Virtual Private Networking Using IPSec and L2TP Connections
222
ProSafe Wireless-N 8-Port Gigabit VPN Firewall FVS318N
Local
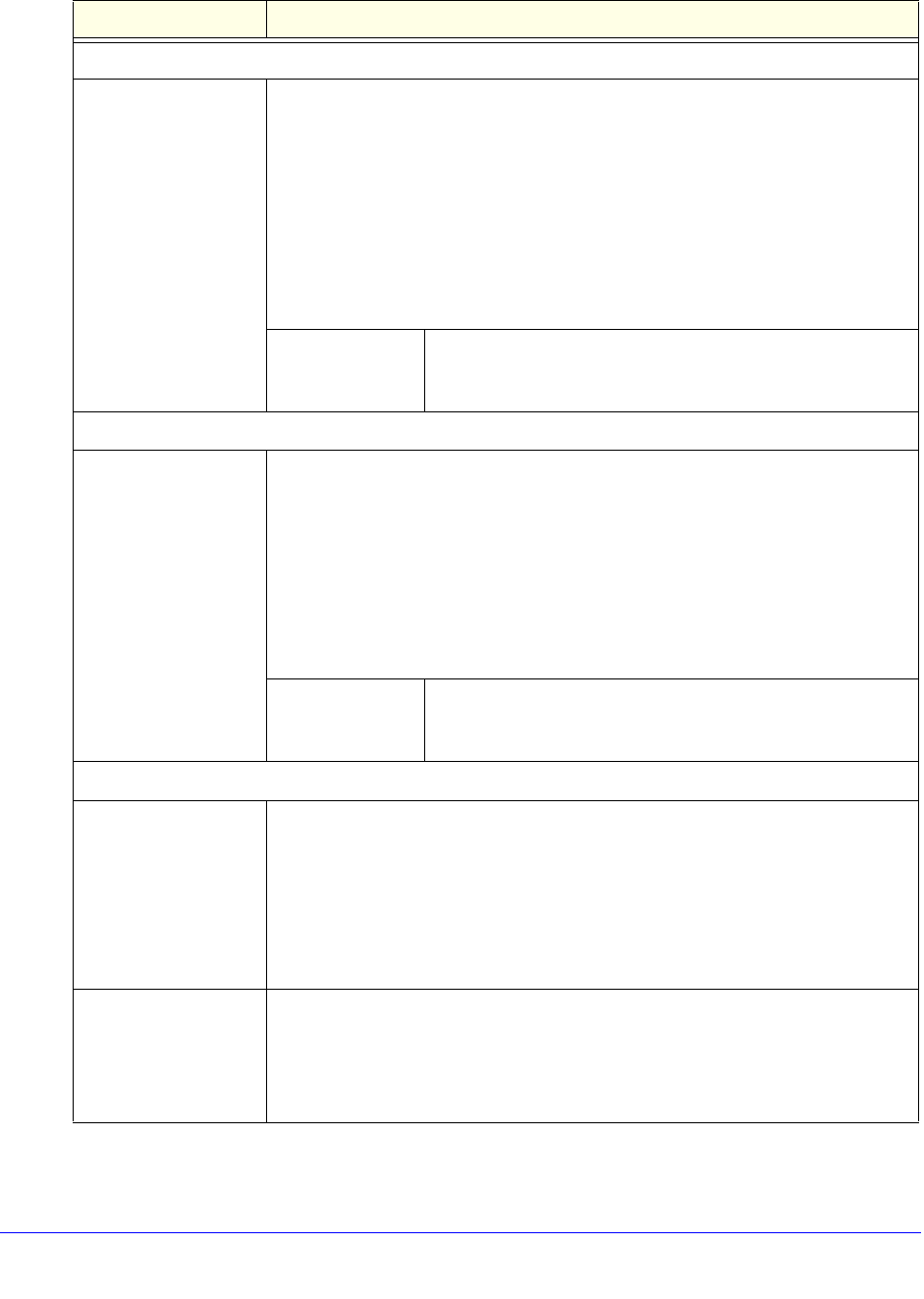
Identifier From the drop-down list, select one of the following ISAKMP identifiers to be used
by the wireless VPN firewall, and then specify the identifier in the Identifier field:
• Lo
cal Wan IP. The WAN IP address of the wireless VPN firewall. When you
select this option, the Identifier field automatically shows the IP address of the
selected WAN interface.
• FQ
DN. The Internet address for the wireless VPN firewall.
• User FQDN. The email address for a local VPN client or the wireless VPN
firewall.
• DER
ASN1 DN. A distinguished name (DN) that identifies the wireless VPN
firewall in the DER encoding and ASN.1 format.
Identifier Depending on the selection of the Identifier drop-down list,
e
nter the IP address, email address, FQDN, or distinguished
name.
Remote
Identifier From the drop-down list, select one of the fol
lowing ISAKMP identifiers to be used
by the remote endpoint, and then specify the identifier in the Identifier field:
• Remote W
an IP. The WAN IP address of the remote endpoint. When you select
this option, the Identifier field automatically shows the IP address of the selected
WAN interface.
• FQ
DN. The FQDN for a remote gateway.
• User FQDN. The email address for a remote VPN client or gateway.
• DER ASN1
DN. A distinguished name (DN) that identifies the remote endpoint
in the DER encoding and ASN.1 format.
Identifier Depending on the selection of the Identifier drop-down list,
e
nter the IP address, email address, FQDN, or distinguished
name.
IKE SA Parameters
Encryption Algorithm From the drop-down list, select one of the follo
wing five algorithms to negotiate the
security association (SA):
• DES. D
ata Encryption Standard (DES).
• 3D
ES. Triple DES. This is the default algorithm.
• AES-128. Advanced Encryption Standard (AES) with a 128-bit key size.
• AES-192. AES with a
192-bit key size.
• AES-256. AES with a
256-bit key size.
Authentication
Algorithm
From the drop-down list, select one of the following two algorithms to use in the
VPN he
ader for the authentication process:
• SHA-
1. Hash algorithm that produces a 160-bit digest. This is the default
setting.
• MD5. Hash alg
orithm that produces a 128-bit digest.
Table 51. Add IKE Policy screen settings (continued)
Setting Description


















