9-17
Catalyst 2950 and Catalyst 2955 Switch Software Configuration Guide
OL-10101-02
Chapter 9 Configuring IEEE 802.1x Port-Based Authentication
Configuring IEEE 802.1x Authentication
To disable AAA, use the no aaa new-model global configuration command. To disable IEEE 802.1x
AAA authentication, use the no aaa authentication dot1x {default | list-name} global configuration
command. To disable IEEE 802.1x AAA authorization, use the no aaa authorization global
configuration command. To disable IEEE 802.1x authentication on the switch, use the no dot1x
system-auth-control global configuration command.
This example shows how to enable AAA and IEEE 802.1x authentication on a port:
Switch# configure terminal
Switch(config)# aaa new-model
Switch(config)# aaa authentication dot1x default group radius
Switch(config)# dot1x system-auth-control
Switch(config)# interface fastethernet0/1
Switch(config-if)# switchport mode access
Switch(config-if)# dot1x port-control auto
Switch(config-if)# end
Configuring the Switch-to-RADIUS-Server Communication
RADIUS security servers are identified by their host name or IP address, host name and specific UDP
port numbers, or IP address and specific UDP port numbers. The combination of the IP address and UDP
port number creates a unique identifier, which enables RADIUS requests to be sent to multiple UDP
ports on a server at the same IP address. If two different host entries on the same RADIUS server are
configured for the same service—for example, authentication—the second host entry configured acts as
the fail-over backup to the first one. The RADIUS host entries are tried in the order that they were
configured.
Beginning in privileged EXEC mode, follow these steps to configure the RADIUS server parameters on
the switch. This procedure is required.
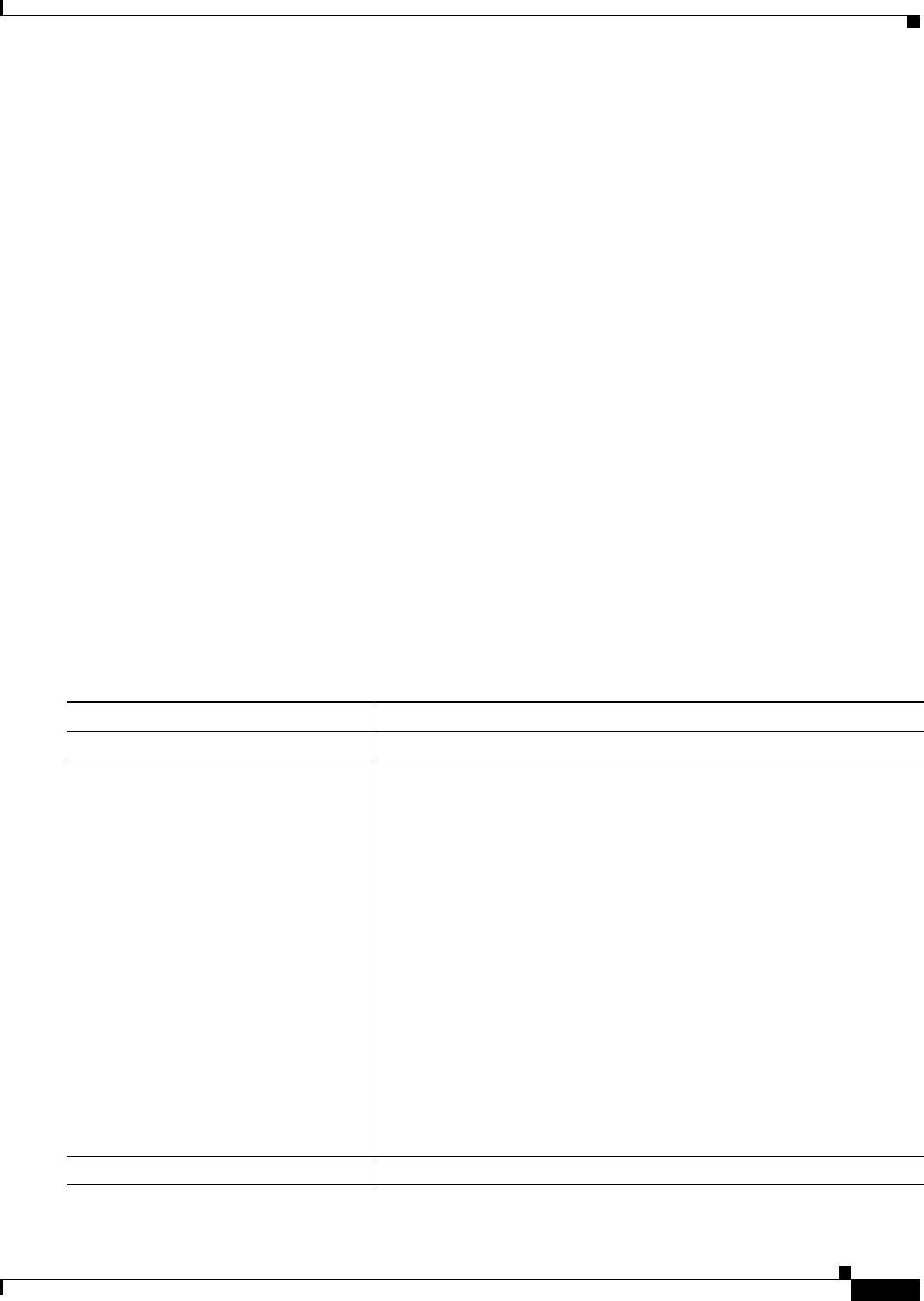
Command Purpose
Step 1
configure terminal Enter global configuration mode.
Step 2
radius-server host {hostname |
ip-address} auth-port port-number key
string
Configure the RADIUS server parameters on the switch.
For hostname | ip-address, specify the host name or IP address of the
remote RADIUS server.
For auth-port port-number, specify the UDP destination port for
authentication requests. The default is 1812.
For key string, specify the authentication and encryption key used
between the switch and the RADIUS daemon running on the RADIUS
server. The key is a text string that must match the encryption key used on
the RADIUS server.
Note Always configure the key as the last item in the radius-server
host command syntax because leading spaces are ignored, but
spaces within and at the end of the key are used. If you use spaces
in the key, do not enclose the key in quotation marks unless the
quotation marks are part of the key. This key must match the
encryption used on the RADIUS daemon.
If you want to use multiple RADIUS servers, re-enter this command.
Step 3
end Return to privileged EXEC mode.


















