ProSecure Unified Threat Management (UTM) Appliance Reference Manual
7-24 Virtual Private Networking Using IPsec Connections
v1.0, January 2010
.
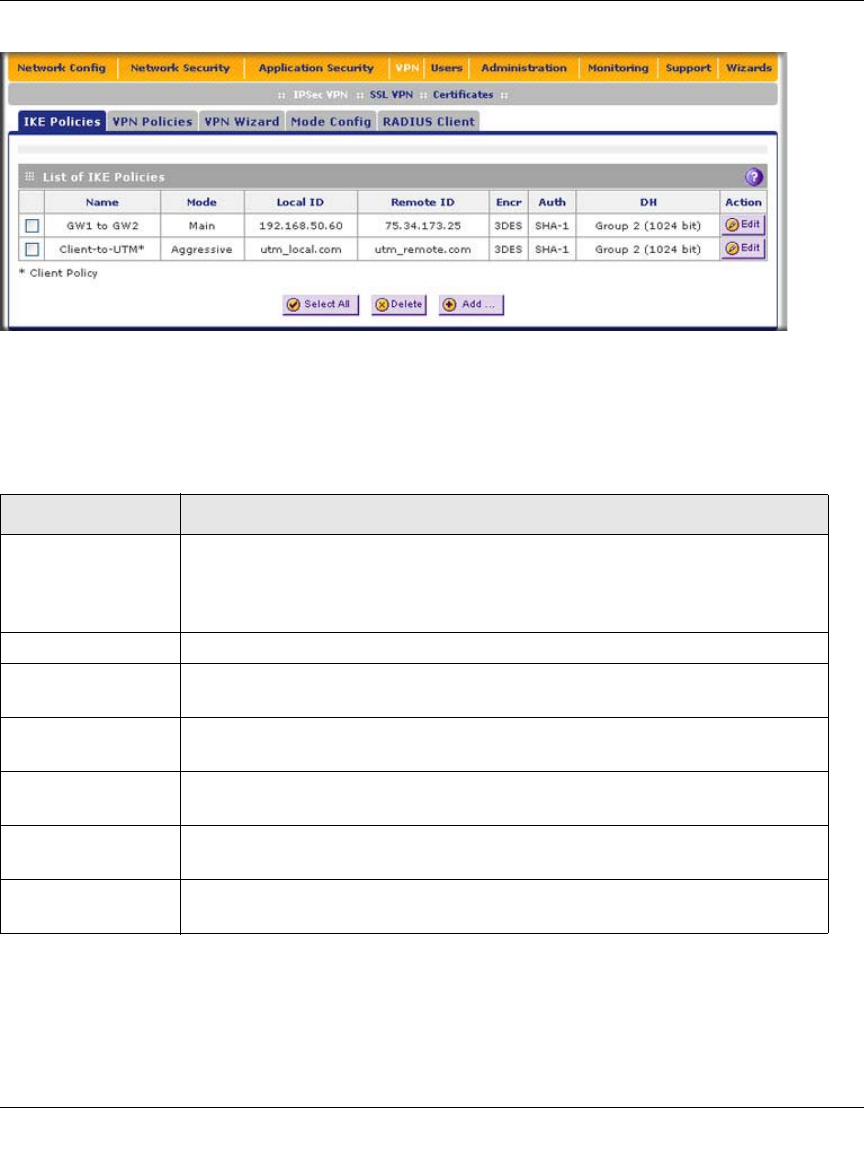
Each policy contains the data that are explained in Table 7-9 These fields are explained in more
detail in Table 7-10 on page 7-27.
To delete one or more IKE polices:
1. Select the checkbox to the left of the policy that you want to delete or click the Select All table
button to select all IKE policies.
2. Click the Delete table button.
Figure 7-20
Table 7-9. List of IKE Policies Information
Item Description (or Subfield and Description)
Name The name that identifies the IKE policy. When you use the VPN Wizard to set up
a VPN policy, an accompanying IKE policy is automatically created with the
same name that you select for the VPN policy.
Note: The name is not supplied to the remote VPN endpoint.
Mode The exchange mode: Main or Aggressive.
Local ID The IKE/ISAKMP identifier of the UTM. The remote endpoint must have this
value as its remote ID.
Remote ID The IKE/ISAKMP identifier of the remote endpoint, which must have this value
as its Local ID.
Encr The encryption algorithm that is used for the IKE security association (SA). This
setting must match the setting on the remote endpoint.
Auth The authentication algorithm that is used for the IKE SA. This setting must match
the setting on the remote endpoint.
DH The Diffie-Hellman (DH) group that is used when exchanging keys. This setting
must match the setting on the remote endpoint.


















