38 Fortinet Inc.
NAT/Route mode with multiple external network connections Getting started
NAT/Route mode with multiple external network connections
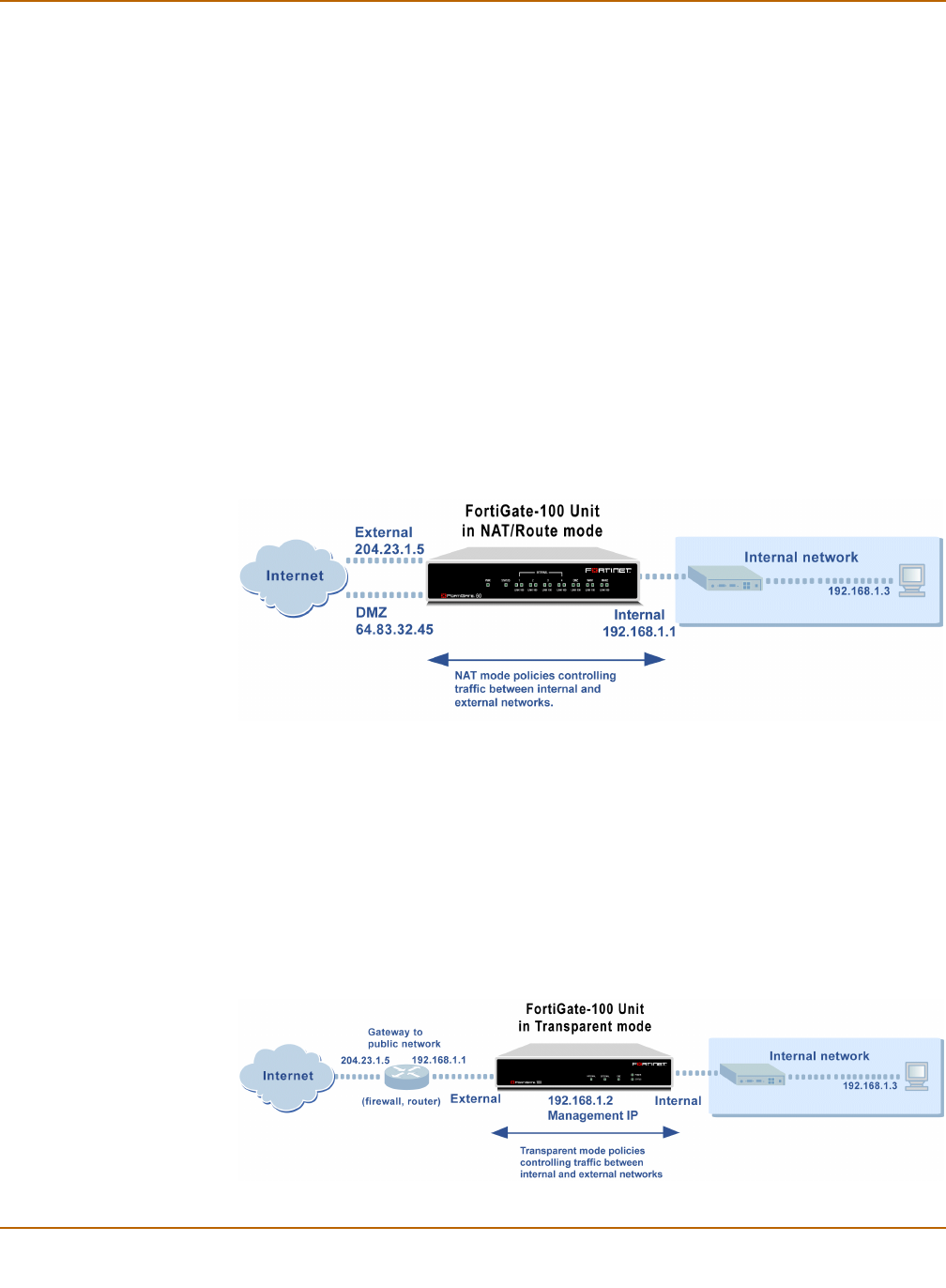
In NAT/Route mode, you can configure the FortiGate unit with multiple redundant
connections to the external network (usually the Internet). For example, you could
create the following configuration:
• External is the default interface to the external network (usually the Internet).
• DMZ is the redundant interface to the external network.
• Internal is the interface to the internal network.
You must configure routing to support redundant internet connections. Routing can be
used to automatically re-direct connections from an interface if its connection to the
external network fails.
Otherwise, security policy configuration is similar to a NAT/Route mode configuration
with a single Internet connection. You would create NAT mode policies to control traffic
flowing between the internal, private network and the external, public network (usually
the Internet). If you have multiple internal networks, such as a DMZ network in
addition to the internal, private network, you could create route mode policies for traffic
flowing between them.
Figure 5: Example NAT/Route multiple internet connection configuration
Transparent mode
In Transparent mode, the FortiGate unit is invisible to the network. Similar to a
network bridge, all of FortiGate interfaces must be on the same subnet. You only have
to configure a management IP address so that you can make configuration changes.
The management IP address is also used for antivirus and attack definition updates.
You would typically use the FortiGate unit in Transparent mode on a private network
behind an existing firewall or behind a router. The FortiGate unit performs firewalling
as well as antivirus and content scanning but not VPN.
Figure 6: Example Transparent mode network configuration


















