3-27
Cisco ASA Series Firewall ASDM Configuration Guide
Chapter 3 Information About NAT (ASA 8.3 and Later)
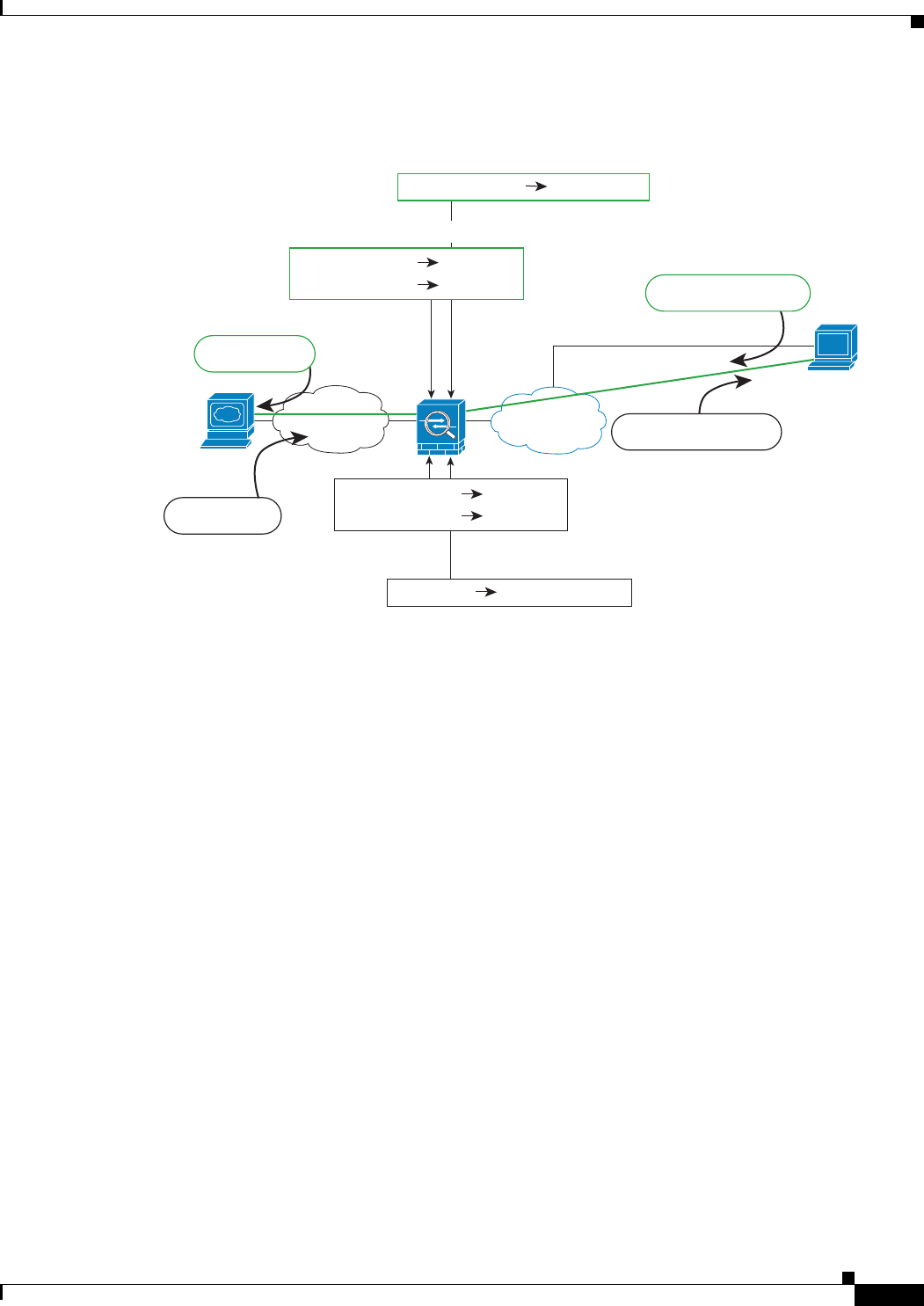
NAT for VPN
Figure 3-22 Identity NAT for VPN Clients
See the following sample NAT configuration for the above network:
! Enable hairpin for non-split-tunneled VPN client traffic:
same-security-traffic permit intra-interface
! Identify local VPN network, & perform object interface PAT when going to Internet:
object network vpn_local
subnet 10.3.3.0 255.255.255.0
nat (outside,outside) dynamic interface
! Identify inside network, & perform object interface PAT when going to Internet:
object network inside_nw
subnet 10.1.1.0 255.255.255.0
nat (inside,outside) dynamic interface
! Use twice NAT to pass traffic between the inside network and the VPN client without
! address translation (identity NAT):
nat (inside,outside) source static inside_nw inside_nw destination static vpn_local
vpn_local
NAT and Site-to-Site VPN
Figure 3-23 shows a site-to-site tunnel connecting the Boulder and San Jose offices. For traffic that you
want to go to the Internet (for example from 10.1.1.6 in Boulder to www.example.com), you need a
public IP address provided by NAT to access the Internet. The below example uses interface PAT rules.
However, for traffic that you want to go over the VPN tunnel (for example from 10.1.1.6 in Boulder to
10.2.2.78 in San Jose), you do not want to perform NAT; you need to exempt that traffic by creating an
identity NAT rule. Identity NAT simply translates an address to the same address.
VPN Client
209.165.201.10
Internet
10.1.1.6
Inside
1. SMTP request to 10.1.1.6
4. SMTP request to 10.1.1.6
2. ASA decrypts packet; src address is
now local address
10.3.3.10 209.165.201.10
7. ASA encrypts packet; dst address is now real address
Dst: 10.3.3.10
5. SMTP response to
VPN Client
Src: 10.3.3.10
Src: 209.165.201.10
8. SMTP response to
VPN Client
Dst: 209.165.201.10
6. Identity NAT
10.3.3.10
3. Identity NAT between inside and VPN Client NWs
Src: 10.3.3.10
10.1.1.6
Dst: 10.1.1.6
10.3.3.10
Dst: 10.3.3.10
10.1.1.6
Src: 10.1.1.6
10.3.3.10209.165.201.10
303463


















