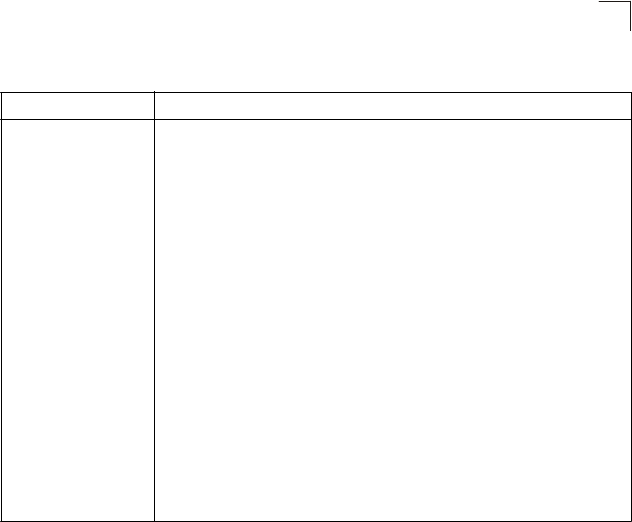
Table 25-11 show ssh - display description
(Continued)
Field Description
Encryption The encryption method is automatically negotiated between the client and server.
Options for SSHv1.5 include: DES, 3DES
Options for SSHv2.0 can include different algorithms for the client-to-server (ctos)
and server-to-client (stoc):
aes128-cbc-hmac-sha1
aes192-cbc-hmac-sha1
aes256-cbc-hmac-sha1
3des-cbc-hmac-sha1
blowfish-cbc-hmac-sha1
aes128-cbc-hmac-md5
aes192-cbc-hmac-md5
aes256-cbc-hmac-md5
3des-cbc-hmac-md5
blowfish-cbc-hmac-md5
Terminology:
DES – Data Encryption Standard (56-bit key)
3DES – Triple-DES (Uses three iterations of DES, 112-bit key)
aes – Advanced Encryption Standard (160 or 224-bit key)
blowfish – Blowfish (32-448 bit key)
cbc – cypher-block chaining
sha1 – Secure Hash Algorithm 1 (160-bit hashes)
md5 – Message Digest algorithm number 5 (128-bit hashes)
show public-key
This command shows the public key for the specified user or for the host.
Syntax
show public-key
[
user
[username]|
host
]
username – Name of an SSH user. (Range: 1-8 characters)
Default Setting
Shows all public keys.
Command Mode
Privileged Exec
Command Usage
• If no parameters are entered, all keys are displayed. If the user keyword is
entered, but no user name is specified, then the public keys for all users are
displayed.
• When an RSA key is displayed, the first field indicates the size of the host key
(e.g., 1024), the second field is the encoded public exponent (e.g., 35), and
the last string is the encoded modulus. When a DSA key is displayed, the first
field indicates that the encryption method used by SSH is based on the Digital
Signature Standard (DSS), and the last string is the encoded modulus.
25-23
Secure She l
25


















