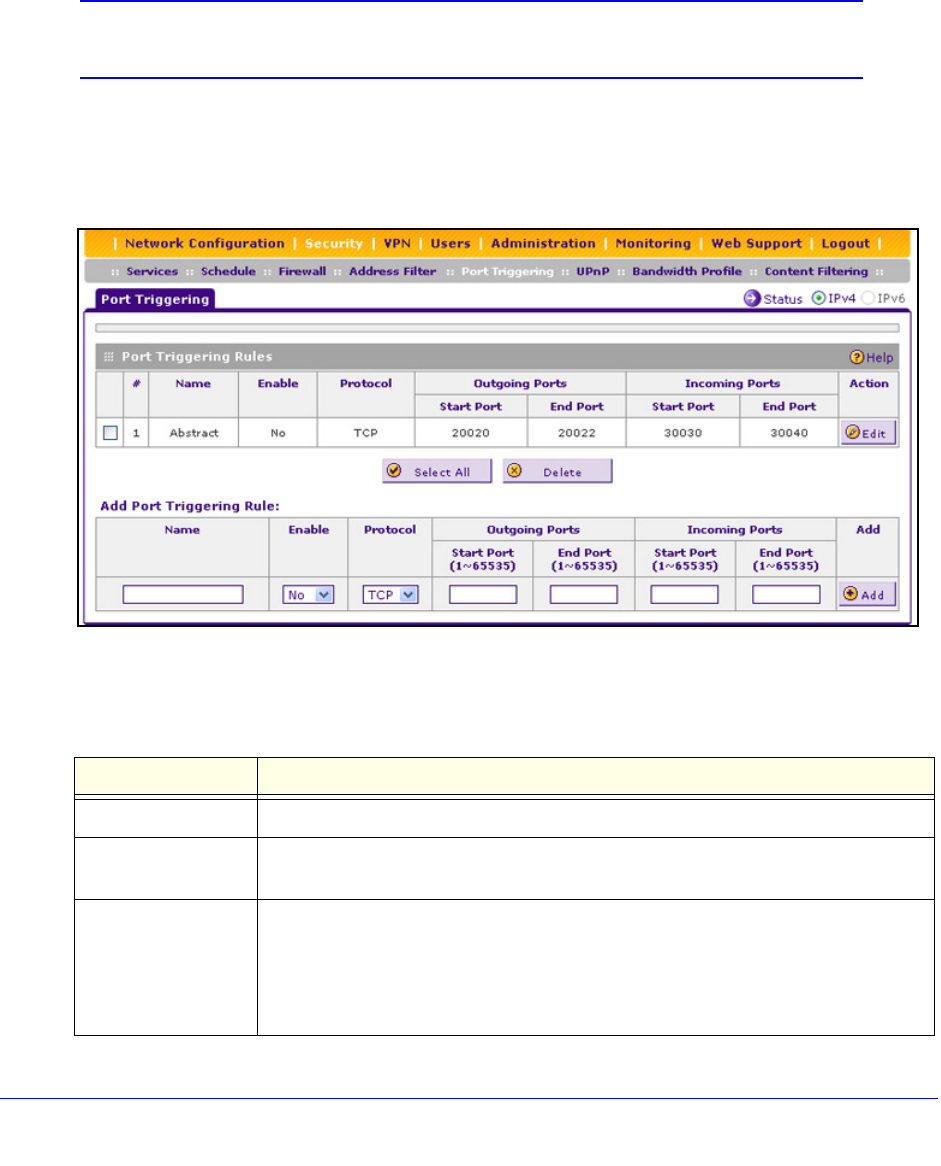
To add a port-triggering rule:
1. Select Secu
rity > Port Triggering. The Port Triggering screen displays. (The following
figure shows a rule in the Port Triggering Rule table as an example.)
Figure 101.
2. In the Add Port Triggering Rule section, enter the settings as explained in the following table:
Table 40. Port Triggering screen settings
Setting Description
Name A descriptive name of the rule for identification and management purposes.
Enable From the drop-down list, select Yes to enable the rule. (You can define a rule but not
enable it.) The default setting is No.
Protocol From the drop-down list, select the protocol to which the rule applies:
• TCP. The rule applies to an application that uses the Transmission Control
Protocol (TCP).
• UDP.
The rule applies to an application that uses the User Datagram Protocol
(UDP).


















