Command Reference Guide Ethernet Interface Configuration Command Set
61200510L1-35E Copyright © 2005 ADTRAN 620
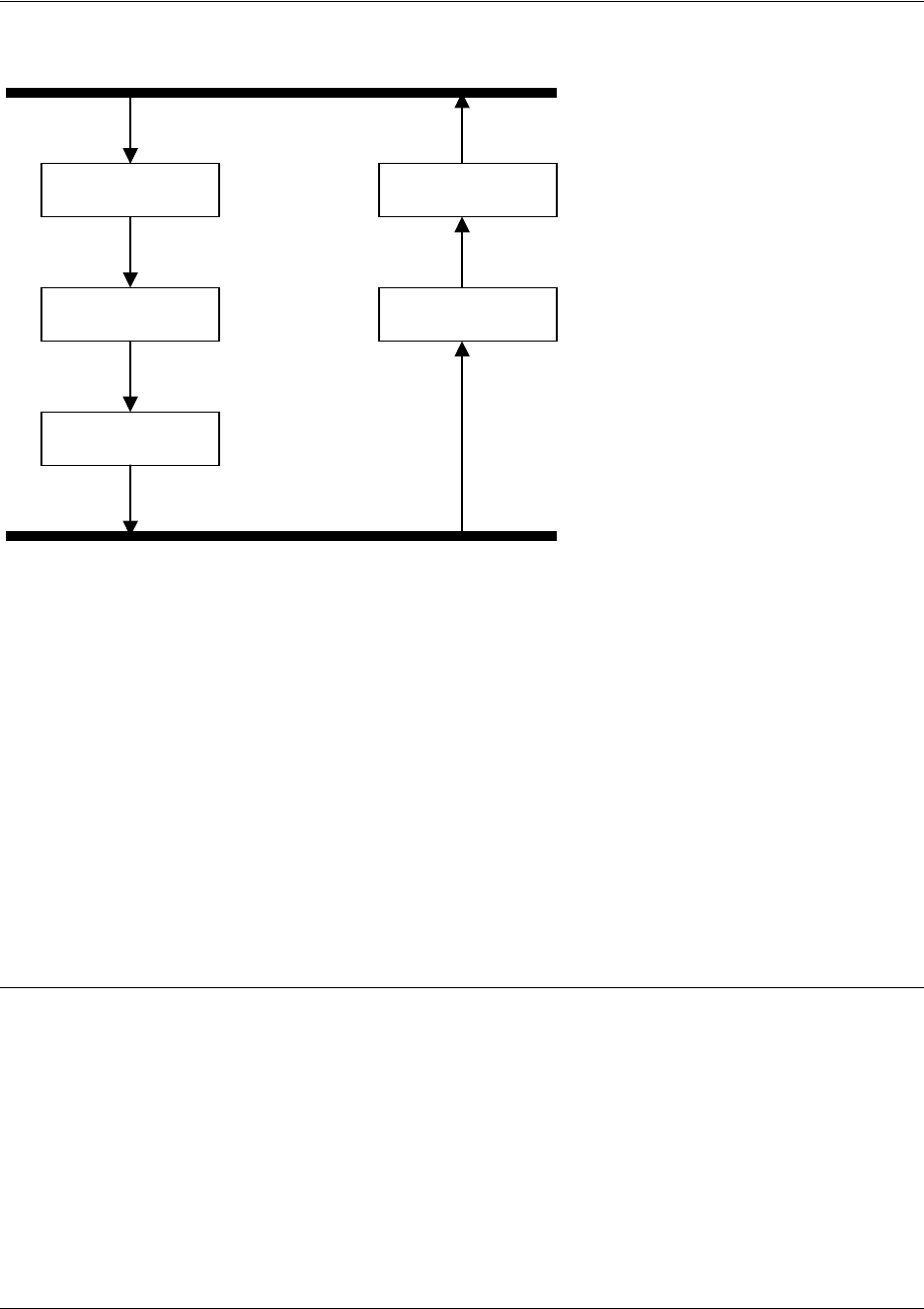
As shown in the diagram above, data coming into the product is first processed by the static filter
associated with the interface on which the data is received. This access group is a true static filter and is
available for use regardless of whether the firewall is enabled or disabled. Next (if the data is encrypted) it
is sent to the IPSec engine for decryption. The decrypted data is then processed by the stateful inspection
firewall. Therefore, given a terminating VPN tunnel, only unencrypted data is processed by the firewall.
The ACLs for a crypto map on an interface work in reverse logic to the ACLs for a policy class on an
interface. When specifying the ACLs for a crypto map, the source information is the private local side,
unencrypted source of the data. The destination information will be the far end, unencrypted destination of
the data. However, ACLs for a policy class work in reverse. The source information for the ACL in a policy
class is the far end. The destination information is the local side.
Usage Examples
The following example applies all crypto maps with the name MyMap to the Ethernet interface:
(config)#interface eth 0/1
(config-eth 0/1)#crypto map MyMap
Interfaces (Ethernet, Frame Relay, PPP, local)
Static Filter
(in)
Static Filter
(out)
IPSec
Decrypt/Discard
IPSec
Encrypt
NAT/ACP/
Firewall
Router


















